The adoption of virtual reality (VR) and augmented reality (AR) headsets in futuristic and science fiction has made it possible for the Metaverse to exist as a single, universal, immersive virtual universe. By extending technology outside of our physical reality, the Metaverse alters the human experience. The four categories we use to categorize metaverse definitions are environment, interface, interaction, and social value. Currently, it is unclear what the metaverse’s structure and elements are. A cybersecurity framework for these devices is necessary as the world grows more interconnected and immersive technologies are increasingly widely used in business, government, and consumer markets. Used was a literature review. The goal of the study is to create a cybersecurity model for a Roblox-based Metaverse architecture framework that can be applied to internationalization, the value chain of education, and the delivery of online and e-learning education. The research is conducted using the Interpretivist Paradigm.
## I. INTRODUCTION
The Metaverse is a virtual iteration of the Internet as a single, universal, immersive virtual world made possible by the use of virtual reality (VR) and augmented reality (AR) headsets in futuristic and science fiction. The Metaverse modifies the human experience by extending technology beyond our physical reality. The Metaverse is essentially a network of 3D virtual worlds focused on social connections, potentially exposing students to inappropriate content. Roblox is an open-source platform that can be used for online education to enable interactive 3D virtual environments in physical and online classrooms, with some basic cybersecurity mechanisms. Metaverse is a combination of virtual reality (VR), augmented reality (AR), mixed reality (MR), blockchain, web3, cryptocurrencies, social media, etc. Metaverse provides users with a multilingual experience, which is a key requirement for successful internationalization that breaks down language barriers and enables easier and more affordable exchange programs. The metaverse has many advantages in science that outweigh disadvantages such as physical limitations when working with VR and AR. Developing a Roblox-based Metaverse architecture framework is worth investing in promoting internationalization and the education value chain. The Metaverse can be seen as the channel of the future for online /e-learning education. Internationalization is the extension of the international, cross-cultural, or global aspects of post-secondary education to its objectives and functions, in order to improve the quality of teaching and research for all students and staff as well as making meaningful contributions to the society. It is a deliberate process that we incorporate into our offerings [1].
Internationalization is "a cross-border, cross-cultural approach to the purpose, function and delivery of post-secondary education in order to improve and enhance the quality of teaching and research for all scholars and staff, and to integrate inter- or global dimensions to society" [1]. This description reflects the increased mindfulness that internationalisation has to come more inclusive and less potty by not fastening generally on mobility but further on the class and literacy out-comes. The internationalization of higher education (IoHE) has been influenced by the globalisation of our economies and societies and the increased significance of knowledge. IoHE is driven by a dynam-dynamic and constantly evolving combination of political, profitable, socio-cultural cultural and academic dimensions. These motives take different forms and confines in the different regions and countries, and in institutions and their programmes. Internationalization is primarily motivated by the increased significance of reputation (frequently symbolised by rankings), visibility and competitiveness; the competition for talented scholars and scholars; short-term and/ or long- term profitable earnings; demographic considerations; and the focus on employability and social engagement. Some of the key recommendations for internationalization include the following:
Address the challenges of imbalances in credit and degree mobility and inter-institutional cooperation that arise from major differences in higher education systems, processes and funding.
1. Recognize the growing popularity of internships and build options to combine internships with language and cultural training and study abroad.
2. Support the critical role of academic and administrative staff in advancing internationalization of higher education (IoHE).
3. Promote greater cooperation between higher education and industry in relation to student and staff mobility.
4. Pay more attention to the importance of "internationalization at home" and integrate international and intercultural learning outcomes into the curriculum of all students.
5. Remove barriers that prevent joint strength development.
6. Develop innovative models of digital and blended learning as tools to complement IoHE.
7. Direct IoHE towards internationalization at other educational levels (primary, secondary, vocational, adult).
8. Promote bilingual and multilingual learning in primary and secondary education as a basis for diversity-based language policy.
9. To increase opportunities and synergies, remove obstacles to internationalization of research and education at all levels.
Rodoff classified the metaverse into seven layers: infrastructure, human interface, decentralization, social computing, the creator economy, discovery, and experience [2]. The metaverse can be successfully used in E-Learning as a solution for subjects that rely entirely on convergence and cannot be taught online or through distance learning, such as medical and engineering courses. Although there are many different types of E-Learning environments, metaverse-based systems can also be used to provide safe and efficient environments for education and business by utilizing virtual reality technologies and continuously researching and attempting to expand learning experiences [2]. As a result, all known learning systems will rely on the virtual learning environment in the metaverse (VLE). The metaverse also incorporates the Internet, web technologies, and virtual reality. The Metaverse roadmap, according to [2], is divided into four sections: augmented reality, life logging, mirror worlds, and virtual worlds. A roadmap of this type can be divided into four dimensions: external, extended, intimate, and simulative [2], with specific techniques such as content editing, smart devices, VR, AR, blockchain, digital twin, XR, cloud computing, and avatars being used in various proportions.
### a) Background
One of the major expectations and focuses of Industry 4.0, the architecture of the Fourth Industrial Revolution, is to connect the digital/cyber/virtual world with the physical world, hence the emphasis on cyberphysical systems. Virtual and augmented reality can play a role in the early stages of true business transformation, where optimization and productivity gains (quantity, quality, speed, and flexibility) are more important than late stages. Augmented Reality (AR) is a digitally enhanced version of the real physical world that uses technology to deliver digital visuals, sounds, or other sensory stimuli. Augmented Reality (AR) enhances your surroundings by incorporating digital elements into your live view, which is frequently accomplished through the use of your smartphone's camera. Augmented reality experiences include Snapchat lenses and the game Pokemon Go. Augmented reality can be used by retailers and other businesses to promote their products and services, launch novel marketing campaigns, and collect unique user data. Unlike virtual reality, which creates its own cyber environment, augmented reality simply adds to what is already there. Virtual Reality (VR) refers to a completely immersive experience in which the physical world is absent. VR immerses people in experiences, often using much more expensive technologies such as headsets. As a result, virtual reality (VR) is a fully immersive experience that simulates the real world.
Users of VR headsets like the HTC Vive, Oculus Rift, and Google Cardboard can experience both real-world and fantastical settings, such as being in the center of a noisy penguin colony or riding a dragon. Contrarily, augmented reality often uses a real-world view of something (such as a mobile phone camera) as the basis before projecting or pasting the image onto a screen or viewer. Table 1 below provides an illustration of how the distinction between VR and AR depends on the device you desire and the experience itself.
Table 1: Difference between AR and VR
<table><tr><td>Augmented Reality (AR)</td><td>Virtual Reality (VR)</td></tr><tr><td>AR uses a real-world environment</td><td>VR is completely virtual</td></tr><tr><td>AR users can control their presence in the real world</td><td>VR users are controlled by the system</td></tr><tr><td>AR can be accessed with a smartphone</td><td>VR requires a headset device</td></tr><tr><td>AR augments both virtual and real worlds</td><td>VR only augments fictional reality</td></tr><tr><td>AR enables individualized learning and improves the learning process</td><td>VR enables immersive learning in an interactive environment. The education sector will benefit from these new opportunities.</td></tr><tr><td>AR offers a wide range of applications that are constantly being improved, and can increase accuracy and efficiency</td><td>VR users can explore all facets of the virtual world.</td></tr><tr><td>Experience and knowledge can be shared over long distances</td><td>Experience is not easily shareable.</td></tr></table>
We must first employ sensors and cameras to acquire data about the user's actual surroundings in order to develop AR. In order to generate immersive interactions, realistic augmented reality also needs powerful computation to analyze inputs like acceleration, location, pitch, and depth in real time. The use of projection allows augmented reality devices to add a digital rendering to the environment after gathering data from the actual world. Future educational systems will primarily use virtual learning environments. It is crucial to keep such a structure in place to protect future generations. In order to create a future e-learning environment and offer a thorough and efficient educational process, it is crucial to integrate new and difficult technology [2].
This study investigates how the metaverse functions and what unique technologies are there in it.
There is no agreement on the layers, the number of levels they should have, or what should be included in one layer and omitted from another despite the fact that numerous scholars have proposed layers for the metaverse framework or architecture. Numerous systems that operate within or make use of the metaverse have also been proposed, although they are unable to fully benefit from the metaverse's advantages. The suggested virtual learning environment ELEM, which was modified from the Metaverse framework used by [2], is seen in Figure 1. A user, several devices, and a metaverse component made up of infrastructure, avatars, and technologies make up ELEM for the metaverse [2].
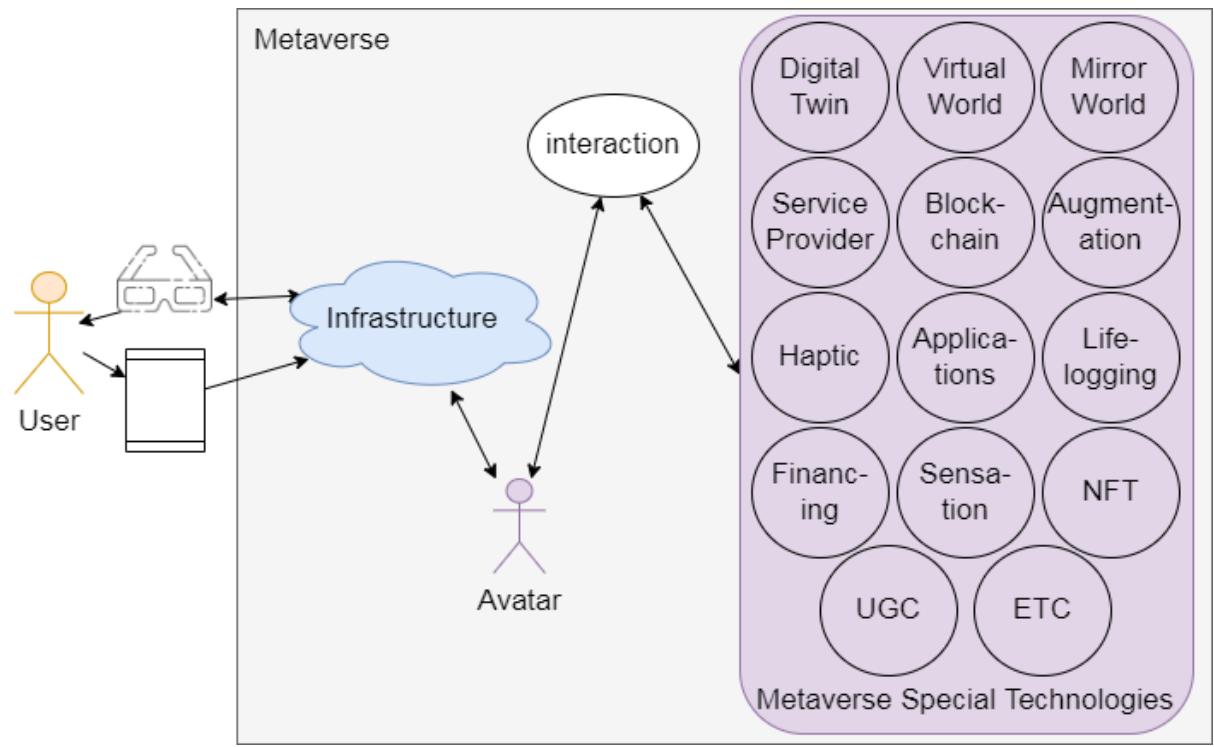 Figure 1: Metaverse Framework (Source: [2], page 8)
There are currently no rules to reduce the security and privacy hazards of the metaverse because it is a relatively new phenomenon. Our ability to trust the technology that underpins virtual experiences is severely compromised as a result. Cybersecurity is a technique for defending against online attacks on programs, networks, and systems [3] defines cybersecurity as the defense of programs, networks, and systems against harmful digital attacks. To defend the confidentiality, integrity, and accessibility of computer resources, networks, software, and data from intrusion, a variety of policies, tactics, technologies, and procedures are used in cybersecurity. Intrusion detection and virus detection are the two key applications in cybersecurity. The following traits characterize current cybersecurity trends:
- $\diamond$ Phishing and Social Engineering, which includes sending fraudulent emails that look like emails from legitimate sources
- Ransonware, a type of malicious software commonly used to extort money by blocking access to files and computer systems until a ransom is paid
- Vulnerability to the Internet of Things (IoT)
- Cloud vulnerabilities and cloud security
- Third-party vulnerabilities
- Internal attacks
- Compliance with data rights
A blockchain is a data structure that is kept in many databases and contains transaction records in the form of a block. When replicated, it functions primarily as a Digital Transaction Ledger (DLT) spread over a computer network [3]. Each transaction in a block is added to the ledger of each participant. A block is a collection of transactions. One of the most well-known applications of blockchain technology is cryptocurrency. Digital money protected by encryption are known as cryptocurrencies, which make counterfeiting and double-spending practically impossible. Peer-to-peer networks, distributed consensus, and public key cryptography are the main foundations of blockchain technology. According to [3], the following six elements are required to create a robust blockchain technology network:
- Cryptography: Block-hain transactions are validated and secure due to the complex calculations and cryptographic evidence among involved parties;
- Immutability: Any records created in a block chain cannot be altered or removed;
- Provenance: Refers to the ability to trace each transaction's lineage inside the block-chain ledger;
- Decentralization: Each participant in the block-chain structure gets access to the entire distributed database due to decentralization. The consensus algorithm enables network control as contrasted to the centrally-based approach;
- Anonymity: Each member of the blockchain network is anonymous; they just have a created address, not
a user identity. This protects user privacy, particularly in a public block-chain setup;
- Transparency: The block-chain system cannot be corrupted. Since it takes a lot of computer power to totally wipe the blockchain network, this is extremely unlikely to occur.
