This research focused on developing of an open ICT ecosystem network design to enhance the utilization of local ICT infrastructure via network, and reduce overdependence on the Internet in the Nigerian campus network environments. A network is used to intelligently share computer infrastructure, and resources by the users involved. The research first surveyed selected tertiary institutions in Nigeria to ascertain the level of utilization, of expensive ICT facilities including, Internet bandwidth via campus LANs, and to discover the causative and prevailing bottlenecks, which hindered optimal utilization of ICT resources via campus networks. The analysis of the findings, alongside the literatures reviewed, revealed that poor network planning and design were the most prominent factors that cause underutilization of ICT resources via a WLAN, in the Nigerian University campus environments.
## I. INTRODUCTION
The current era of the COVID-19 pandemic has accelerated dependence on ICT for solving communication problems through virtual means. Virtual activities are computer networks-based, and, often Internet dependent. The 2020 COVID-19 pandemic lockdowns, escalated the awareness in virtual activities such as; eLearning, E-commerce, E-entertainment, E governance and etc. The rise can be attributed to the directive by the World Health Organization to reduce physical contact between persons to avert contracting the pandemic (World Health Organization, 2020.). The notable upsurge in virtual activities, triggered the emergence, and the implementation of several new trends in network technology advancements to balance the increasing number of users and network-based facilities around the globe.
Recent trends in computer techno fad such as, the Internet of things (IoT), and other similar technologies, have continued to stimulate the growth in intelligent ICT infrastructures. Modern devices and solutions are intelligently designed to be able to meet up with the dynamic network trend in ICT resource needs, and for resources utilization. The new trends bothers on users, manufacturers, and service providers. Unfortunately, the massive improvements on ICT infrastructure notwithstanding, the quest for the optimal performance and utilization of computer networks remains a severe issue. Since the advent of wireless LANs, which use dual-band routers for the delivery of Internet access and ICT resources via a campus LAN, quite unlike the wired LAN, ICT resource underutilization in educational network environments has escalated, and remained a reoccurring issue (DQE Communications, 2022.) and (Project Store, 2021).
At the moment, ICT and networks are inevitable tools for achieving organizations' set out goals in an educational environment. But, in many developing countries, campus wide area network deployments by the vendors of different ISPs (Internet Service Providers), are solely used for Internet access provision. Most vendors' sole interest in the deployment, is to sell Internet bandwidth, but not concerned with the utilization of the sold bandwidth, talk less of other numerous possible ICT services available for use in a client's network environment (Guimaraes, 2007).
Therefore, the scenario of over-prioritizing bandwidth as the sole resource component of a campus WLAN, causes organizations to spend huge amount of funds for only Internet access provision. Thus, lowering the quest for the utilization of a network for other possible benefits. Also, the problem of high cost disparity in designs, and the modes of internet access bandwidth delivery pose hitches for optimal utilization of ICT infrastructure in many of institution' WLANs. This is because, poor planning, and poor equipment choice, coupled with the unintelligent network design models also contribute to the low utilization of resourceful ICT infrastructures in campus WLANs. (Mahajan et al., 2005). The ISPs often deliver Internet access bandwidth to their clients via fiber-optics, or last-mile microwave radios, which are differentiated by their designs. The difference in the designs pose hiccups to the proper utilization of ICT facilities in the clients' campus WLANs. Furthermore, Interoperability issues between ISPs and clients, expose clients' WLANs to poor susceptible design that cause low utilization of networks (Hassidim et al., 2020).
Finally, bandwidth is an expensive, and difficult to save against downtimes, a feature which pose a serious concern to network administrators as they battle to optimize bandwidth usage for optimal network performance (Dajvit et al., 2015). The poor design at ISPs backbone and clients' network, facilitate network underutilization which promotes resilience to network failure (Richard, 2014). In the same manner, low utilization of bandwidth, or ICT resources available in a network spells inefficiency of administrators, in the administration of their networks. Therefore, securing optimal utilization of ICT resources via a network to attain high throughput, is among the paramount desire of every organization. This can only be achieved through a good network design (Kassim, 2013).
## II. PROBLEM STATEMENT
The daily increase in the pivotal role played the Internet and ICT in providing solutions for tertiary educational institutions cannot be overemphasized. But, the inadequacy in using ICT facilities via tertiary institutions' network of some developing countries poses serious challenges to them. Some of the major contributory problems besides the high cost of network deployment, are stated below:
1. The poor utilization of ICT infrastructure in WLAN sequel to design.
2. The failure of different Internet Service Provisions to establish a smooth handshake that will proffer optimal bandwidth utilization.
3. The poor design that can enable WLAN to deliver ICT infrastructures via campus networks
4. The low utilization of ICT infrastructure via networks resulting from heterogeneous designs.
5. The poor design framework to accommodate network or ICT infrastructural growth via campus WLAN.
## III. AIM OF STUDY
The quest to ameliorate the low utilization of ICT infrastructure via campus WLANs motivated this study, which is, the development of a 3-tier open ICT ecosystem network design (3TOIEND) to enhance the utilization of ICT infrastructures via campus WLANs and reduce the users' overdependence on bandwidth in a campus WLAN.
## IV. OBJECTIVE OF STUDY
The specific objectives set out to achieve the aim of this research are as follows:
1. The development of an intelligent network design plan for a campus area networks.
2. The development of an architecture that can integrate heterogeneous ICT components and services into an open ICT ecosystem.
3. The development of an intelligent hybrid network core layer comprising of different ISPs integrated with local ICT infrastructures.
4. The design a mesh of network aggregation and access layers using a hybrid of fiber optic and point-to-point radio links.
