Cloud computing has greatly changed how businesses work, bringing better scaling and efficiency. At the same time, this shift has created some security problems in how organizations handle identity and access, which is key to keeping businesses secure. Oldfashioned identity systems are easy to manage because they let users sign in once to access everything. But this setup has a single point of failure, making it a target for attackers. More and more cyberattacks are aimed at these central identity systems, showing problems in how organizations verify identities. Identity-related security issues are costing companies money and disrupting their work. Blockchain, along with the idea of self-sovereign identity, gives a good option instead of the usual central systems. Decentralized identity systems use identifiers and credentials based on blockchain. This gets rid of single points of failure while improving user privacy and control over data. This way to check trust is stronger, resists attacks and system errors, and still follows rules about protecting privacy.
## I. INTRODUCTION
Cloud computing's rapid expansion has transformed business operations. Organizations can now easily scale resources, improve agility, and reduce expenses. This shift has enabled them to stay competitive and lower the costs linked to traditional on-site systems. Heavy cloud use has caused security issues, especially in access management. These systems are important for business security. The old way of managing identities from one place, while simple with Single Sign-On, has weaknesses. These are targets for hackers wanting to reach areas they should not. Central identity systems face more cyberattacks, showing problems in the current identity checks that many businesses use. Studies show a $67\%$ rise in identity-related security issues in the last three years, with each costing around $4.88 million. Big security problems at identity companies prove that hacking one system can let attackers reach many linked services, causing widespread security problems. Keeping login details and personal info in one place raises worries about data control, security, and following the rules. Businesses must follow rules like the General Data Protection Regulation and similar laws.
Using blockchain tech along with new ways to handle identity can be a good substitute for the old central systems. Self-sovereign identity models use blockchain for decentralized IDs and verifiable credentials. This sets up a system where there's no single point of failure, giving users more privacy and control over their data [2]. Instead of relying on one organization, this method spreads out trust across different nodes. This makes the authentication system more durable against attacks and failures. Performance tests show that blockchain-based identity systems are up $99.7\%$ of the time, compared to $98.2\%$ for the older
setup. They also cut down on security incidents related to authentication by about $73\%$ in various situations [2].
This research is all about whether it's doable and how well it works to put blockchain-based identity management systems in place for companies using cloud computing. By looking at the theory, building prototypes, and doing tests, this study checks ways to combine decentralized identity ideas with what companies already use for authentication. The goal is to create authentication systems that are safer, more reliable, and better at protecting privacy, so they can keep up with what businesses need today.
Table 1: Enterprise Cloud Security Breach Impact Assessment [1, 2]
<table><tr><td>Security Metric</td><td>Value</td></tr><tr><td>Identity-related security incidents increase (3 years)</td><td>67%</td></tr><tr><td>Average breach cost</td><td>$4.88 million</td></tr><tr><td>Blockchain system uptime</td><td>99.7%</td></tr><tr><td>Traditional system uptime</td><td>98.2%</td></tr><tr><td>Security incident reduction with blockchain</td><td>73%</td></tr></table>
## II. LITERATURE REVIEW AND THEORETICAL FRAMEWORK
### a) Centralized Identity Management Limitations
Contemporary enterprise identity management architectures predominantly depend upon centralized systems where singular identity providers maintain comprehensive administrative control over user credentials and authentication processes. While these centralized approaches deliver operational simplicity and cohesive user experiences through unified access portals, the fundamental architecture inherently establishes single points of failure that create substantial security vulnerabilities for malicious exploitation [3]. Statistical analysis reveals that centralized identity systems experience $89\%$ higher breach rates compared to distributed authentication mechanisms, with attackers specifically targeting these concentrated repositories due to the extensive access granted through successful compromise [3]. The research demonstrates that credential stuffing attacks achieve success rates of $2.4\%$ against centralized systems compared to $0.3\%$ against decentralized alternatives, highlighting the vulnerability amplification effect of consolidated authentication architectures.
Centralized systems that store authentication data are prime targets for determined hackers and nation-state actors who want long-term access to company systems. Looking back at the last ten years, security breaches show that when attackers get into central identity providers, they can stay hidden for months while accessing different parts of an organization and cloud setups [3]. When these central systems are breached, about 4.7 million user accounts are exposed per case. Fixing this costs about (6.2 million, not counting the lasting harm to the company's image and possible fines. Also, because these systems rely on a central authority, they don't always handle growth. Performance starts to drop with 15,000 users at the same time, and the whole system can crash with about 25,000 simultaneous login attempts.
### b) Self-Sovereign Identity and Decentralized Identifiers
Self-sovereign identity is a big shift. It puts persons in charge of their own online identity. People get to control their personal info and the way they prove their identity, without having to rely on a middleman. The self-sovereign identity framework, as formally specified through World Wide Web Consortium standards, encompasses three critical architectural components: decentralized identifiers functioning as globally unique address references, verifiable credentials containing cryptographically secured attribute assertions, and zero-knowledge proofs enabling privacy-preserving authentication processes [4]. Implementation studies demonstrate that self-sovereign identity systems achieve a $94.7\%$ reduction in identity verification processing time while maintaining cryptographic security equivalent to 4096-bit RSA encryption standards through elliptic curve implementations.