### b) Statement of the Problem
Network Intrusion Detection Systems (NIDS) have increased due to the rapid developments of the internet. NIDS distinguishes between legitimate network users and malicious users, monitors system usage, and identifies behavior that violates security policies. Traditional firewall protection and similar mechanisms have proven inadequate as hackers deliberately circumvent firewall protection. Therefore, it is fundamental to find effective solutions that can dynamically and adaptively defend network systems. Cryptocurrencies are growing in popularity and countries around the world are finding it difficult to manage them. So far, many developing countries have not enacted regulations on cryptocurrencies.
### c) Main Purpose
The objective is to develop a cybersecurity model for a Roblox-based Metaverse architecture framework that can be used in internationalization, education value chain, and online /e-learning education delivery.
### d) Research Objectives
The key research objectives of the research are to:
1. Review the Virtual Reality (VR) and Augmented Reality (AR) architectural frameworks concerning their suitability for education delivery purposes.
2. Ascertain the institutional capacity building requirements for a Metaverse-based academic virtual environment.
3. Determine the challenges associated with copyright and intellectual property (IP) violations faced by universities and Professors with regards the learning materials against for use in a metaverse environment.
4. Assess the cybersecurity risks of a Roblox-based Metaverse educational environment and their impact on internationalization and the education value chain.
5. Develop a cybersecurity model for a Roblox-based Metaverse architecture framework that protects users from cyber-attacks.
6. Investigate how Blockchain technology may be effectively used to handle payments on the metaverse-based education value chain.
### e) Research Questions
The research questions include the following:
1. What is the suitability of VR and AR architectural frameworks for online education delivery?
2. What are the capacity building requirements for the required investment in training academics, students and administrative staff in delivering metaverse programmes and courses?
3. How can universities and Professors safeguard their learning materials against copyright and intellectual property (IP) violations?
4. How can we develop a cybersecurity model that protects the academic space from unnecessary intrusion into and surveillance of their online classrooms?
5. In what way can user-generated content and a chat features on Roblox be protected from intrusion by predators or people posting pornography or other illegal material?
6. How can Blockchain technology be effectively used to handle payments on the metaverse-based education value chain?
## II. LITERATURE REVIEW
a) Systematic Literature Review of Metaverse, Virtual Reality (VR) and Augmented Reality (AR)
Augmented reality is designed to move freely. In other words, whether it is a smartphone application or a pair of smart glasses, visuals are projected onto whatever you're looking at. In virtual reality, VR headsets like the Oculus Quest and Valve Index are used to entirely take over the wearer's field of vision for a 360-degree immersive perspective of his outside world swap out the sight. Between augmented reality and virtual reality, mixed reality provides an improved version of augmented reality. Immersive and realistic virtual worlds are fully enhanced by combining the visual powers of AR/VR with the cognitive skills of AI, improving entertainment, meetings, and even casual hangouts with far-flung friends and family. Virtual worlds have been utilized in the context of software engineering education (SEE) to enhance learning outcomes [4]. Typically, a person enters a metaverse (parallel virtual world) using a virtual reality (VR) equipment, enters the actual world through a digital avatar (by analogy with the user's physical self), and lives there. There is more to the Metaverse than just games and online communities. Ball [4] asserts that the Metaverse is "a vast, open network of 3D virtual worlds produced in real-time that can sustain an almost infinite number of users while maintaining individual presence and data continuity. Identity, history, rights, objects, communications, and payments are among the things that can be experienced simultaneously and persistently". Extended Reality (XR), Artificial Intelligence (AI), Blockchain, Non-Fungible Tokens (NFTs), Edge Computing, Digital Twins, Human-Computer Interaction, Immersion, Sense of Presence, and Affordances are just a few of the technologies and concepts that make up the Metaverse [4]. Research in VR and AR that is theory-based is lacking.
The use of the metaverse in Software Engineering Education (SEE) enables experiences that effectively teach software processes, allowing the student to take on the lead roles in software projects, using techniques of specific development process models, navigating in different environments (such as meeting rooms and programmers' rooms), communicating with other avatars, and interacting with and viewing Unified Modeling Language (UML) diagrams in the same way that they are seen in real-world software projects. [4] conducted a thorough analysis of the literature that took into account 105 published documents from Google Scholar and Scopus, including articles, book chapters, conference papers, conference reviews, and reviews. The systematic review work by [4] highlighted the Metaverse elements, digital currencies, AI applications in the virtual world, and blockchain-empowered technologies to discuss how blockchain and AI fuse with the Metaverse. These were some of the key findings. Notably, technological aspects of the blockchain-based Metaverse approaches, such as data collection, storage, sharing, interoperability, and privacy protection, have been examined. The research clearly illustrated the technological difficulties of the metaverse before emphasizing how blockchain may be useful. Identity, Data, Privacy, Network, Economic, Physical/Social Impact, and Governance are the categories used to group common security risks in the metaverse. From the standpoint of technology adoption, [4] begins with an expanded technology adoption model, describing how developers might expand the metaverse to satisfy user expectations and improve user interaction with this technology. On the network side, noteworthy computational, metaverse, and cloud edge-end computational difficulties, solutions, and concepts were emphasized. In software engineering, using 3D visualization is already a common technique. The portrayal of computer programs, related documents, and data that improves, streamlines, and clarifies the software engineer's mental description of how a computer system functions is known as software visualization, which is a subfield of information visualization [4]. Authoring Tools, Devices, Economy, Infrastructure, Interaction, Physical World, Security, Storage, Technology, and Virtual World are some of the major elements and technologies of the SEE metaverse, according to [4].
Early conceptual articles on VR and AR addressed possible technological applications and proposed that increased sensory acuity and breadth will alter and expand channels for information delivery [5]. The most often used definition of VR is the real-time simulation of one or more people utilizing a 3D artificial environment that they can explore and interact with [5] More specifically, the three essential components of
VR are: (1) Visualization, which allows the user to look around, typically with the aid of a head-mounted display; (2) Immersion, which induces suspension of disbelief and physically realistic representations of objects; and (3) Interactivity, which refers to the degree of control over the experience and is typically accomplished with sensors and an input device like joysticks or keyboards [5]. The terms virtual environment and virtual world are widely used in VR research. Immersion in a virtual setting gives the user the full VR experience. A persistent virtual environment that is available around-the-clock, where users can generate content, play games, and engage in real-time interaction is known as a virtual world (personal representations in 3D format).
Augmented Reality (AR) can generally be defined as augmenting the real-world environment with layers of computer-generated imagery by the device [5]. AR can almost certainly be considered a variant of VR. AR and VR are therefore at different ends of the real-virtual continuum, with one end consisting entirely of real-world objects and the other consisting entirely of synthetic or man-made objects. The difference for users is the level of immersion. In AR, much of what the user sees is still the real world, but in VR, the user is completely immersed in a virtual environment. Tourists happily escape to familiar simulated experiences such as Disneyland and become completely immersed in step-by-step alternate realities [5]. In fact, [5] argued that the application of VR/AR into the tourism experiences merely pushes this alternate reality one-step further. Research has shown that VR's greatest strength is its ability to visualise spatial environments, which is especially crucial in tourism where products are intangible and are confidence goods which consumers are not able to test in advance. Putting on a VR headset and being able to compare different destinations could help consumers make informed decisions found that for theme parks, virtual experiences provided more effective advertising compared to brochures due to the richness and interactivity of the information [5]. Studies show the ultimate goal for web based destination marketing is to provide travel information to tourists via a vicarious experience of the destination to persuade them to visit, and so VR can cater specifically to the vicarious experience by allowing the user to experience selected visual, audio, and most importantly, spatial aspects of the destination without actually being there [5]. Research conducted by [5] identified the gaps and challenges associated with VR/AR as centered around four main themes: 1) awareness of the technology; 2) usability; 3) time commitment required to learn; and 4) the willingness to replace corporeal experiences with virtual ones.
Virtual reality experiences in educational contexts are becoming increasingly important as this technology increases learner motivation and achievement through learning transfer, problem-solving skills, educational equity, and multisensory learning [6]. With the 4th Industrial Revolution and his COVID-19, there is a renewed interest in virtual reality. Technological developments such as head-mounted displays (HMD), controllers, and motion tracking systems, as well as content that applies virtual reality to games, movies, advertisements, Museum exhibits, and education, are progressing rapidly in various fields. [6]. Virtual Reality (VR) refers to the real world like simulated environments artificially created by computer technology [6]. VR aims to create immersive and interactive experiences based on highly realistic visual and auditory stimuli and rich feedback by tracking the user's position, movements and decisions. VR-based teaching has the potential to improve learner motivation, engagement, satisfaction, and transfer of learning [6].
The general definition of augmented reality (AR) is the use of a technology to add layers of computer-generated imagery to the physical environment [6]. It is almost probable that AR is a subset of VR. As a result, AR and VR are at opposite extremes of the real-virtual continuum, with one end totally made up of objects from the actual world and the other entirely made up of artificial or man-made objects related to something created by a computer. The amount of immersion is what makes a difference for users. In contrast to VR, which entirely immerses the user in a virtual environment, AR allows users to view a large portion of the real world. Tourists enthusiastically flee to well-known simulated attractions like Disneyland and fully immerse themselves in step-by-step parallel realities [6]. Earth science engineering education, medical education, STEM education, math education, computer science education, higher education, heritage education, and rehabilitation management of breast cancer survivors are some of the VR education applications listed in [6]. daily activities in chronic stroke patients; therapies for PSTD; studying a foreign language; K-12 and higher education; training in surgery, industrial skills, cognitive training for those with minor cognitive impairment; Education in science, sensorimotor skills, dentistry, and nursing; Training in evacuation; Virtual reality therapy for social anxiety disorder; neuropathic treatment Parkinson disease rehabilitation; education in anatomy and physiology, etc.