5. The formulation of policies that will proffer good network maintenance.
## V. LITERATURE REVIEW
### a) Network and Bandwidth Utilization
### b) Effect of Network Planning on Network Utilization
(Devajit et al., 2013) Showed that the inclusion of network topology in the design of a network proffer effective bandwidth management and overall throughput of a network, while having good network design will give a good understanding of a network, and the location of the resources, which are embedded in a network. Also,
(Scte.org, 2013) maintained that, successful management of a network and the bandwidth therein, begin with good planning and a sound design for the implementation and maintenance of a network to enable it, meet the constant dynamics experienced with modern ICT infrastructures and solutions. Consequently, (John et al., 2011) also revealed that most of the network failures in campus environments emanate from poor designs and poor utilization of the network infrastructures.
### c) Network Design and Network Utilization
Many researchers agree that network deployment must begin with an excellent network design, but none of the researchers suggested how to include available ICT infrastructures for utilization via a network. (Kassim et al., 2012) Survey on bandwidth management in LANs, WLANs, and CAMs showed that of the most networks studied were underutilized, and short-lived because of poor design and lousy bandwidth management plan. At present, network devices are continually being reengineered to become more intelligent, to improve network resource utilization for better efficiency, and performance. As such, most network designs have been improved, yet many ICT infrastructures are still underutilized via the networks. Having a good network design before deployment is necessary, and will help to identify where bottlenecks may exist, and the locations from where to collect the best data to help troubleshoot, or monitor the networks better resource utilization (Robert, 2002).
### d) Bandwidth Optimization and Network Utilization
Although, bandwidth optimization is significant when considering network utilization. Still, the components which cause over or under-dependence of a network on bandwidth in place of other ICT infrastructure, have to be considered too. As an example, (Ketan, 2002) noted that audio streaming is less concerned when considering network utilization concerning bandwidth. This is because, an audio streaming consumes less bandwidth when compared to a video streaming concerning bandwidth. (Ketan, 2002) Did not state how to improve this condition in a network design, but (Lian, 2001) and (Koller et al., 2003) agreed that high network utilization often causes serious message delays, jitters, or losses, which are caused by the large number of communicating devices in a network. Such condition, leads to degradation in performance or instability of the control loops in a network.
Also, network bandwidth utilization problems are aggravated by the popularity of wireless sensor networks, and the increase of power line transmission. Wireless sensor networks use smaller bandwidths which has higher error rates resulting from low bandwidth utilization (Lian, 2001) and (Koller et al., 2003).
It is obvious that moderate network utilization are more realisable in developed regions because of better bandwidth consumption rates. But, such moderate utilization may not be constant if the design is not taken into consideration at beginning of the network life (Xipeng, 2008). This position buttresses the importance of network design to a network's utilization. As an example, the typical utilization of a last mile broadband link is often fairly low, and less than $10\%$ efficient, because the design offer multiple tiers of broadband access speed, yet many subscribers do not sign up for the highest tier. Therefore, while it is generally thought that having more bandwidth will cause a better link utilization, better design instead does (Xipeng, 2008). Bandwidth availability can be likened to food because, having excess food does not guarantee satisfaction; likewise, a network user may consume excessive bandwidth, without achieving the required network utilization, or the network achieving optimal throughput.
### e) The ICT Ecosystem
The ICT ecosystem is a new concept that suggests ICT as a part of an expanded network that recognizes the non-technical dynamics of socioeconomic, political, and spatial concerns (Simon et al., 2018). The ecosystem concept was borrowed from biology to describe the interaction of various actors in a network environment. Accordingly, several studies within the ICT research sphere have applied the ecosystem metaphor (Xipeng, 2008). The Open ePolicy Group, also described how open ICT ecosystem have been carried out in many information technology research (Open ePolicy Group, 2005). Therefore, the thought of applying open ecosystem concept in a campus wired local area network (WLAN) environment could be rewarding, because all homogeneous and heterogeneous components within the ecosystem will handshake every network component to yield, ICT resources, and network utilization, by turning the value chain to a value ecosystem (Rafigue et al., 2012).
### f) Students Presence in Campus WLANs
A case study of selected Nigerian university students' application of the Internet for studies revealed that Nigerian undergraduate students make extensive use of the internet by relying on private, or commercial cyber cafés, which are grossly poor for studies (Okon, 2010). The students are often, not considered in the institutions' Internet infrastructural design (Okon, 2010). On the other hand, most postgraduate students who can access the Internet from campus WANs do not possess the necessary skills to utilize available ICT infrastructure via the networks for studies. In some cases, the ICT infrastructures are basically not utilized via a campus WANS (Adeleke & Emeaghara, 2016). A study on the usage of electronic resources in Nigerian university libraries showed that the ICT infrastructures, and resources are grossly underutilized (Obidike & Mole, 2015). Students are often not aware of available ICT resources, and as such, do not utilize same for studies (Mohamed, 2008). Findings from oral interviews with students in different tertiary institutions in Nigeria showed a few concerns that often compel the management, and administrators of campus networks from fully including students' presence in the institutions' networks. (Siddiquah et al., 2017) Itemized speed of computers, the Internet signal problems, virus threat issues, poor working condition of computers, load shedding, and lack of access to the Internet as the factors that deter students from utilizing campus ICT infrastructures via campus networks. (Valerie, 2018) Attributed poor wireless connectivity problems as one reasons why the students in higher education do not use campus WLAN. The poor budgetary for student presence in the campus WAN designs is also a serious contributor to ICT underutilization via the campus networks of the tertiary institutions.