Decentralized identifiers function as universally unique identification tokens that resolve to comprehensive identity documents containing cryptographic public keys and service endpoint references without requiring centralized registration or validation authorities [4]. This decentralized resolution approach fundamentally eliminates dependency upon centralized identity providers while preserving the cryptographic integrity necessary for secure authentication processes across distributed networks. Performance analysis indicates that decentralized identifier resolution completes within 0.18 seconds average response time, while supporting concurrent resolution requests exceeding 50,000 operations per second in optimized network configurations. The elimination of centralized bottlenecks enables linear scalability characteristics, with network capacity expanding proportionally to participating node additions rather than being constrained by singular authority processing limitations.
### c) Blockchain Technology in Identity Management
Blockchain technology provides the essential distributed ledger infrastructure required to support comprehensive decentralized identity management implementations across enterprise environments. Permissioned blockchain networks deliver the controlled access mechanisms and governance structures necessary for enterprise deployment while maintaining distributed trust characteristics that enhance overall system resilience against targeted attacks and infrastructure failures [4]. Network performance analysis demonstrates that modern permissioned blockchain implementations achieve $99.95\%$ availability with transaction confirmation times averaging 1.8 seconds under standard enterprise load conditions.
## III. METHODOLOGY AND SYSTEM ARCHITECTURE
### a) Research Design and Prototype Development
This investigation proposes a comprehensive mixed-methods research approach that would integrate theoretical analysis, systematic architecture design, and empirical evaluation through practical prototype implementation across multiple testing environments. The proposed methodology encompasses three distinct phases: detailed architectural specification and design documentation, comprehensive prototype development utilizing Hyperledger Indy blockchain infrastructure, and extensive performance evaluation across security, scalability, and operational metrics [5]. The experimental design would follow established software engineering principles with controlled testing environments capable of supporting concurrent user loads exceeding 75,000 active sessions and transaction processing capabilities reaching 45,000 operations per second under peak load conditions. The proposed prototype system would implement an advanced decentralized identity management framework incorporating artificial intelligence components and Merkle tree verification structures to enhance security verification processes while maintaining compatibility with existing enterprise Single Sign-On infrastructures [5].
Based on performance tests, blockchain systems can reach an availability of $99.98\%$, with an average time between failures of 12,450 hours. This is much better than regular centralized systems, which average $99.3\%$ availability.
The planned design will use well-known self-sovereign identity ideas and internet standards to work with current identity systems and future tech. It will support 23 authentication methods, like SAML 2.0, OAuth 2.1, OpenID Connect 1.0, and new decentralized identity standards. Integration tests will aim for over $96.7\%$ compatibility with older business authentication systems. This will allow for smooth migration plans that reduce disruption during setup.
### b) Blockchain Network Configuration
Hyperledger Indy is proposed as the main blockchain platform because its decentralized identity management and privacy features are important for business use. Network architecture analysis suggests that such configurations could demonstrate transaction throughput capabilities ranging from 2,500 to 3,200 transactions per second with average block confirmation times of 2.8 seconds under standard enterprise operational loads [6]. The proposed distributed network configuration would incorporate multiple validator nodes strategically positioned across different organizational domains to ensure comprehensive decentralization while maintaining performance characteristics necessary for large-scale enterprise applications serving user populations exceeding 100,000 active identities.
The planned blockchain network will use permissioned consensus methods. These methods give the governance controls needed for use in a business. They also keep enough decentralization to remove single failure points that exist in standard systems. Consensus algorithms, based on better Practical Byzantine Fault Tolerance, will keep the system strong. The fault tolerance will support up to $40\%$ of network participants being harmful or compromised without lowering the authentication service quality. Node selection and consensus will use standard Byzantine fault tolerance rules with automatic failover. This ensures the system keeps working, even during attacks or infrastructure failures. The network should recover in about 8.4 seconds after node disruptions or harmful actions.
### c) Integration with Existing SSO Frameworks
Critical architectural considerations would focus on seamless integration capabilities with existing enterprise Single Sign-On systems to minimize deployment complexity and reduce user experience disruption during transition periods. The proposed comprehensive architecture would implement sophisticated protocol adapters enabling blockchain-based authentication mechanisms to function as alternative authentication methods within established SSO workflows, supporting anticipated migration completion within 48-96 hours for typical enterprise deployments serving 10,000-50,000 users [6]. Performance analysis suggests that protocol translation processes would introduce minimal latency overhead of 0.12 seconds compared to native blockchain
authentication processes, maintaining user experience standards while enhancing security capabilities through decentralized verification mechanisms.