Via augmented and virtual reality technology, the metaverse has the potential to expand the physical world by enabling people to interact naturally in both real and simulated surroundings using avatars and holograms [7]. Virtual worlds and immersive games (like Second Life, Fortnite, Roblox, and VR Chat) have been referred to as the forerunners of the metaverse and provide some context for the possible socio-economic effects of a fully developed persistent cross-platform metaverse. Given that there is likely to be some blurring of the barriers between physical and digital, the potential influence on how we conduct business, engage with brands and people, and create shared experiences might be profound. Although the infrastructure and technology to create new immersive virtual worlds on a large scale, one that human avatars might traverse between platforms, do not yet exist, researchers are increasingly looking at the transformative influence of the metaverse [7]. Marketing, education, healthcare, social interaction factors from widespread adoption, concerns with trust, privacy, bias, and the application of the law, as well as psychological impacts associated to addiction and an influence on weaker people, are just a few of the areas that will be impacted. The Metaverse has been defined as a new version of the internet that integrates the real and virtual worlds in a novel way using VR headsets, blockchain technology, and avatars [7]. Through the use of VR headsets, haptic gloves, AR, and Augmented Reality (XR), the technology that permits the construction of the Metaverse is quickly evolving and enabling users to engage in highly engaging and immersive experiences. Marketing, travel, leisure, hospitality, citizen-government interaction, health, education, and social networks might all be transformed if firms were able to modify their business models and operational capacities to function in the metaverse [7]. The many effects of a fully operational, immersive metaverse, where users can easily switch between the virtual and physical worlds within a network, are now being studied by researchers.
### b) Cybersecurity Model for the Education Value Chai
Cybersecurity awareness is the degree to which internet users comprehend the significance of information security, as well as their obligations and actions to apply information security controls effectively to safeguard the networks and data of the enterprise [8]. Cybersecurity awareness in this context refers to the capacity to recognize potential threats to cyberspace, evaluate the risks, and quickly prevent or resolve issues in cyberspace to safeguard personal information and real estate security [8]. People today need a variety of digital skills to succeed in their profession and daily lives because they may take advantage of more chances as digital technology develops. This is necessary due to the growth of the digital economy and an increasingly digitalized society around the world. Across many education value chains, emerging information and communication technologies (ICTs) have led to creative new approaches to teaching and learning. Education value chains are characterized as hybrid relationships between educational systems or processes and other social and economic agents with the goal of enhancing educational quality and addressing issues encountered in the real world [9]. However, the value chain in education has developed into an appealing and fruitful environment for cyber-attacks [10]. The National Initiative for Cybersecurity Education (NICE Framework) was developed in response to these dangers with the goal of promoting cybersecurity training, education, and employee development.
### c) National Initiative for Cybersecurity Education (NICE Framework)
The NICE framework is anchored on pillars that describe the categories, specialty areas, tasks and the knowledge, skills and abilities required to perform work for a certain role. Categories are a high level grouping of common cybersecurity functions that include Security Provisionals (SP), operate and maintain (OM), Oversee and Govern (OV), Protect and Defend (PD), Analyze (AN) and Investigate (IN) [11]. Specialty areas are distinct areas of cybersecurity work such as Training, Education and Awareness. The components of this framework and associated examples according to [12] are displayed in Table 2.
Table 2: NICE Framework Components Explained
<table><tr><td>NICE Framework Component</td><td>Example</td></tr><tr><td>Category</td><td>Oversee and Govern (OV)</td></tr><tr><td>Specialty Area</td><td>Training, Education, and Awareness (TEA)</td></tr><tr><td>Work Role</td><td>Cyber Instructional Curriculum Developer/Cyber Instructor</td></tr><tr><td>Task</td><td>Develop or assist in the development of computer based training modules or classes</td></tr><tr><td>Knowledge</td><td>Knowledge of organization issues, objectives, and operations in cyber as well as regulations and policy directives governing cyber operations</td></tr><tr><td>Skill</td><td>Skill in evaluating information for validity, reliability, and relevance</td></tr><tr><td>Ability</td><td>Ability to craft curriculum suitable for virtual environment</td></tr></table>
The NICE Framework can be used in the education value chain in the identification of training and qualification requirements for the development of critical Knowledge, Skills, and Abilities to execute cybersecurity tasks [13]. The framework serves as a reference or cybersecurity dictionary for educators in crafting curriculum, certificate or degree programs as well as training programmes or experiments that involve the
Tasks, Knowledge and Skills described in the NICE Framework [12]. This in turn ensures that graduates produced have the requisite cybersecurity knowledge and skills that the industry and employers seek. That way the education curriculum across the whole education value chain remains relevant and in sync with the demands of industry.
### d) Evaluation of the Roblox Architecture
The Roblox Client, Roblox Studio, and Roblox Backend are the three essential components of the Roblox Platform, which has a client-server design. The Roblox Client is the engaging front-end user interface that enables user login so that they may explore, interact with, and take part in the 3D virtual world. It is available through PCs, laptops, and mobile devices. A downloadable program called The Roblox Studio is used to design user interfaces. On the Roblox platform, it makes building, publishing, and gameplay possible. When developing various experiences, the Studio contains a ton of templates and ready-to-use materials, including 3D models and animations. The Roblox Backend is the pillar that holds a number of backend services, and the Roblox Cloud, which is essentially the platform's infrastructure and allows for the delivery of services like 3D simulations, is housed there [14]. The front-end of Roblox is shown on Figure 2.
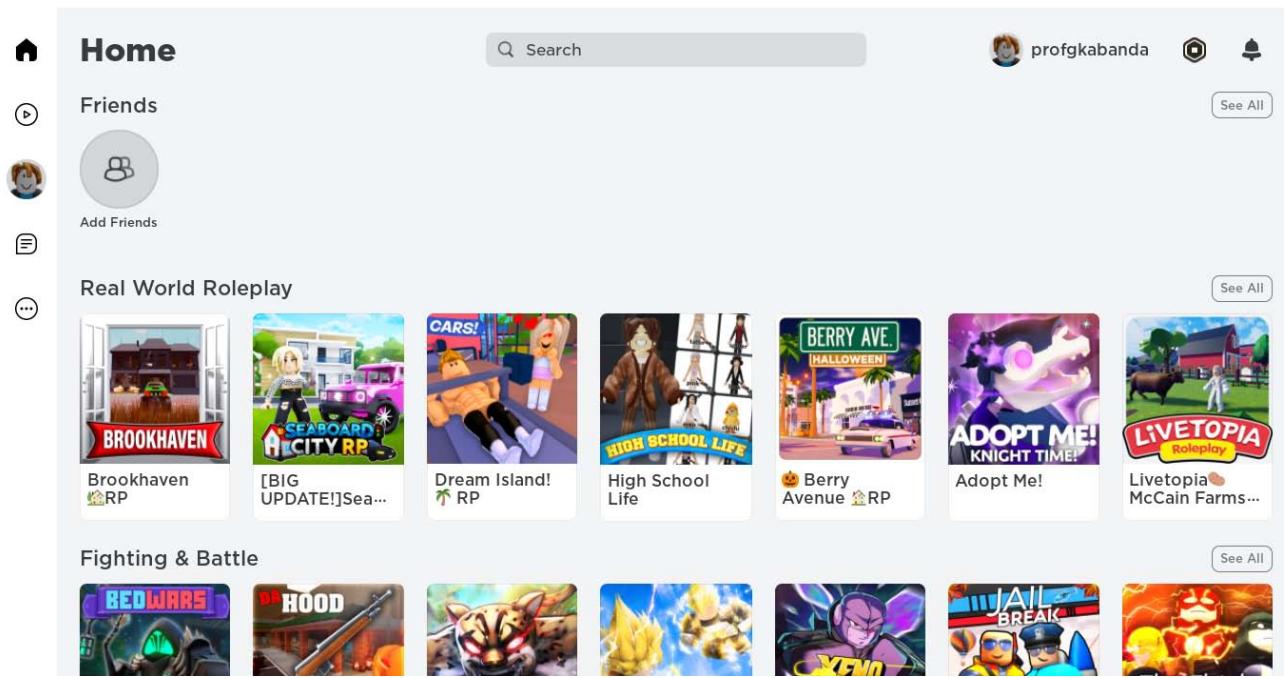 Figure 2: The Roblox Front-End
Roblox uses virtual reality to let users develop and create immersive learning environments, which boosts novelty and encourages a rise in the use of teaching and learning [15], [16]. Students that engage in immersive learning are also inspired to build the resources they employ, changing them from knowledge consumers to creators of knowledge. It makes it possible for educators from all tiers of the education value chain to use innovative teaching strategies that equip students with the abilities to foster creativity in a fun learning environment [17], [18]. The Roblox design also provides the best framework for online learning, role-playing, and promoting entrepreneurship [19] and digital citizenship [17]. The Roblox platform, which is based on the use of VR technology and the metaverse principles [21], provides students with a wide range of virtual collaboration abilities and opportunities [20]. These acquired abilities will also be available to be transferable across numerous communities. The advantages of virtual reality, however, are equally essential for creating a comfortable and safe online social environment for students of various skill levels [22].
On the other hand, it is possible that the current security frameworks will not be sufficient to handle the expanding attack surface that spans beyond only computers and networks [18]. The new models or frameworks for safety and security in the Metaverse that Roblox is based on must consequently take human psychology and the human brain into account [23]. Given the lack of anonymity in the metaverse-based Roblox architecture, confidentiality concerns are also of major concern. As a result, increased user awareness is necessary so that students can avoid the dangers presented by the immersive surroundings. The Roblox platform may additionally pose psychological risks, including as addictions [24]. In this sense, it is vital to recognize that the metaverse is still evolving, and as a result, users of platforms like Roblox may find it difficult to trust the platform due to security flaws. Additionally, because it depends on the convergence of a number of technologies that serve as enablers, such as virtual reality (VR), augmented reality (AR), edge networks, 5G, and artificial intelligence, it might take some time for it to be integrated into the value chains of education, particularly in developing nations. These technologies have not yet been adopted in these nations.
As the Roblox metaverse has grown in popularity, numerous brands have used the Roblox game engine to create games that incorporate real-world advertisements. The majority of businesses in the Roblox metaverse create video games that advertise actual goods and occasions. For instance, a movie producer might create a game that promotes a forthcoming movie as well as potential partners' brands from industries outside than entertainment. As a result, Roblox has ingratiated itself into pop culture, collaborating with companies like Nike and television series like Stranger Things. Roblox has also merged the goods and universes of these companies into a number of immersive games.
### e) The Hadoop Architecture Framework
The file system, Map Reduce engine, and Hadoop Distributed File System are all included in the Hadoop architecture (HDFS). MapReduce engines come in two flavors: Map Reduce/MR1 or YARN/ MR2. Map Reduce [34]. A framework called "map reduce" is intended to process a lot of data concurrently and widely across a group of processing units. A single master and numerous slave nodes make up a Hadoop cluster. Data Node and Task Tracker are on the slave node, whereas Job Tracker, Task Tracker, Name Node, and Data Node are on the master node. The framework aims to simplify interaction with huge data. Through the use of straightforward programming concepts, it enables the distributed processing of big datasets across computer clusters. The Hadoop architecture has established itself in businesses and industries that must work with massive, sensitive data sets that require effective processing [34]. As a result, the Hadoop framework is a framework that permits the processing of huge data sets that are organized into clusters. The Hadoop architecture consists of a number of modules supported by a sizable ecosystem of technologies and offers a range of services to address big data issues [35]. It consists of Apache projects as well as a number of paid tools and services. Most of the time, these important components are supplemented or supported by tools or solutions. Together, these instruments can offer services including data absorption, analysis, storage, and maintenance.
Hadoop Distributed File System (HDFS), Processing/Computation layer (Map Reduce), Yet Another Resource Negotiator (YARN), and Hadoop Common are the four main components of the Hadoop architecture [36]. The Hadoop framework application operates in a setting that offers distributed computing and storage across computer clusters [37]. The Hadoop framework is made to expand from a single server to tens of thousands of servers, each of which provides local computing and storage [38]. Numerous significant corporations, including Facebook and Google, have used Hadoop, a well-liked open source MapReduce implementation [39]. The Hadoop framework is presented in Figure 3.