### g) Conclusion on Literature Review
From the literature review, it was evident that good network design is a major prerequisite process in the life of any performance-oriented computer network, and building an ICT ecosystem which comprises of bandwidth, and ICT infrastructure in a tertiary institution's network environment will harness the accommodation, and utilization of the necessary components required by users in a campus network. Such integration, will yield optimal network performance through high ICT resource utilization. In Conclusion, no existing documented algorithm, for the design of an open ICT ecosystem integration or utilization via a campus WLAN was found in the literatures reviewed.
## VI. DESIGN METHODOLOGY
The Cisco Service-Oriented Architecture (SONA) that adopts architectural modularization, with emphasis on infrastructural considerations, and the Top-Down modular method of splitting a proposed network design into three modular tiers of core, distribution, and access layers was adopted to aid flexibility, facilitation of implementation, ease of testing, and troubleshooting of a design was adopted for the proposed design.
## VII. THE 3 TIER OPEN ICT ECOSYSTEM NETWORK DESIGN (3TOIEND)
Sequel to the findings and conclusion drawn from the literature review, a 3 (three) Tier Open ICT Ecosystem Network Design (3TOIEND) would be appropriate to curb the menace of ICT infrastructure/resources underutilization, and overdependence of only the Internet access provision in a campus network. The 3TOIEND is an intelligent network design that will provide a campus networks with the capability of adequately utilizing every available ICT resources in a network, and depending less on the Internet as the sole source for data and information in a campus WLAN and proffer optimal performance.
### a) 3TOIEND Design Algorithm
The 3TOIEND shall be achieved through the following algorithm and flowchart in Figure 1:
Step 1: Planning Campus WLAN design
Step 2: Choosing WLAN design structure and components
Step 3: Provide an Open ICT Ecosystem architecture
Step 4: Design a 3 Tier open ICT ecosystem Network
Step 5.1: Create a robust hybrid ISP open ecosystem core, test layer design
Step 5.2: Create Aggregation Layer, test layer design
Step 5.3: Create Access layer, test layer design
Step 5.4: Network Security Design
Step 6: Test the 3TOIEND design
Step 7: Implement the 3TOIEND design
Step 8: Refine design for future upgrade
### b) The 3TOIEND Algorithm Implementation
Step 1: Planning a Campus-Wide Local Area Network Design In computer science, planning is usually the first step in designing a system. Networks are expensive; therefore proper planning of a network for future developments, or upgrades is required before proceeding on the design and execution. A proper planning will enable the design to accommodate the inclusion of all the necessary requirements. In this case, the requirements included, every available ICT infrastructure and network-oriented services in a campus environment. The planning process began with gaining sufficient in-depth knowledge of the existing ICT facilities, needs, users, and network problems, which are required to be solved by the new design. Also, the planning considered the choice and viability of the platform that will be used, as well as, the available sources of Internet bandwidth subscriptions. Afterwards, the plan was tested for viability, and the test results were considered for every stage of the design process.
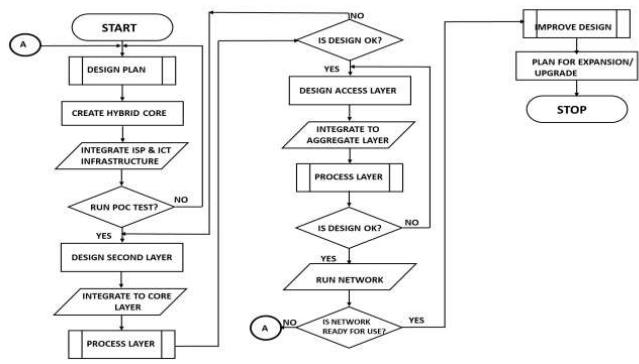 Figure 1: Flowchart for the 3TOIEND
Step 2: Choosing the WLAN Design Structure and Components
A campus network is a portion of an enterprise network infrastructure which enable users to communicate with, and use available ICT resources (CISCO, 2016). The choice of the design architecture adopted for the 3TOIEND was, the layered (hierarchy), modularity design. The choice was based on its resilience and cost effectiveness in guaranteeing ICT infrastructure, resource utilization, ease of management and performance, expansion, equipment integration, and operational compatibility. The choice of the components for the design was made open to nonproprietary vendors' equipment to evade integration-related and operational issues.
Step 3: Development of the Open ICT Ecosystem
The ICT ecosystem is a new concept that suggests ICT resources as a part of a comprehensive network platform (Simon et al., 2018). An Open ICT Ecosystem (OIE) refers to an ICT system architecture that is open to allow for the interaction, operation, and synchronization of both homogenous and heterogeneous ICT devices within a network. The open ICT ecosystem idea enabled the integration of the various hardware and software components of the ecosystem, and allow their inter-operability to create a robust resourceful network design, for optimal resource utilization.
The creation of the open ICT ecosystem began with gathering a list of ICT infrastructure, resource, and services that are required for the network design, and implementation. Future advancements and possible expansion of the network were also considered. The open ICT ecosystem was able to resolve compatibility issues by unifying the operational systems of the different components, by accommodating every available resourceful infrastructure to benefit equipment vendors and the network users. The open ICT ecosystem provided a limitless device-operational environment, and optimal resources utilization via a campus WLAN.
Step 4: Design Requirements for the 3-Tier Open ICT Ecosystem Network Architecture
A 3-Tier (Hierarchical/Tree) Network design was developed according to the flowchart in Figure1. The design comprised of the core, distribution and access layers. The design began with finding the major players for the network ecosystem, which needed to form the layers of the open ICT ecosystem. The components requirement for the open ICT ecosystem included, the Internet service providers, ICT infrastructures viz; servers, routers, converters, printers, and etc.