The main or most important part of the Hadoop ecosystem is HDFS, which is in charge of storing massive amounts of structured and unstructured data across numerous nodes while also keeping the metadata in the form of log files [35]. It is made up of a Name node (which carries Meta data, or information about data), and a Data node (stores the actual data). HDFS is a file system that was specifically created to store enormous datasets on commodity hardware, storing data in diverse forms on numerous devices [40]. The Name Node and the Data Node are HDFS's two constituent parts. The master daemon is the Name Node [41]. There is just one Name Node that is active. It stores all the information and controls the Data Nodes. The slave daemon, however, is Data Node. There can be multiple Data Nodes and its purpose is for storing the actual data.
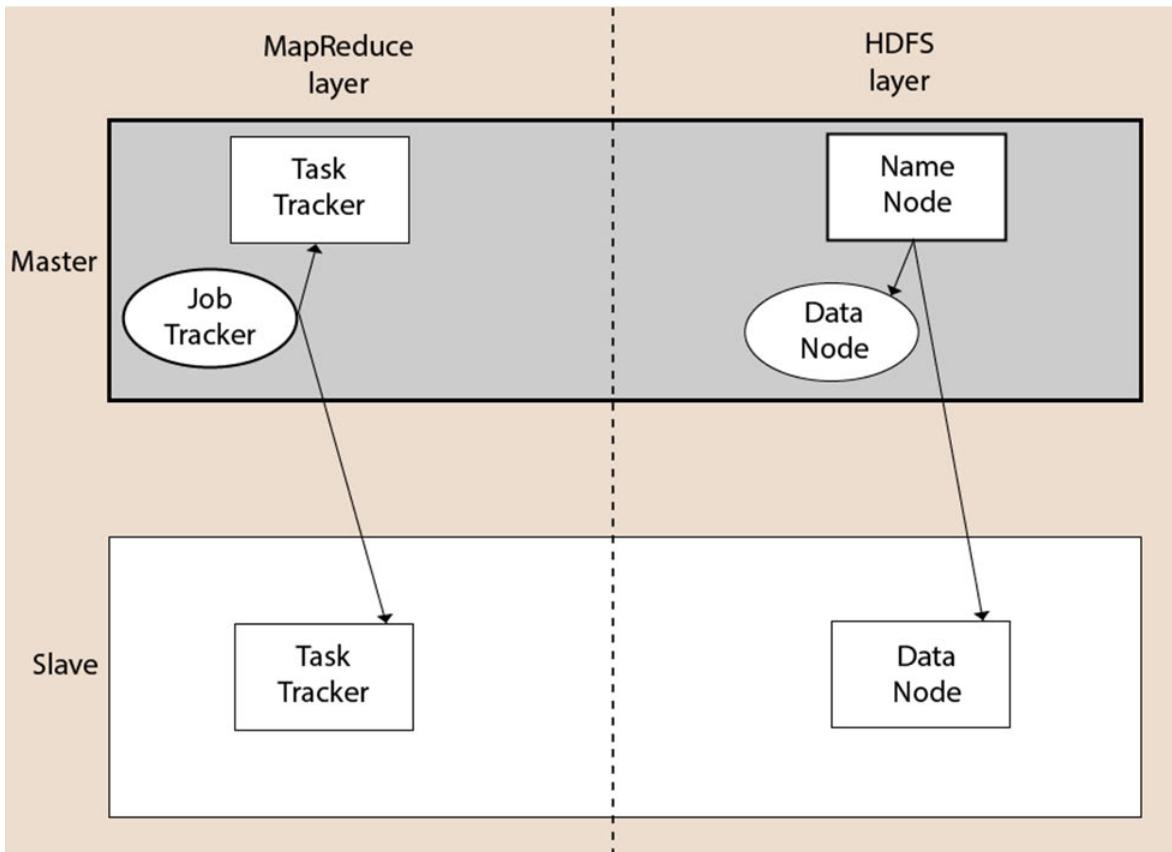 Figure 3: Hadoop framework
The Yet Another Resource Negotiator (YARN), which aids in managing resources across clusters, is the other part of the Hadoop framework [42]. For the Hadoop System, it manages scheduling and resource allocation. There are two parts to YARN. The master daemon is Resource Manager (Master). It controls how resources like CPU, memory, and network bandwidth are distributed. The slave daemon, NodeManager (Slave), reports resource utilization to the Resource Manager.
Another component is Map Reduce. By utilizing distributed and parallel algorithms, Map Reduce enables the continuation of the processing's logic and aids in the creation of applications that reduce large data sets to manageable ones [34]. Map Reduce is a parallel programming model for creating distributed systems that process massive volumes of data quickly and fault-tolerantly on vast clusters of cheap hardware. Map Reduce employs the two methods Map() and Reduce(), the former of which performs data sorting and filtering and groups the results into groups [35]. The Reduce() method later processes the key-value pair-based output that Map produces. On the other hand, Reduce() aggregates the mapped data to do the summary. Reduce(), in its simplest form, takes the output produced by Map() as input and splits the tuples into smaller groups.
The Hadoop framework has the benefit of making it simple to create and test distributed systems. It is effective and uses the underlying parallelism of the CPU cores to automatically divide the data and work across the computers [43]. In order to provide fault-tolerance and high availability (FTHA), the framework Hadoop does not rely on hardware; rather, the Hadoop library itself has been built to recognize and manage problems at the application layer. Again, machines can be dynamically added to or deleted from the cluster, and Hadoop keeps running unabated.
### f) Blockchain Technology Application Model
An open financial ledger or record called a blockchain is where every transaction is verified and approved. A blockchain is intended to function as a decentralized network of numerous computers, often known as nodes [44]. With blockchain technology, each node acts as a network administrator who willingly joins the network, creating a distributed database design. A blockchain is virtually impossible to hack since there is no centralized data in its architecture. Distributed ledger technology is another name for blockchain technology. It enables participants to achieve transactions, transfer assets, and secure the settlement of transactions at a cheap cost [45]. Traceability, transparency, smart contracts, and security are the four main characteristics of blockchain technology. These features ensure that the technology is applicable in a wide range of fields in addition to its primary use as a cryptocurrency, including government elections, healthcare, logistics, identity management, supply chain, and others. An increasing collection of ordered documents known as blocks are supported by the blockchain architecture [46]. Each block keeps a connection to the preceding block and a timestamp. A blockchain is virtually impossible to exploit since there is no centralized information in its architecture [47]. Block chain applications can have positive effects on an existing business model, including [48], [49], and [50].
1. Because of the variety of advantages it offers, block chain technology has gained widespread use.
2. The block chain is a perfect register for cooperative business ventures because there is no central authority in charge of monitoring operations.
3. The use of digital signatures and verification in block chains helps thwart fraud.
4. Information is not centralized, which prevents data loss.
5. Simplicity: more integration between procedures from various entities, simplified processes
6. Traceability: Transactions are easily traceable, and the ledger's immutability ensures that they are attributed to the right parties and can be proven to have occurred.
7. Better performance: By integrating and automating processes, operations and other activities can perform more quickly.
8. Stronger relationship: Greater process integration and simplification imply the development and maintenance of stronger bonds with other stakeholders (participants to the same supply chain).
Block Chain Can be Either Centralised, Decentralised or Distributed as Shown Below on Figure 4.
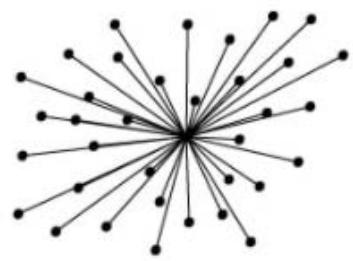 centralised
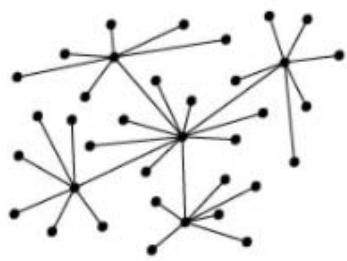 decentralised
distributed Figure 4: Blockchain Distribution Options
The components of the blockchain architecture are-
1. Node: which is a computer in the blockchain architecture, is one of its constituent parts (each node has an independent copy of the entire blockchain ledger)
2. Transaction: A data record that is confirmed by blockchain users and acts as a nearly unchangeable affirmation of the legitimacy of a financial transaction or contract.
3. Block: A compartment for encrypted data that includes a native hash code to identify the block, a hash code from the block before it in the chain of blocks, and a series of time-stamped transactions.
4. Chain: Blocks arranged in a line.
5. Miners: Nodes that validate blocks before integrating them into the blockchain structure are known as miners.
6. Consensus (protocol): A set of guidelines and agreements for using blockchain technology.
The Blockchan cyber vulnerabilities identified by [3] are as follows.
Blockchain code vulnerabilities from programs that rely heavily on encryption algorithms or may have underlying software coding flaws.
- Blockchain platform vulnerabilities from applications caused by software running on platforms with known security issues and general-purpose operating system.
- End-User vulnerabilities, such as online wallet hacking, private key theft, etc.
- Wallet controls - Although digital wallet companies are now reducing personal risks and offering better key management services, using passwords and other user authentication controls still carries a significant level of risk.
## III. RESEARCH METHODOLOGY
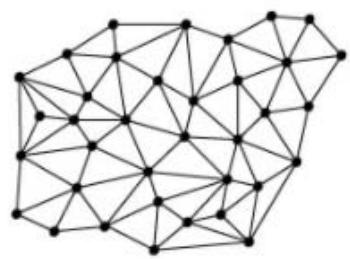
The General Thinking of Researchers about The Research Work is Shown on Figure 5.
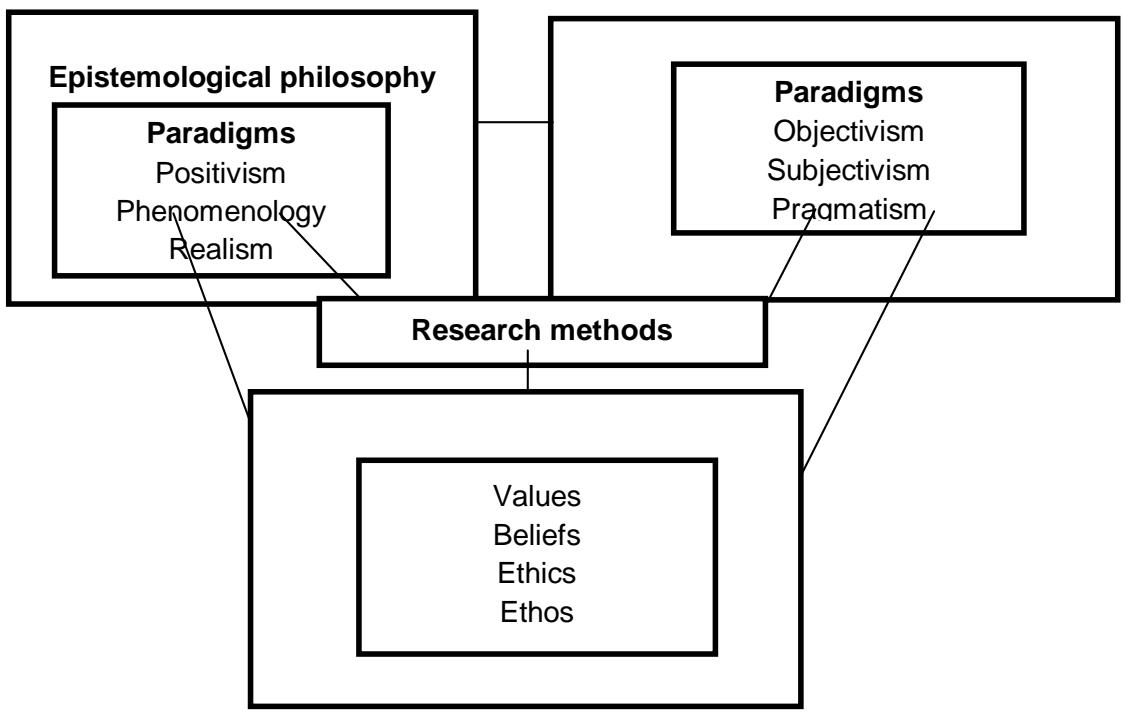 Figure 5: Research Philosophy and Paradigms
### a) Epistemological Philosophy
This is how the researcher thinks of legitimate knowledge structures [25]. Researchers have access to his three main epistemological tenets: positivism, realism, and interpretivism [26]. The pragmatism paradigm was used in conducting this research. In order to determine the truth regarding the cybersecurity implications of computer vulnerabilities, a methodical and scientific approach was used during the data collection procedure.
### b) Ontological Belief
According to [25], ontology is concerned with the nature of reality and raises issues with the assumptions that researchers make about how the world functions and the commitment to holding specific viewpoints. Positivism is the belief that social entities actually exist, independent of the social players who care about them [25].
### c) Axiological Belief
The researcher admitted that the relevance of ethics in the study process was crucial. In order to have an unbiased evaluation of the topic under study, the researcher made an effort to maintain their separation from the respondents during the data gathering time. The respondents were treated with respect and in a manner that was socially just. The researcher also thought the research had a positive net impact on Zimbabwean organizations, as putting its recommendations into practice is expected to result in better cybersecurity measures. For the purpose of ensuring that the industry obtains high-quality suggestions on information technology and cyberattacks, data were accurately evaluated. Additionally, the researcher made an effort to protect the confidentiality of the respondents' personal data.
### d) Research Approaches
A research approach is a strategy that includes phases from general hypotheses to specific methods of data collecting, analysis, and interpretation. As a result, it depends on the type of research problem being addressed. There are fundamentally two types of research approaches:
1. Inductive/qualitative
2. Deductive/quantitative.
### e) Qualitative/inductive Research
This strategy places a lot of attention on the techniques used to gather or produce data. However, it gives less weight to the methods of data interpretation that need analysis. Furthermore, using an inductive method, concepts, themes, and models are typically derived from careful study of secondary data. As a result, it is frequently utilized for qualitative data analysis. This starts with the choice of the study area and develops a theory. The inductive strategy comprises combining various secondary data into a succinct the research's goals and its findings gleaned from the raw data. Additionally, make those connections visible to others and how they will advance the study's goal, as well as building a theory based on the experiences and procedures made apparent by the text data [27]. The study's goal is to comprehend a phenomenon, as shown by the choice of an inductive approach through thematic analysis (a "data driven" approach). Hypothesis testing is not its main concern. This strategy was partially used in this investigation.
### f) Quantitative Research/deductive
Making the relationship between what is known and what might be learnt by research requires the use of statistical analysis, which is frequently a component of quantitative research approaches. As a result, knowing the relationships between variables using either descriptive or inferential statistics is necessary for data analysis using quantitative methodologies. Descriptive statistics facilitate population conclusions and parameter estimation [28]. To test hypotheses, statistical analysis is needed for quantitative data. The deductive method is frequently utilized because it allows researchers to move from general to specific reasoning. Additionally, the researcher draws a theoretical framework (hypothesis) from general viewpoints, tests it, and draws a specific conclusion as a result. The deductive method of analysis or reasoning entails the investigation of theories, creation of theoretical frameworks or hypotheses, statistical testing of hypotheses, observation, and validation of a certain conclusion deduced logically from premises [29]. For this investigation, deductive research was the most useful. When huge volumes of data were collected and analyzed using descriptive and inferential statistics, which all needed deductive thinking, quantitative research was equally utilised.
## IV. KEY FINDINGS, DATA ANALYSIS AND INTERPRETATION
a) Metaverse, Virtual Reality (VR) and Augmented Reality (AR)
The Metaverse uses technology to transcend our physical reality, changing the human experience. By describing each aspect of the metaverse [7], as seen on Figure 6, we categorize definitions of the metaverse into four categories: environment, interface, interaction, and social value. In terms of the interface, the metaverse is also divided into categories based on the level of immersion, such as 3D and virtual reality (VR) [7]. Although users can experience a great deal of immersion when using VR devices in a 3D environment, the metaverse provides more than just the usage of VR devices in 3D environments. Metaverse definitions focus on interactions for users and non-player characters that go beyond ordinary talks in addition to settings and interfaces (NPCs). There are realistic, unreal, and blended environments in the metaverse. Based on an actual environment, the fused environment displays some irrational characteristics. The designer's intent and interpretation are properly reflected in the realistic metaverse's depiction of geography and natural features [7]. Avatars cannot exist in two places at once in the realistic metaverse, and movement speed is constrained similarly to how it is in the physical universe. Avatars and holograms can be used to work, interact, and socialize via simulated shared experiences in the new metaverse concept, according to Mark Zuckerberg. This integrated immersive ecosystem allows users to cross barriers between the virtual and real worlds with ease [7]. There are physical, immersive, and 3D interface options available. For the metaverse to remain continuous and to encourage user interaction, immersion is a crucial component. Social networking, teamwork, and persona discourse are the three categories used to describe interaction in the metaverse. It is challenging to define and use the social networking experience in the metaverse effectively.
The metaverse provides tasks that are challenging to do in reality as a complement to the real world in a variety of ways. It takes the place of familiar settings (such as offices, SNS, in-person classes, and medical care) and enables things that would be difficult to complete in reality due to issues like cost [7]. As a tool, the metaverse reduces complexity (such as in aircraft engineering) and boosts coherence from a multimodal perspective. The aim is the metaverse itself [7]. The metaverse's operating system needs a lot of users in order to remain sustainable, and seamless services are accessible even on relatively basic mobile devices. Environmental design must take the scalability of the current limited environment into account for long-term service.
It is vital to constantly develop open source platforms that can facilitate collaboration between different developers and a top expert group in order to grow the environment and make use of it [7]. The sustainability of the metaverse depends on an intuitive user interface.
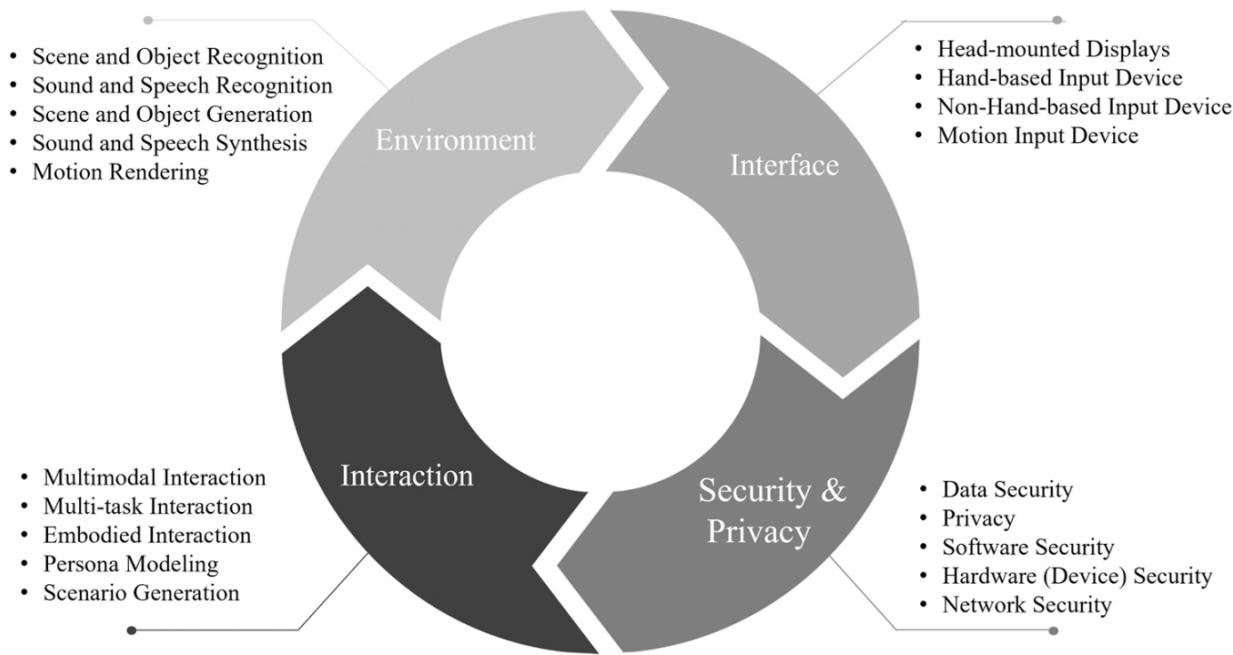
Figure 6: Metaverse with the Environment, Interface, Interaction, Security and Privacy [7]
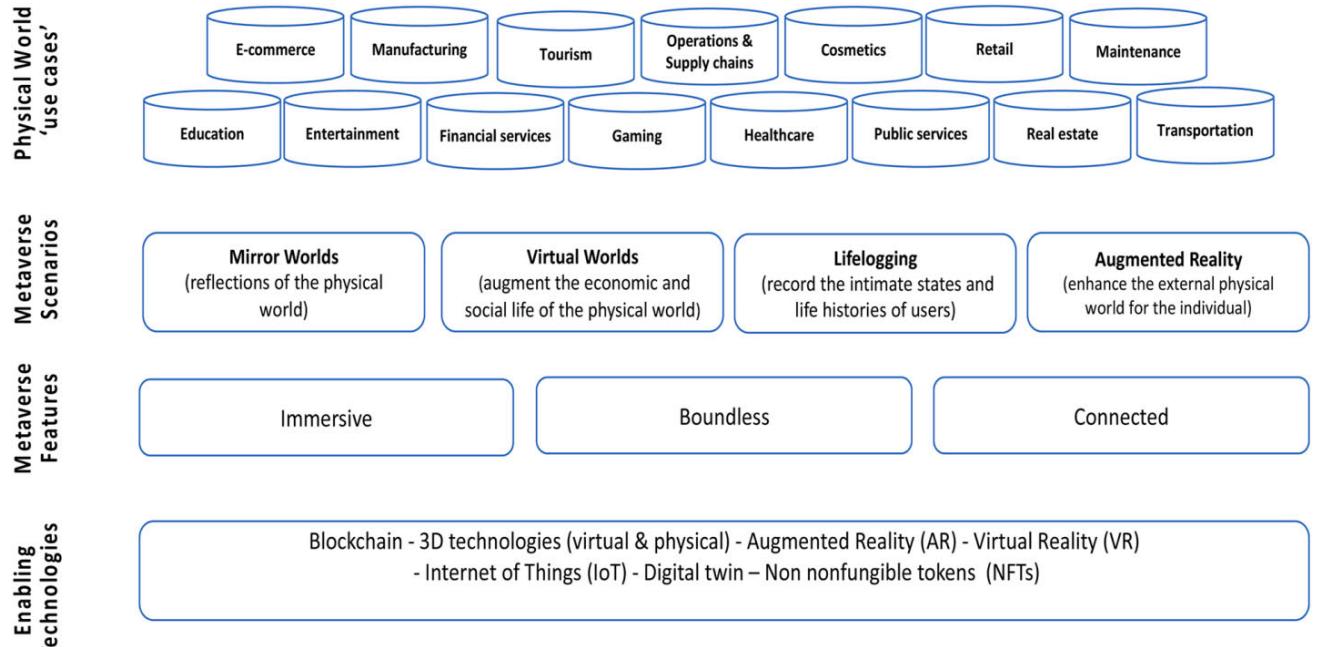
Figure 7 Below Depicts How The Metaverse Is Conceptualized. Figure 7: Conceptualisation of the Metaverse (Source [7])
Holograms and eye-attached lenses are useful additions to augmented reality and virtual reality. Additionally, some user interfaces shield young users from unwanted sounds by muffling and expressing them in the actual world. The majority of interfaces in the metaverse consist of visual and supplemental auditory forms. Despite extensive research on metaverse technology, privacy and security in the metaverse have received very little attention. In the metaverse, security and privacy are major concerns, just like on social networking sites. In order to identify a user, malicious users can track and gather real-time biometrics (such as facial expressions and vocal inflections) and metaverse users' behavior (such as their interactions with other users and purchasing actions). The metaverse is constructed in a cyber (or digital) environment, so we must take cybersecurity and privacy concerns into account in order to provide consumers with appropriate services securely and effectively. To ensure that people and systems are protected from a variety of risks and
vulnerabilities, cybersecurity and privacy should offer a variety of measures, approaches, and solutions [7]. A universe without nations, boundaries, or gender is the metaverse. Beyond the current humanistic approach, a fresh viewpoint is required. Since the metaverse incorporates various concepts like marketing, management, and strategy research, it spans a wide range of disciplines. The main components of the metaverse economy are cryptocurrencies and non-fungible tokens (NFTs), such as bitcoin and ethereum. NFTs enable the verification of these assets and even identities while representing ownership of virtual in-game items, virtual avatars, real estate properties, and other assets [7]. Similar to how money functions in the normal economy, cryptocurrencies function similarly in the metaverse economy.