The following basic hardware were used in Building the 3 Tier Open ICT ecosystem Design:
1. Mikrotik cloud core multilayer router (CCR1036-12G 4s-EM).
2. Smart multilayer cloud router switch (CRS125-24G-1S-IN complete 1sfp 24 port 10/100/1000 layer 3 switch (optional).
3. Mikrotik Firewall OS, Intrusion Detection and Prevention Systems (IDS and IPS).
4. 8 core Fiber optic link for point to points secured links.
5. Netlink Ethernet media converter; 10/100/1000Base-T to 1000 Base-SX/LX.
6. Mikrotik 5.8 SXT GHz distribution radio device for Point to Point link on layer 2.
7. Mikrotik 2.4 GHz router board device for local remote access points.
8. Ubiquitous or TP Link 4G Wireless N router (to serve for access points in the access layer).
## VIII. DEVELOPMENT OF THE 3TOIEND
Building the 3TOINED was carried out in three phases viz;
Step 4.1: A. Creation of a Robust Hybrid Core Layer (RFCL) Design
The core layer design started with creating a robust, hybrid, and open ICT ecosystem at the Network Operation Center (NOC). The layer consists of an integrated Internet access service sources using a Mikrotik cloud router CCR1036-12G-4s-EM, with inbuilt firewall OS. The router was connected to a multilayer switch (Mikrotik CRS125-24G-1S-IN complete 1SFP 24 Port 10/100/1000 layer 3 switch) to produce one common output of a hybrid internet access backbone. Further integration of more ICT facilities such as, subnetworks, servers, network printer, and etc. followed. The core layer used a hybrid link comprising of a 5.8GHz Mikrotik wireless radio and a fibre optic link, which terminated with two 10/100/1000Base-T to 1000 Base-SX/LX Ethernet fibre media converter at both ends, to provide connections from the core layer to the distribution layer.
Although, both links were merged by the router to produce one output, the links remained independent of one another, and sustained their peculiar features, so that, they can be used independently if the need arises. The design and configuration of the core layer can be likened to a smart phone with multiple SIM cards, which are used for Internet access services for the phone, for seamless switching between alternatives SIM cards to constantly provide a consistent Internet access services for the phone, via any of the SIM cards.
At the end of the core layer design, the Proof of Concept (POC) design testing was carried out on the design, to confirm viability of the design before proceeding to the design the next layer.
The figure 2, presents the three layers of the design architecture and the WLAN components.
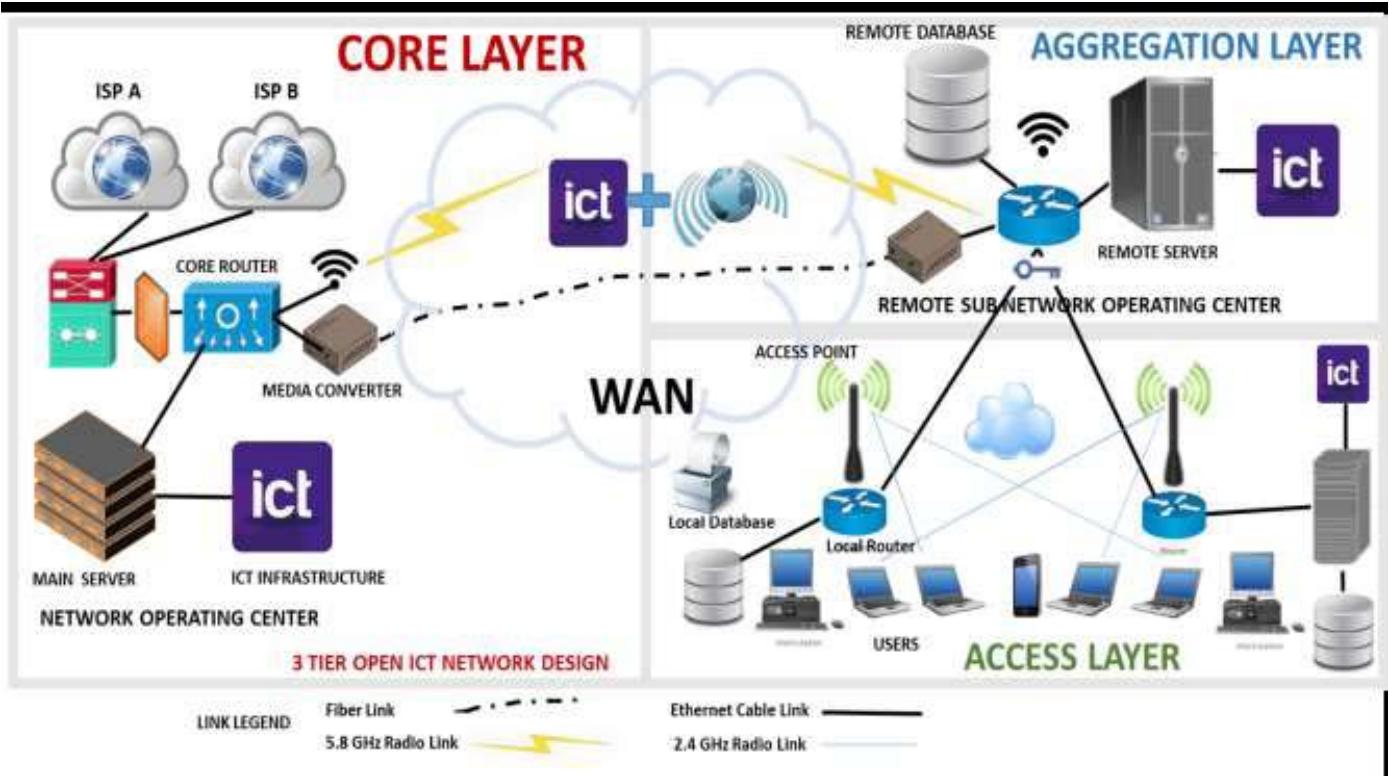 Figure 2: The 3 Tier Open ICT Network Design layout
Step 5.2: The Aggregation/ Distribution Layer Design and Implementation
The aggregation layer, which is also referred to as, the distribution layer, interface between the core layer and the access layer. The aggregation layer serves as the critical point for control and application services of the WLAN. The layer's design began with the creation of Remote Sub Network Operations Centres (RSNOC), and afterwards was linked the core layer via a hybrid link of fiber (Ethernet media converter of 10/100/1000Base-T to 1000 Base-SX/LX at both ends), and a wireless (Mikrotik 5.8GHz SXT) radio device. The duo links terminated at a router (Mikrotik router board) located at the RSNOC.