### b) Cybersecurity on the Education Value Chain and Blockchain
A cybercrime threat or vulnerability must be positioned in a multidisciplinary perspective. However, the nation's educational system has been stove-piping such a cybersecurity strategy for decades. While understanding the technical aspects of the cyber environment, networked systems, operating systems, and the security threats that surround them is given more importance, little to no attention is paid to the human actors and their decision-making processes, which are crucial to the success of a cyber-attack. In actuality, cyber-attacks have increased in frequency and cost to enterprises, organizations, economies, and other infrastructure-related institutions. The world has become more network-centered in the twenty-first century, and the rapid development of internet technology has given rise to a contemporary cybersecurity culture and a complex threat environment in the higher education sector. The future of the fourth industrial revolution is a system called Blockchain.
The blockchain is a public ledger that stores collections of transactions, referred to as blocks, that are chronologically and cryptographically connected. Excellent security, immutability, and program expertise dependent on the Blockchain architecture and the nature of the consensus protocol used by the Blockchain are the primary characteristics linked with it. Blockchain technology has produced a payment system that accepts both cash and non-monetary payments. With features of distribution, centralized ledger alteration connects parties who are jointly responsible for various parts of a single authoritative ledger. The complete abolition of a centralized regulating authority was associated with the dispersal of ledgers and the development of a system in which certain individuals kept copies of the entire ledger system. A major novel that has been circulated requires agreement from those who have copies in order to make adjustments or additions, and each addition or change is duly recorded in each copy of the ledger as well as with authority.
### c) Institutional Capacity Building Requirements for a Metaverse-based Academic Virtual Environment
A platform based on content businesses like gaming is now being created using metaverse technology [30]. Accordingly, [30] lists and illustrates the four definitions of the Metaverse in Figure 8 and Table 3.
Table 3: Definitions of the four types of Metaverse
<table><tr><td>Classification</td><td>Definition</td></tr><tr><td>Augmented Reality</td><td>It is a technology that enhances work efficiency by augmenting virtual information in real space in real time and allowing users to interact with the augmented virtual information.</td></tr><tr><td>Lifelogging</td><td>It is a technology that captures, stores, and depicts everyday experiences and information about objects and people.</td></tr><tr><td>Virtual Reality</td><td>It refers to a specific environment or situation or the technology itself that is like reality but is not real, created by artificial technology.</td></tr><tr><td>Mirror Worlds</td><td>It is a digital representation of the real world that makes an effort to geographically accurately map real-world structures. It provides a software utility model of actual environments and how they function.</td></tr></table>
As seen in Figure 6, the horizontal axis is a measure of user immersion intensification and the extent to which the external environment is reflected (intimate). On the other hand, the vertical axis displays a criterion for differentiating between simulation in the virtual world and the augmentation of reality, which is a setting in which information is implemented. This standard divides the vertical axis into augmentation and simulation and the horizontal axis into intimate and outward elements. Four subcategories of the metaverse can be identified:
augmented reality, life logging, mirror worlds, and virtual worlds.
The lines separating the actual world and the Metaverse world will eventually merge to the point that it is possible to forget that you are in cyberspace. Based on the convergence of technologies like virtual reality (VR) and augmented reality (AR), which enable multimodal interactions with virtual surroundings, digital objects, and people (AR), the metaverse is a post-reality world, a continuous and enduring multiuser environment that combines physical reality with digital virtuality [31]. The Metaverse is an ever-available web of socially networked immersive experiences for multiple users that allows for real-time, embodied user conversation and dynamic interactions with digital objects. The Metaverse concept is summarized on Figure 7. The Metaverse is an ever-available web of socially networked immersive experiences for multiple users that allows for real-time, embodied user conversation and dynamic interactions with digital objects. Institutional capacity building requirements for a Metaverse-based academic virtual environment is centered on investments in Mixed Reality (MR) and the Metaverse concept shown on Figure 9. Mixed reality (MR) can combine social media
connectivity with immersive VR and AR technologies' unique features [31]. Online education will push the boundaries of informal education and social interactions in the Metaverse. Physical presence in the classroom won't be valued as a distinctive educational experience any longer. Telepresence, avatar body language, and facial expression conformance will make virtual meetings equally as productive as in-person ones. Additionally, MR in the Metaverse can support active mixed education to develop deeper, more enduring knowledge [31]. Additionally, it can contribute to the democratization of education by enabling equitable participation without regard to a person's location.
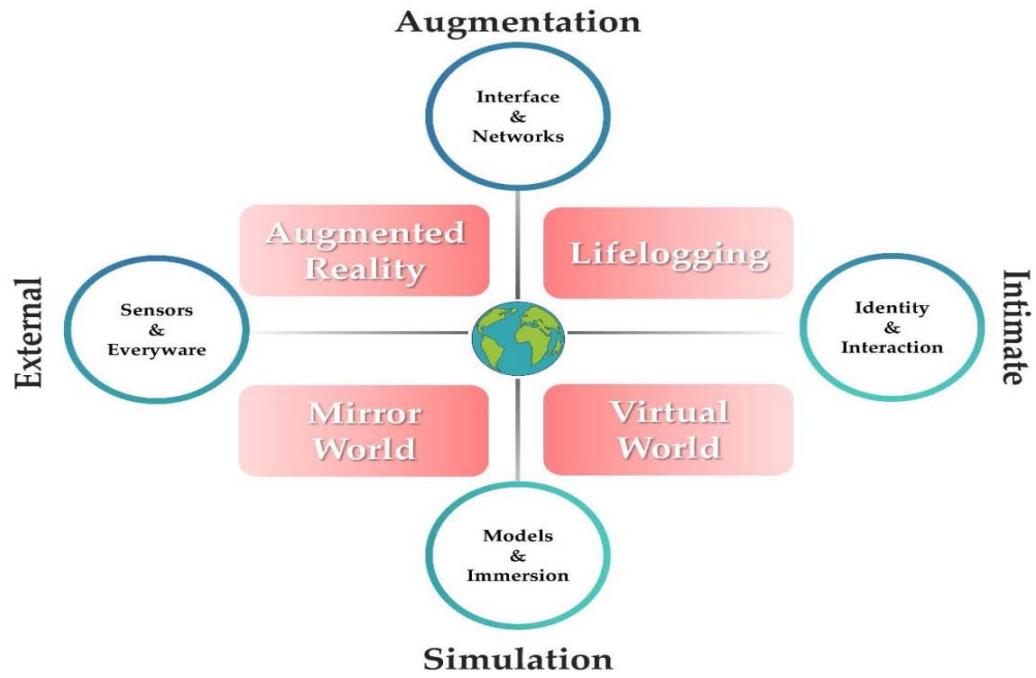
Figure 8: The Four types of Metavernes (Source: [30], page 3)
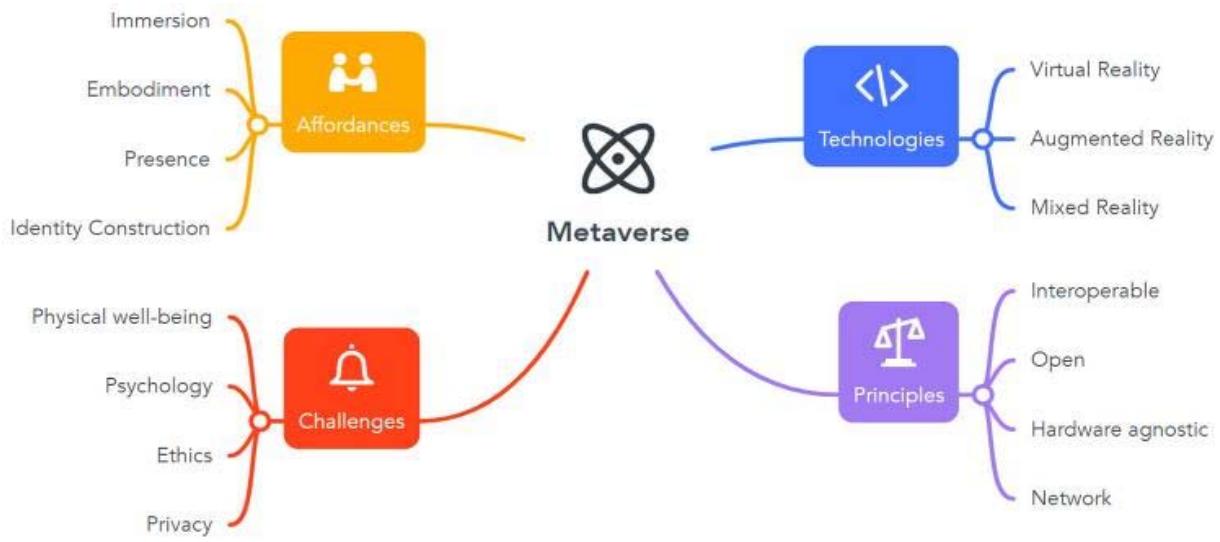 Figure 9: The Metaverse Concept (Source: [31], page 3)
Online learning may be done more interactively thanks to the virtual world idea espoused by Metaverse. The learning environment at school or college is not compromised by the support offered by Metaverse for online learning. Online learning can be done more interactively with the virtual world idea suggested by Metaverse [31]. The world of education will unavoidably need to get ready to embrace this technology as a result of the Metaverse being developed by powerful technology businesses. The atmosphere will undoubtedly be more comfortable and enjoyable in the virtual/Metaverse world where school buildings with all the amenities can be built, but the relationship between teachers and students in the real world may suffer because they only interact with each other in the Metaverse in the form of their respective avatars, whereas they hardly or never interact in the real world [31]. In learning and educational situations, Metaverse offers students more immersive experiences and a more interactive learning experience.
### d) Handling Copyright and Intellectual Property (IP) Violations of Learning Materials
Patents, copyrights, trademarks, and trade secrets are all considered to be part of intellectual property. With a patent, the owner has the legal authority to prevent others from "practicing" (creating, utilizing, and commercializing) an invention. New, practical, and nonobvious inventions that fall under the categories of methods, machines, manufacture, and composition of matter are eligible for patent protection. Thus, the outcomes of academic research can take many different forms, including technologies, chemicals, biological materials, instruments and methods for conducting study, production processes, and software. Trademarks, service marks, certification markings (which, for example, indicate testing by an independent laboratory), and collective marks are the many types of marks used to distinguish goods and services in the marketplace (identifying membership in an organization, such as real estate agents). Original works of authorship preserved in any physical form are protected under copyright. When a work satisfies these legal standards, copyright becomes its property; there is no longer a need for an application or registration procedure. Literature and other printed materials, architectural or engineering drawings, circuit diagrams, lectures and other instructional materials, musical or dramatic compositions, motion pictures, sound recordings, choreography, computer software and databases, as well as paintings and sculptures, are examples of subject matter that is eligible for copyright protection. According to [33], intellectual property in universities includes developed theories, laws, mathematical formulas, and symbols; Published print and electronic books, journals, and articles; discoveries and innovations resulting from scientific research, statistical information and reports, and art prints and drawings.
Patents, trademarks, breeder's rights, copyrights, and industrial design rights are all examples of intellectual property rights.