The Functional features of the Aggregation Layer: This layer was designed to perform among others, the following prominent functions:
1. The distribution of local campus ICT infrastructure to the access layer: The RSNOCs links the open ICT ecosystem infrastructure of the core center, to the meshed access layer, for the distribution of the integrated hardware and software contents of the core layer.
2. The Integration of Remote Local Hardware and Software Resources: The RSNOC serve as the integration center for ICT infrastructure and resources at remote campus locations. The aim the RSNOCs was to ensure optimal ICT resource integration, and utilization via a campus network, and to evade link redundancy. The Local contents at the RSNOCs included; faculty and departmental libraries, expensive hardware; such as network printers and scanners; local databases containing digitized student forms, lecture materials; and other
similar materials. The integration of the ICT resources at the RSNOCs, yielded a robust mesh of resourceful hardware and soft contents that is accessible to users via a campus WLAN, and increased the utilization of the robust open ICT ecosystem shown in figure 2.
3. The Utilization of the WLAN login page for news and information dissemination: The design used the local network Security Set Identifier (SSID) of the RSNOC access points, to provide the local NOC's name alongside a short message. The network login page layout was designed to use a part of the page layout, for posting institution's news headlines, and other vital information as shown in figure 3. The content of the login page is subject to updates, regularly from the server at the NOC. Network-users will be able to access News, information, and campus updates by merely connecting to the network Wi-Fi's, SSID login page, and get the necessary information, without logging into WLAN, or using the WLAN's bandwidth data.
4. The Provision Remote Second Security Layer (RSSL): The distribution layer was designed to provide a second layer security at the RSNOCs, by using the Mikrotik router board's operating system. The Mikrotik router board's configuration, provided monitoring, filtering, and firewall services as shown in Figure 2.
5. The Inclusion of Student-Users' Presence on the Network: Students comprises a larger population of any tertiary institution, yet their participation is often, not properly captured, or accommodated in most campus network designs. Thus, denying students from extensive use of campus networks, and the underlying ICT infrastructures which are leveraged therein. In order to improve student-users' presence
in a campus WLAN, and to improve resource and network utilization, the design included the following features at the distribution layer:
i. The Creation of Students' Layer in the Network Design: The student layer of the design made it possible, for the integration of student-related services such as; link for uploaded and download of local forms for students' using Wi-Fi-enabled devices, CBT solutions facilities, and games into the ICT ecosystem, which is accessible via the campus network. Adding students' presence-oriented services, and needs in the design caused more local network traffic, and higher utilization of the robust ICT infrastructure available on the network.
ii. The Integration of EGranary/ Digital Library Server(s) to the Design: The design also gave room for the integration of robust local research infrastructural tools, like the EGranary server (Internet in a Box), digital library servers, and database information systems servers, to further enrich the open ICT ecosystem design. The provision of these robust academic materials, which are needed, and accessible by students via a local campus WLAN in the design, grossly reduced the overdependence on the Internet access service of a network. Also, the integration of aforementioned resources to the ecosystem, caused notable reduction of Internet traffic, but increased the local WLAN traffic, because the resources provided alternatives to the Internet resources needed. Furthermore, the integrations grossly reduced bandwidth usage and wastage, to proffer more utilization of the local resources present in a local campus network.
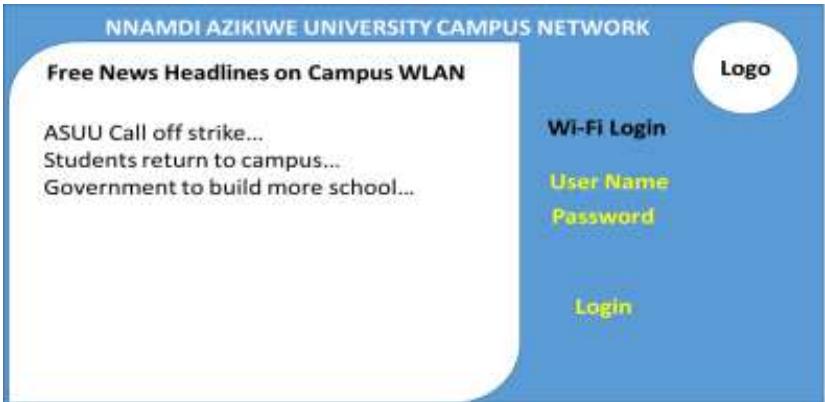 Figure 3: The Wi-Fi Login Page Designed to Hold News Headlines
### a) Implementation of the Mesh Access Layer Design
At the periphery of every network lies the access layer. The access layer provides the initial connectivity between the user devices and, a network, through the aggregation layer. The designof the access layer comprise of a mesh of Mikrotik router boards, wireless routers, and other ubiquity devices for delivering access to local open ICT ecosystem contents to users, via a local campus network. The meshed access layer serve the critical-mission clients, general-purpose clients, and the mobile clients, by cable, or wireless connections. The design made provision for the further integration of
available services, and ICT infrastructure to a network. Also, the design made provisions for free Wi-Fi clusters at different locations within a campus. The students can utilize a filtered Internet access remotely via a campus WLAN, at the designate free-Internet access locations. The access layer design and implementation were successfully tested using the network ready for use (NRFU) testing tools to mark the end of the 3 Tier Open ICT Ecosystem Network Design (3TOIEND), and implementation.