One component of access to knowledge is access to educational resources. There is little question that access to educational resources is a key component of the success of any educational system and that education is a cornerstone of social and economic growth. Any set of policy solutions that deal with the issue of access to learning materials in southern Africa will have to take the informal economy into account in order to be comprehensive, despite the fact that it may be challenging for policy-making structures to overcome the naturalization of simplistic polarities like "piracy" on the one hand and the "formal economy" on the other. It is presumable that a student's ability to persevere through the learning process depends on the caliber and accessibility of the learning materials. People who work on academic, instructional, or artistic projects create a wide range of copyright-eligible items that they would want to guard from unlawful use. Books, articles, monographs, bibliographies, lecture notes and handouts, musical compositions and recordings, visual arts like paintings and pictures, films, and audiovisual works, as well as computer programs, are just a few examples of these. The copyright of a work that is created by a member of the faculty, staff, or a student is theirs to keep. Even while the College might offer some assistance in the form of resources like buildings, supplies, gear, or staff, it is proper for each individual to own the copyright to such works. The College may use, reproduce, and modify any copyrighted work that was initially created with the express intent of making it available to people other than, or in addition to, the original creator for use in teaching, administration, or other College activities. It is understood, however, that the individual will grant a perpetual, worldwide, royalty-free license allowing the College to do so. Even if the person who designed the curriculum or programs has left the College, the College will have access to these materials for free. It is the individual's responsibility to make sure that any additional authors of works with multiple authors are made aware of this policy and give their consent for the license to be granted to the College in cases where one or more of the authors are not affiliated with the College and are not covered by this policy.
It is possible to start learning and producing information as soon as possible. Students can acquire new knowledge and create it as soon as possible without any additional restrictions that might pose a barrier, such as classroom partitions and time constraints. In order to experience the true freedom of learning, which must be enjoyable for them, students will have a class that is as diverse as this world and more time to spend researching the knowledge they wish to acquire. Ultimately, there will be more and expanding learning resources. The use of technology will inevitably lead to the development of new knowledge and technologies. The more knowledge sources we have access to, including sources of information that may be used to advance our abilities, will result in the creation of learning resources that are more diverse. Schools are not just structures anymore. There will be many virtual schools that do not require significant amounts of land and buildings to construct an educational institution and the existence of the Metaverse will bring about changes to the physical form of educational institutions in the globe. The majority of educational institutions are out of reach due to distance, travel time, and prohibitive expenses.
Online learning has replaced the traditional face-to-face classroom setting for instruction. Because of the limited resources available to schools that demand teachers and students to teach both in social media groups and in class, several schools provide daily instruction through online learning programs. Poor learning performance is a result of this, especially when there is a literacy gap between teachers and students. Because no technology can completely replace the function of the teacher in student-centered learning, the Metaverse will have an impact on the educational landscape. Teachers should interact with students in person rather than online. Other than teaching and learning activities, the Metaverse can be used for administrative tasks like managing teachers, finances, supervision, promotion files, and so forth. Whether these tasks can ultimately be implemented in our nation is still up in the air, and it is obvious that for the time being, all of them are still confined to wishful thinking. Negative effects, like the loss of social warmth because they do not directly engage with people, will be felt if all educational activities are conducted digitally. Because education is merely a formality, educators do not have a direct relationship with their students.
government and business, and they serve as a foundation for the case for public funding of research and the university's role as an independent contributor to both policy and business. The administration and negotiation of faculty-generated intellectual property can be difficult and have serious repercussions for those directly involved.
The disadvantages of the Metaverse are-
1. Metaverse requires a high level of technology consumption due to the sophisticated and high-quality graphics it produces.
2. It is quite expensive to gain access to technologies that enable Metaverse.
3. Due to the Metaverse's unbounded nature, there is the potential for social and cultural development.
4. Relevance and metaverse are still struggling with the question of whether communication and action in the virtual world are necessary or not.
e) Cybersecurity-Compliant Hadoop Architecture Framework for Metaverse Online Education Value Chain [3] explained how the framework of bitcoin and blockchain technology addresses cyber concerns and adds value to the financial services sector and education value chain in the following way:
- Minimal Transaction Fees: Peer-to-peer cryptocurrency transfers necessitate no centralized intermediaries, therefore transaction fees are negligible, and decentralized systems do not impose fees for currency conversion.
- $\diamond$ Accessibility: By their very nature, cryptocurrencies are not subject to a country's exchange rates, interest rates, transaction fees, or other levies.
- Instant Payment: Peer-to-peer transactions make Instant Payments possible.
- Improved security provided by Blockchain technology: Blockchain technology offers greater security than centralized financial systems, which makes it very difficult for hackers to compromise.
- Transparency in the transactions.
- $\diamond$ Decentralization framework supporting stakeholder governance by giving people, rather than centralized authorities, the power to make decisions.
- $\diamond$ Immutability: The blockchain's general ledger's immutability makes it impossible for internal players to change data for their own gain.
The Big Data Analytics Framework that is suggested for implementation in a Hadoop-Metaverse system is represented on Figure 10 below from the conceptual framework perspective of this research article.
## BIG DATA ANALYTICS FRAMEWORK FOR THE HADOOP-METVERSE EDUCATION VALUE CHAIN ENVIRONMENT
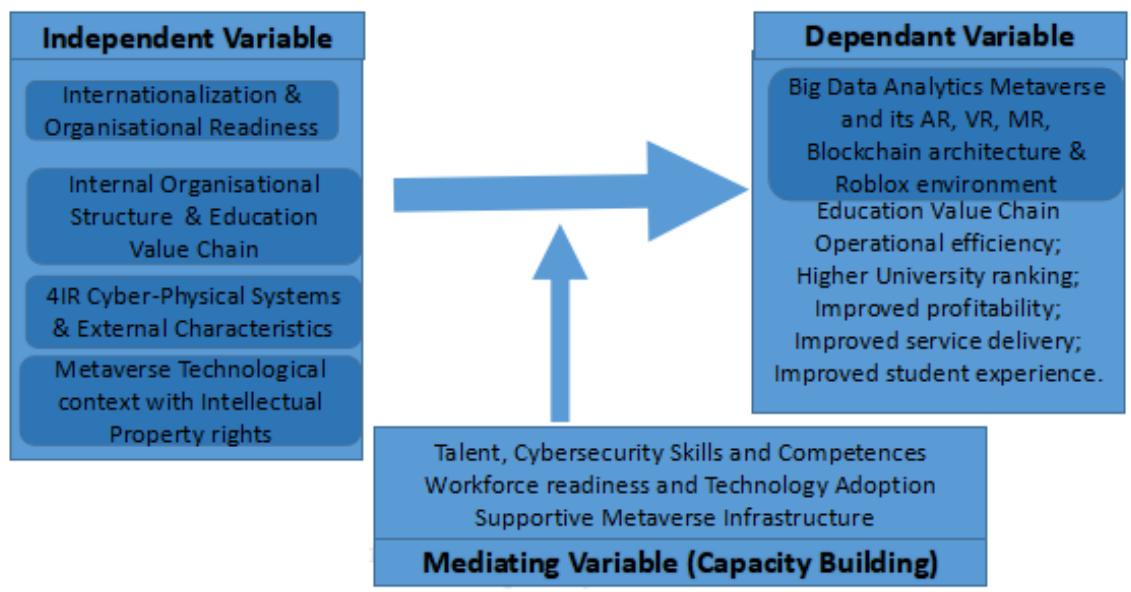 Figure 10: Big Data Analytics Framework for the Hadoop-Metaverse Environment
The sixth generation (6G) of mobile communication, which follows and improves on the fourth and fifth generations (4G and 5G), is a cutting-edge technology that combines sensing, storage, communication, control, and computational capability. Speed and latency will be the most noticeable differences between 6G and 5G. A major advantage of 6G is that it facilitates instant communication in phones, computers, wearable devices, robotics, and more. Every time mobile communication technology is updated and iterated, its different performance indicators outperform the last generation by a factor of 10 to 100. Edge intelligence powered by 6G enables the Internet of Everything and allows people, devices, and the cloud to be connected at any time and from any location [51]. Smart service applications for next-generation wireless networks are transforming our way of life and enhancing it. The effective integration and collaboration of AI technology and 6G mobile communication technology resulted in the creation of the 6G-enabled edge AI paradigm [51]. Edge AI benefits from decreased latency, a more reliable network connection, and a more secure network design thanks to 6G mobile communication technologies. The benefits of reduced latency, computing offload, and high performance come with 6G edge intelligence. The immersive and real-time physical-virtual world interaction offered by the Metaverse technical layer is a feature of the Metaverse architecture shown on Figure 11. The Metaverse is low bandwidth, low latency, provides ubiquitous access, and is reliable for consumers thanks to the enabling technologies.
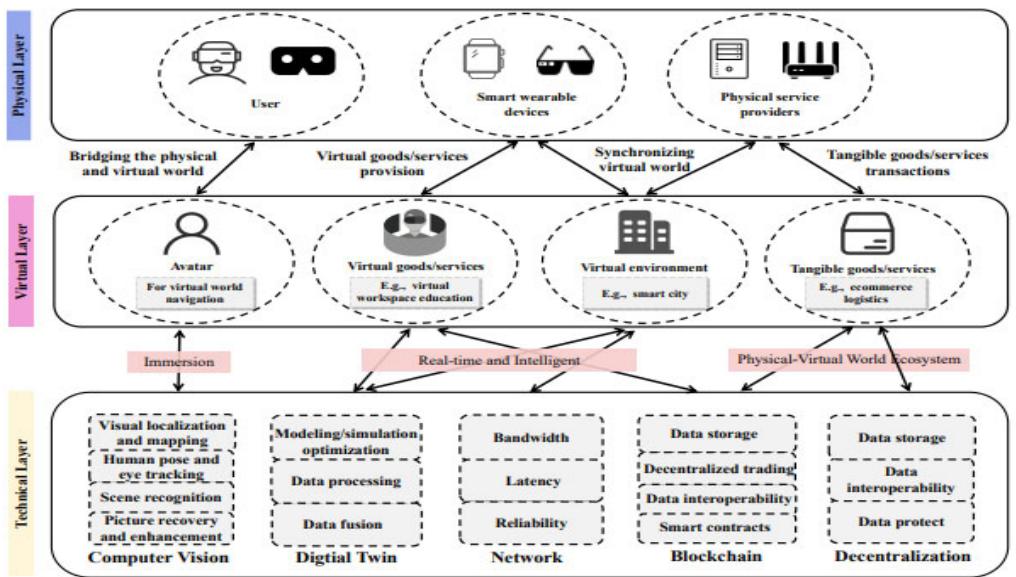 Figure 11: Metaverse Architecture with Immersive and Real-Time Physical-Virtual World (Source: [51])
The Cybersecurity model for the Cybersecurity model for a Roblox-based Metaverse architecture framework is illustrated on Figure 12.