### b) Network Security Design
A network design will be incomplete without the development of basic security measures put in place to prevent intrusion and consequent failure of the design. The OSI layer 3 security devices, and software were used to checkmate network intrusion and detection, and to enhance intrusion prevention for the defence, and optimization of the 3TOIEND. The Mikrotik hardware and software, were properly configure to monitor all connections and their content. Also, operational and maintenance policies for the users in a campus network environment were listed, and formulated. Institution's management are expected to provide the access rights and privileges applicable to their network to curb unauthorised access and usage.
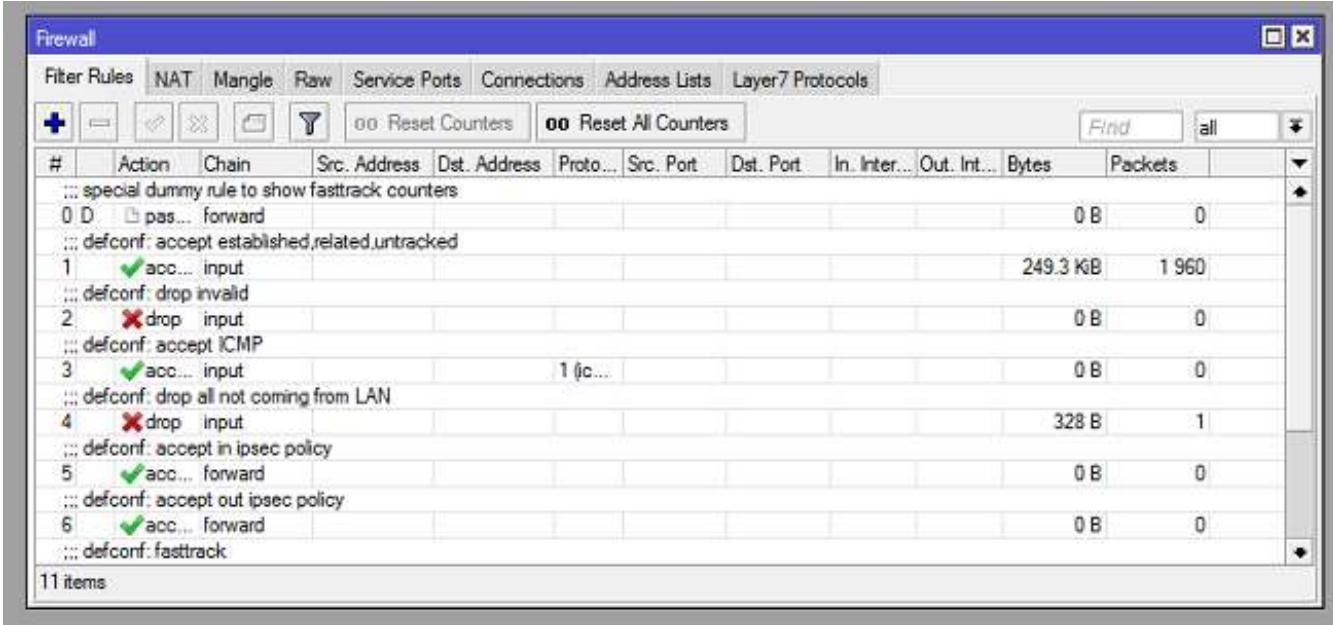 Figure 4: Mikrotik firewall setup
#### Step 6: Campus Wlan Management Policies Development
Efficient utilization and optimal throughput are the required goals of every network success. Successfully managing any network to deliver, will the required design goals to yield optimum throughput implies setting good management policies as stated in network design algorithm.
### c) Curbing Security and Safety Concerns at the Access Layer
Network security architects (NSA) are responsible for analysing network data and systems to select the most appropriate control mechanism for the security required in a network. A security architect will also have a hand in selecting software and hardware usage in a network to control system. Finally, for adequate maintenance of a network performance and utilization, the following concerns must be considered for address while formulating the network design policy:
- $\checkmark$ Access point levels security
- ✓ Network usage monitoring
- ✓ Scale usage of a network
- Checkmate authentic user qualified to access a network
- Checkmate intrusion into to a network
- Monitor abuse of bandwidth
- ✓ Monitor abuse of privileges
- $\checkmark$ ICT resource access control
## IX. BENEFITS OF THE 3TIER OPEN ICT ECOSYSTEM NETWORK DESIGN (3TOIEND)
After the design and implementation, the 3TOIEND design was able to render the following services among others:
a. Provision VOIP (Voice over Internet Protocol) - VOIP service can be configured to run on the network, so that users can leverage the WLAN to make free calls through a network with, or without connecting to the Internet. Optimal performance of this feature require some additional devices and configurations.
b. The integration of local resources - The 3TOIEND WLAN design offer very robust services beyond the distribution of Internet access. The Implementation an open ICT ecosystem design, positions a network to integrate every local ICT infrastructure in a campus WLAN for adequate utilization.
c. Ease of network expansion- The design is intelligent enough to accommodate future network expansion of any extent, and at any required time. An expansion may include but not be limited to;
1. An Indoor and outdoor equipment expansions
2. The introduction of a new ICT infrastructure
3. A User-based expansion
4. A network device expansion
5. The Internet bandwidth increments
6. A general network expansion
d. On the Go News flash Service on the Login Page: This peculiar feature of having a campus news update on login page, showcases the robust features of the 3TOIEND. Connecting to a Wi-Fi is usually automatic on every Wi-Fi-enabled device. Thus, using a Wi-Fi login page to provide a campus' news updates, means that, users can get a campus news, and information, without having to waste a ampus' Internet bandwidth, but by just securing a connection to a campus WLAN,.