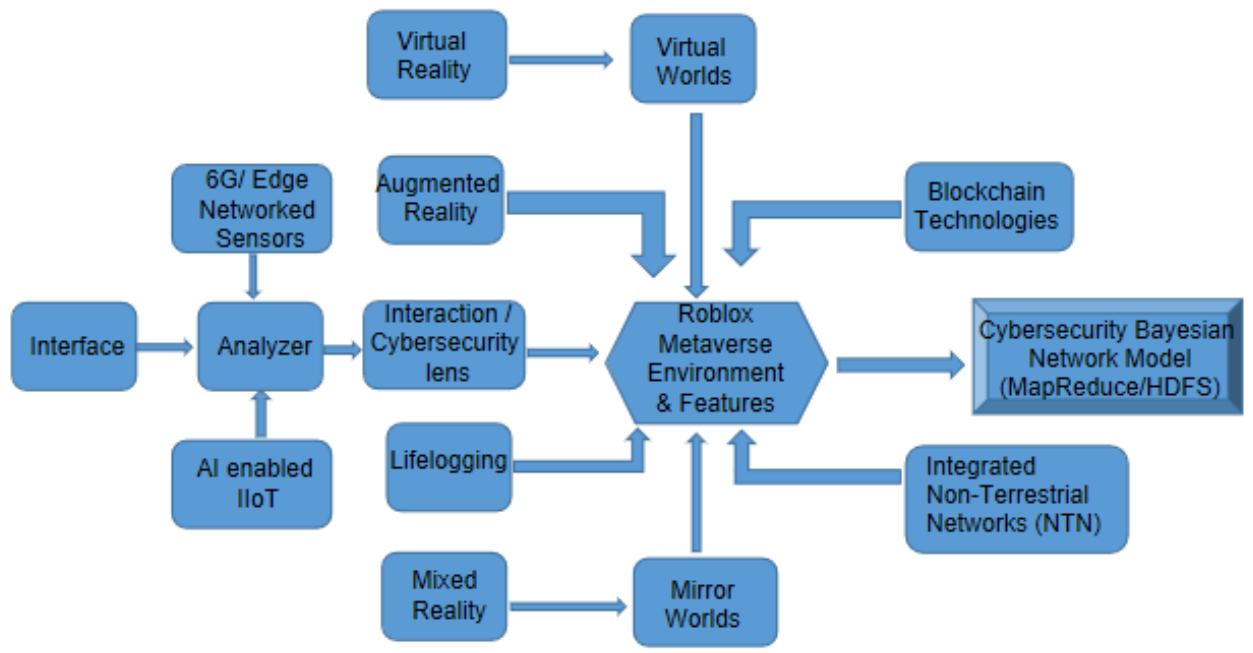 Figure 12: Cybersecurity Model for a Roblox-Based Metaverse Architecture Framework
### f) Summary Architecture Framework
The effects of internationalization, international integration, or globalization as well as the COVID-19 health emergency have caused a shift from the traditional/simulated education paradigm to zero and one as well as introduced and innovated significant changes to the teaching and learning process. Virtual reality (VR), immersive virtual reality (IVR), and augmented reality (AR) are the only three harmful tendencies in the field of education at the moment as a result of the tremendous technological transformation that humanity is undergoing [32]. In order for kids to study and engage in the new technological field in which they are born, we must first construct transformative educational settings in addition to implementing innovative emerging technologies in education. Virtual reality (VR) is seen as a philosophical, scientific, and technological turning point in the digital age. IVR can enhance the transformation of the educational process [32]. Immersive virtual reality presents a significant
short-term challenge to educational institutions as a learning tool. IVR is becoming more affordable and accessible. Roblox and other immersive learning tools make it possible to identify devices, thus it is crucial in education to take the teaching and learning process to a new level by honing and developing abilities in online and offline (synchronous and asynchronous) training. IVR facilitates the creation of simulations in which the teaching is done, with a focus on teaching and learning in the context of educational technology.
The Metaverse is a three-dimensional, real-time immersive simulation medium, and its ecology is well suited to supporting audiovisual notifications, creating an amazing setup in training or teaching environments. Nevertheless, it is challenging for different network users to participate in or even use three-dimensional world technology in the teaching/learning process due to a lack of knowledge and competence. Most importantly, making full use of the metaverse's capabilities and applying these capabilities to the digital environment "requires training in specific skills specific to the virtual world. Digital skills are what this entails. The knowledge, skills, abilities, attitudes, and tactics needed to use internet technology and the Internet are collectively referred to as "digital competencies." Every field of work or education can benefit from the immersive, multisensory 3D environment that Metaverse offers teachers.
The Cybersecurity model for a Roblox-based Metaverse architecture framework shown on Figure 12 is a Bayesian Network. Bayesian Networks (BNs) are directed acyclic graphs that have an associated probability distribution function and these graphical probabilistic models are used for multivariate analysis [3]. These BNs allow us to reason from evidence to hypotheses with regards to cyberscurity issues.
$$
P (x) = \mathsf {\Pi} ^ {\mathsf {n}} \prod_ {\mathrm {i} = 1} p (\mathrm {x} _ {\mathrm {i}} | \Psi_ {\mathrm {i}})
$$
## V. CONCLUSION
The Metaverse is a virtual iteration of the Internet as a single, universal, immersive virtual world made possible by the use of virtual reality and augmented reality headsets in futuristic and science fiction. Roblox is an open-source platform that can be used for online education to enable interactive 3D virtual environments in physical and online classrooms, with some basic cybersecurity mechanisms. In essence, Metaverse is a combination of virtual reality, augmented reality, mixed reality, blockchain, web3, cryptocurrencies, social media, etc. Metaverse provides users with a multilingual experience, which is a key requirement for successful internationalization that breaks down language barriers and enables easier and more affordable exchange programs. The metaverse has many advantages in science that outweigh disadvantages such as physical limitations when working with VR and AR. Although there are many different types of E Learning environments, metaverse based systems can also be used to provide safe and efficient environments for education and business by utilizing virtual reality technologies and continuously researching and attempting to expand learning experiences. The Metaverse roadmap, according to??? is divided into four sections: augmented reality, life logging, mirror worlds, and virtual worlds. Our ability to trust the technology that underpins virtual experiences is severely compromised as a result. Cyber security is a technique for defending against online attacks on programs, networks, and systems. The key focus of cyber security is the defense of programs, networks, and systems against harmful digital attacks. The Cyber security model for a Roblox-based Metaverse architecture framework developed is a Bayesian Network, which is a directed acyclic graph that has an associated probability distribution function which can be used for multivariate analysis. Systematic literature review of Metaverse, Virtual Reality and Augmented Reality Augmented reality was conducted. The systematic review work highlighted the Metaverse elements, digital currencies, AI applications in the virtual world, and blockchain-empowered technologies to discuss how blockchain and AI fuse with the Metaverse. Between augmented reality and virtual reality, mixed reality provides an improved version of augmented reality. The use of the metaverse in Software Engineering Education enables experiences that effectively teach software processes, allowing the student to take on the lead roles in software projects. Students do this using techniques of specific development process models, navigating in different environments, communicating with other avatars, and interacting with and viewing Unified Modeling Language diagrams in the same way that they are seen in real-world software projects.
Generating HTML Viewer...
References
46 Cites in Article
Ligia Deca,Eva Egron-Polak,Cristina Fiţ (2015). Internationalisation of Higher Education in Romanian National and Institutional Contexts.
N Mpofu,R Chikati (2013). The Leading Edge Digital Edition - [October 2013] (Volume 32, Issue 10).
Young Ernst (2015). Cybersecurity and the Internet of Things 11.
Roblox (2022). Unknown Title.
J Bailenson (2018). Experience on Demand (2018): What Virtual Reality Is, How It Works, and What It Can Do.
Cecile Meier,Jose Saorín,Alejandro Bonnet De León,Alberto Guerrero Cobos (2020). Using the Roblox Video Game Engine for Creating Virtual tours and Learning about the Sculptural Heritage.
R Pericles (2022). Metaverse or Simulacra? Roblox, Minecraft, Meta and the turn to virtual reality for education, socialisation and work.
Samreen Sadiya (2022). Humans Emerging beyond Universe with Metaverse, is it possible? How?.
D Maloney,G Freeman (2020). Falling asleep together: What makes activities in social virtual reality meaningful to users.
James Hutson (2022). Social Virtual Reality: Neurodivergence and Inclusivity in the Metaverse.
James Cummings,Jeremy Bailenson (2016). How Immersive Is Enough? A Meta-Analysis of the Effect of Immersive Technology on User Presence.
Murat Coban,Yusuf Bolat,Idris Goksu (2022). The potential of immersive virtual reality to enhance learning: A meta-analysis.
A Gaggioli (2018). Virtually social, Cyberpsycho logy, Behavior, and Social Networking.
F Fernandes,C Werner (2022). A Systematic Literature Review of the Metaverse for Software Engineering Education: Overview, Challenges and Opportunities.
R Yung,C Khoo-Lattimore (2019). New realities: a systematic literature review on virtual reality and augmented reality in tourism research.
Daeseok Kim,Tami Im (2022). A Systematic Review of Virtual Reality-Based Education Research Using Latent Dirichlet Allocation: Focus on Topic Modeling Technique.
Mun Zahiroh (2019). Cybersecurity Awareness and Digital Skills on Readiness For Change in Digital Banking.
M Hussein,C Nätterdal (2015). The Benefits of Virtual Reality in Education. A Comparison Study.
M Saunders,P Lewis,A Thornhill (2009). Research methods for business students.
William Tayler,Robert Bloomfield (2011). Norms, Conformity, and Controls.
I Jebreen (2012). Using inductive approach as research strategy in requirements engineering Year.
Santosh Nanda,Ariel Rivas,William Trochim,J Deshler (2000). Emphasis on Validation in Research: A Meta-Analysis.
L Soiferman (2010). Inductive and Deductive Approaches.
J.-E Yu (2022). Exploration of Educational Possibilities by Four Metaverse Types in Physical Education.
T Fitrial,N Simbolon,Afdaleni (2022). Possibility of Metaverse in Education: Opportunity and Threat.
Douglas Barráez-Herrera (2022). Metaverse in a virtual education context.
C Philips,Cecilia Chinda (2017). Lecturers’ Perception of Intellectual Property Rights in Universities in Rivers State.
Jeffrey Dean,Sanjay Ghemawat (2008). MapReduce.
Badrul Chowdhury,Tilmann Rabl,Pooya Saadatpanah,Jiang Du,Hans-Arno Jacobsen (2013). A BigBench Implementation in the Hadoop Ecosystem.
Mithu George,P Rasmi (2022). Performance Comparison of Apache Hadoop and Apache Spark for COVID-19 data sets.
N Akhtar,F Parwej,Y Perwej (2017). A perusal of big data classification and hadoop technology.
V Bobade (2016). Survey paper on big data and Hadoop.
S Agrawal (2011). The Next Generation of Apache Hadoop MapReduce.
D Borthakur (2010). HDFS architecture. Document on Hadoop Wiki.
A Vyas,S Ram (2017). Comparative study of MapReduce frameworks in big data analytics.
Konstantin Shvachko,Hairong Kuang,Sanjay Radia,Robert Chansler (2010). The Hadoop Distributed File System.
Tilmann Rabl,Michael Frank,Manuel Danisch,Bhaskar Gowda,Hans-Arno Jacobsen (2014). Towards a Complete BigBench Implementation.
Sudeep Tanwar,Karan Parekh,Richard Evans (2020). Blockchain-based electronic healthcare record system for healthcare 4.0 applications.
Florian Tschorsch,Bjorn Scheuermann (2016). Bitcoin and Beyond: A Technical Survey on Decentralized Digital Currencies.
Ahmed Hussein,N Arunkumar,Gustavo Ramirez-Gonzalez,Enas Abdulhay,João Tavares,Victor De Albuquerque (2018). A medical records managing and securing blockchain based system supported by a Genetic Algorithm and Discrete Wavelet Transform.
Taras Maksymyuk,Juraj Gazda,Longzhe Han,Minho Jo (2019). Blockchain-Based Intelligent Network Management for 5G and Beyond.
N Mohamed,J Al-Jaroodi (2019). Applying blockchain in industry 4.0 applications.
Riccardo Tiscini,Silvia Testarmata,Mirella Ciaburri,Emanuele Ferrari (2020). The blockchain as a sustainable business model innovation.
Michael Kramer,Linda Bitsch,Jon Hanf (2021). Blockchain and Its Impacts on Agri-Food Supply Chain Network Management.
L Chang,Z Zhang,P Li,S Xi,W Guo,Y Shen,. Wu,Y (2022). 6 G-enabled Edge AI for Metaverse: Challenges, Methods, and Future Research Directions.
No ethics committee approval was required for this article type.
Data Availability
Not applicable for this article.
How to Cite This Article
Professor Gabriel Kabanda. 2026. \u201cA Cybersecurity Model for a Roblox-based Metaverse Architecture Framework\u201d. Global Journal of Computer Science and Technology - E: Network, Web & Security GJCST-E Volume 23 (GJCST Volume 23 Issue E1).
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.