Step 7: Testing the Design and Results Discussion
Network design testing is essential, because networks are hard to build correctly. A network design may appear subtle, whereas, there may be bugs therein that may require intermittent attention. A network design testing as an investigation, conducted to provide network Stakeholder (s) with information about the quality of the product, service, or design of a proposed network. A network design testing is similar to a software design testing and aims to ensure that a network's implementation, works as designed. The flowchart in figure 1, included design testing after each step of the design. (CISCO, 2012) Recommended two types of network design tests viz; firstly, a proof of concept testing (POC) is required, to ensure that a newly invented design, or to test if a design technology will work as expected in the context of the design. Afterwards, the Network ready for use testing (NRFU) method follows immediately. The NRFU is typically executed at the last step of a design, to certify that the design is ready to carry expected traffic.
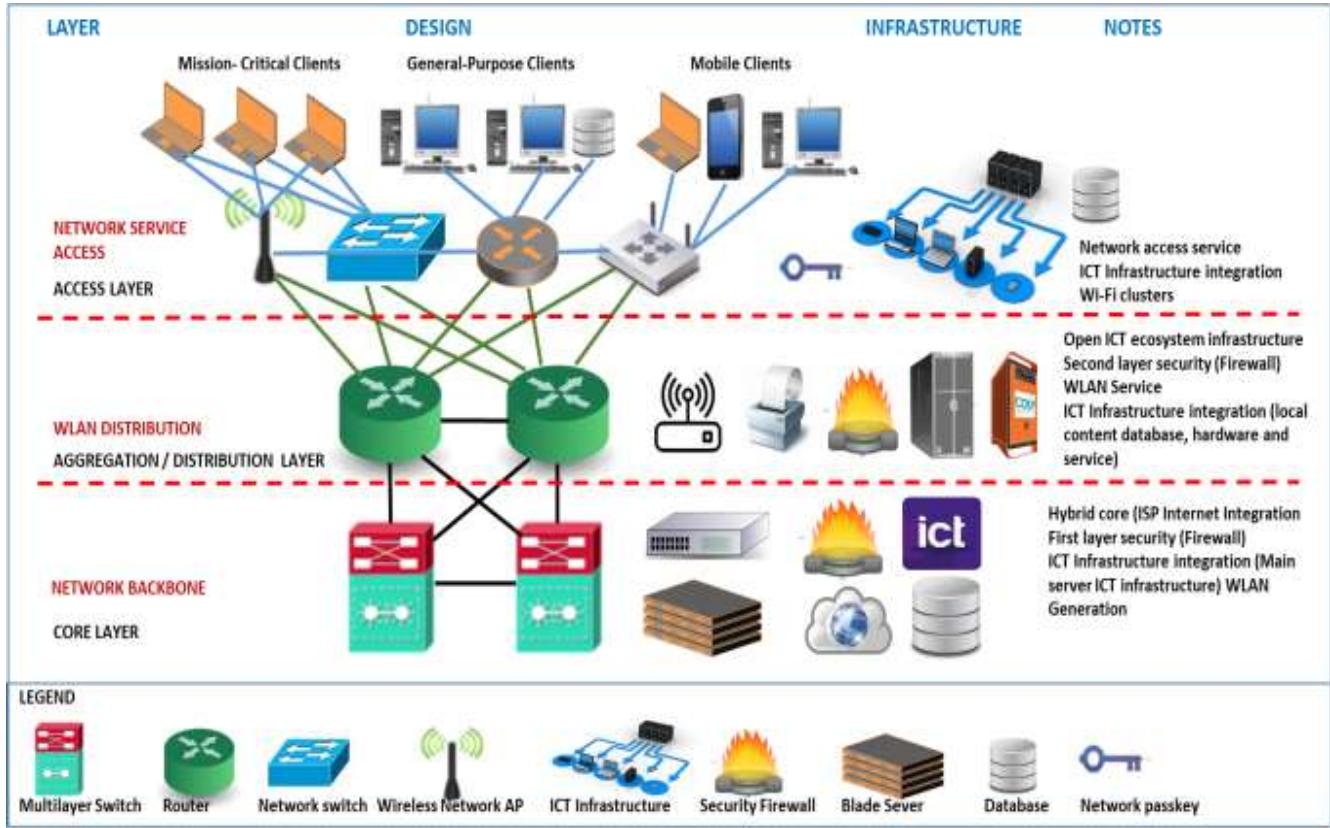 Figure 5: The 3-Tier Open ICT Ecosystem Network Design (3TOIEND) Model
### a) Design Testing Results
The design testing results are as follows:
i. A verification that the design meets desired technical goals.
ii. The validation of the WAN and LAN technology, and the device selection for the design.
iii. The identification of any possible problem area or connectivity issues.
Table 1: 3TOIEND testing parameters
Comparison tests were carried out using various parameters to compare the 3TOIEND, with the previously existing campus WLAN design at Nnamdi Azikiwe University Awka campus. The table below, shows the parametric data used to test the new 3TOIEND against the previously existing WLAN design at the Nnamdi Azikiwe University Awka. The results of the tests are presented in the column chart of figure 6.
Table 1
<table><tr><td>Design Name</td><td>Resource Coverage</td><td>Resource Utilization</td><td>Network Stability</td><td>Student's Presence</td><td>Network Redundancy</td></tr><tr><td>Other Designs</td><td>85</td><td>70</td><td>65</td><td>83</td><td>25</td></tr><tr><td>3TOIEND</td><td>40</td><td>45</td><td>50</td><td>38</td><td>55</td></tr></table>
## X. 4.0 DISCUSSION OF TEST RESULTS AND DESIGN VALIDATION
As shown in table 1, different types of tests were carried out to test the efficacy of the 3TOIEND. A POC testing was carried out, to certify the design plan, at the same time, the NRFU test was performed to test the bandwidth, and the open ICT ecosystem's infrastructures utilization via a network. The 3TOIEND model yielded amazing test results. Statistical tools were further used to carry out comparison tests, between the new model's performance, and an existing model's performance. The test applied the following parameters; resource coverage, resources utilization, network stability, student's presence, and network redundancy. Eventually, the comparison test results, which are summarized in the bar chart of figure 6 validated the 3TOIEND model.
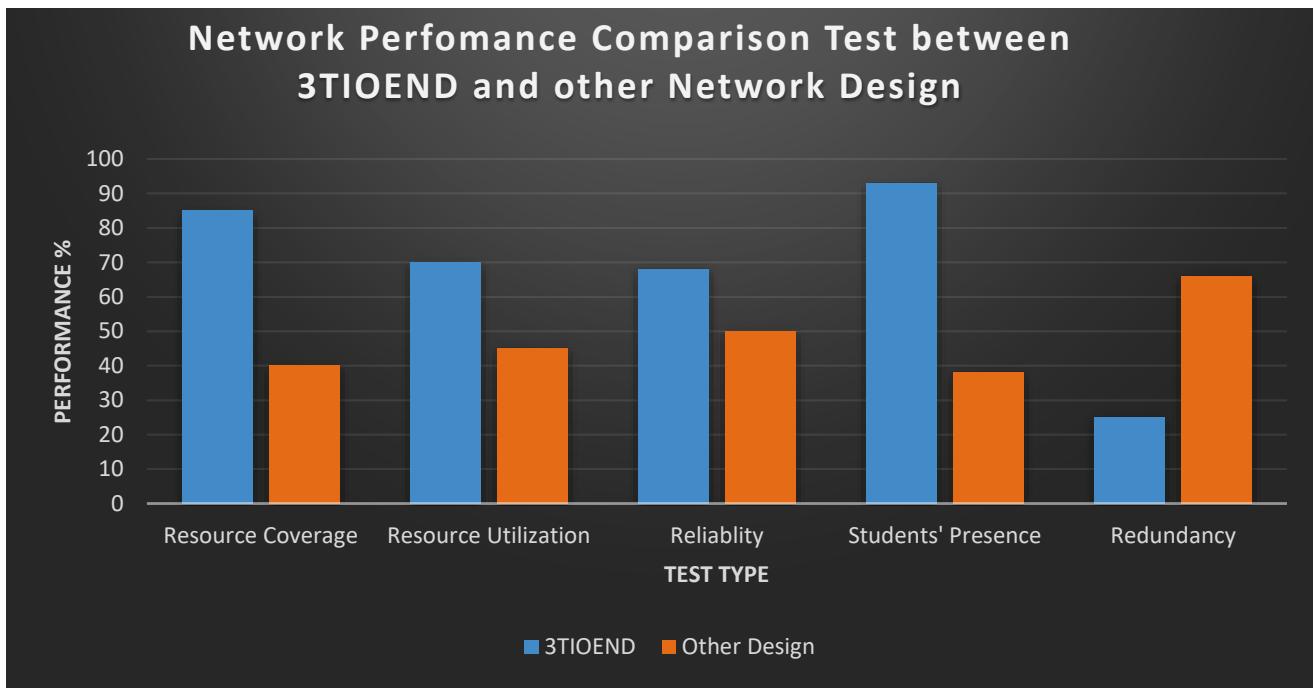 Figure 6: Network Performance Comparison Test between 3TOIEND and other Network Design
## XI. CONCLUSION
In conclusion, the 3-Tier Open ICT Ecosystem Network Design (3TOIEND) is intelligent, robust, and easy to implement. The 3TOIEND was implemented at Nnamdi Azikiwe University Awka, Anambra State, Nigeria, and the intelligent design proffered an enhanced, value-added, and sustainable network, which optimally, utilized the ICT resources available in the Open ICT Ecosystem, via the Network. The
Also, the implementation of the design at Nnamdi Azikiwe University, enable the campus WLAN, to satisfactorily utilized the available bandwidth subscription in the campus ICT ecosystem, and created a very noticeable network optimization; reduced bandwidth wastage; evaded bandwidth abuse; drastic reduction in network and resource redundancy; optimal utilization of available local ICT resources via the campus WLAN; a drastic reduction in the overdependence on Internet; and increased network reliability.
Generating HTML Viewer...
References
18 Cites in Article
Dare Adeleke,Emeaghara Samuel,Nkechi Evelyn (2016). Relationship between information Literacy and Use of Electronic Information Resources by Post graduate Students of the University of Ibadan, DigitalCommons @University of Nebraska -Lincoln.
No ethics committee approval was required for this article type.
Data Availability
Not applicable for this article.
How to Cite This Article
Ikechukwu Innocent Umeh PhD. 2026. \u201cA 3 Tier Open ICT Ecosystem Network Design (3TOIEND) to Enhance Utilization of Local ICT Infrastructure VIA Campus WLAN\u201d. Global Journal of Computer Science and Technology - E: Network, Web & Security GJCST-E Volume 22 (GJCST Volume 22 Issue E2).
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.