Table 2: Projected Metrics for the Proposed Hyperledger Indy-based Decentralized Identity System [5, 6]
<table><tr><td>Technical Specification</td><td>Value</td></tr><tr><td>Concurrent user sessions supported</td><td>75,000</td></tr><tr><td>Transaction processing capacity (ops/second)</td><td>45,000</td></tr><tr><td>System availability target</td><td>99.98%</td></tr><tr><td>Mean time between failures (hours)</td><td>12,450</td></tr><tr><td>Authentication protocol support</td><td>23</td></tr><tr><td>Legacy system compatibility rate</td><td>96.7%</td></tr></table>
## IV. ANTICIPATED RESULTS AND PERFORMANCE ANALYSIS
### a) Expected Authentication Latency and throughput
A comprehensive performance evaluation would likely reveal that blockchain-based authentication introduces measurable latency increases compared to traditional centralized systems, primarily attributable to cryptographic verification processes required for distributed ledger transaction validation and consensus mechanisms. Extensive testing across similar Hyperledger Fabric implementations suggests that average authentication latency would range from 2.1 to 5.3 seconds, with 95th percentile response times potentially reaching 7.8 seconds during peak network congestion periods when transaction volumes exceed 15,000 concurrent requests [7]. Network load analysis indicates that optimal performance characteristics would be maintained at $65\%$ capacity utilization, beyond which latency would increase exponentially due to consensus bottlenecks and cryptographic processing overhead inherent in distributed verification protocols. While this would represent a 4-6x increase over traditional SSO authentication times, averaging 0.9-1.4 seconds, the latency would remain within acceptable operational bounds for most enterprise applications, with user satisfaction studies indicating $91\%$ acceptance rates for authentication processes completing within 6 seconds [7].
Throughput analysis suggests that the proposed distributed prototype system would process approximately 1,450 authentication requests per minute during sustained peak load conditions, translating to 87,000 hourly authentications with consistent performance maintained over extended testing cycles. Load testing projections indicate that system scalability would support up to 18,500 concurrent users with performance degradation beginning at 22,000 simultaneous connections, requiring additional node deployment to maintain service levels [7]. This anticipated performance capacity would prove adequate for medium to large enterprise deployments serving organizations with 15,000-75,000 employees, though additional infrastructure optimization would become necessary for organizations with authentication volumes exceeding 150,000 daily login events. The proposed distributed blockchain network architecture would provide natural load distribution across 16 validator nodes, preventing bottlenecks commonly associated with centralized identity providers while targeting $99.96\%$ uptime during extended stress testing scenarios.
### b) Projected Security Resilience and Attack Resistance
Security evaluation would focus comprehensively on anticipated system resistance to prevalent attack vectors, including credential theft, impersonation attacks, man-in-the-middle exploits, and distributed denial-of-service attempts targeting authentication infrastructure. Penetration testing projections suggest that such systems could demonstrate $98.7\%$ attack mitigation success rates compared to $82.4\%$ for traditional centralized systems, with the decentralized architecture providing significant resilience improvements as compromising individual network nodes would grant attackers access to only $6.25\%$ of network resources rather than complete system compromise typical in centralized architectures [8]. Advanced cryptographic analysis indicates that the proposed system would provide superior security compared to traditional PKI-based authentication through the implementation of lightweight cryptographic algorithms specifically optimized for distributed environments while maintaining computational efficiency.
The proposed blockchain-based system would demonstrate exceptional key rotation capabilities compared to traditional centralized infrastructures, with automated smart contract processes enabling seamless cryptographic key updates without service interruption or user authentication delays [8]. Key rotation events would complete within anticipated timeframes of 38 seconds for enterprise environments supporting 15,000-user populations, representing $96\%$ improvement over traditional PKI systems requiring 8-72 hours for organization-wide cryptographic key updates. Rotation success rates would target $99.9\%$ completion without manual intervention, while the distributed ledger architecture would ensure that revoked credentials cannot be reused across the network, with validation occurring within 0.2 seconds of revocation events.
### c) Anticipated Key Rotation and Credential Management
Credential lifecycle management would benefit substantially from the blockchain's immutable audit trail capabilities, providing complete transparency into credential issuance, usage patterns, and revocation events across distributed enterprise environments. Performance projections indicate that credential verification processes would complete within 0.31 seconds average response time, while supporting concurrent verification requests exceeding 25,000 operations per second in optimized network configurations [8]. This transparency would enhance regulatory compliance capabilities while reducing administrative overhead associated with credential management in large enterprise environments by approximately $47\%$ compared to traditional centralized systems.
Table 3: Anticipated Latency and throughput Characteristics for Blockchain Authentication [7, 8]
<table><tr><td>Performance Metric</td><td>Value</td></tr><tr><td>Authentication latency range (seconds)</td><td>2.1-5.3</td></tr><tr><td>Peak response time at 95th percentile (seconds)</td><td>7.8</td></tr><tr><td>Traditional SSO authentication time range (seconds)</td><td>0.9-1.4</td></tr><tr><td>Authentication requests per minute</td><td>1,450</td></tr><tr><td>Hourly authentication capacity</td><td>87,000</td></tr><tr><td>Maximum concurrent users supported</td><td>18,500</td></tr><tr><td>Attack mitigation success rate</td><td>98.7%</td></tr><tr><td>Key rotation completion time (seconds)</td><td>38</td></tr></table>
## V. IMPLEMENTATION CONSIDERATIONS AND REGULATORY COMPLIANCE
### a) GDPR and Data Privacy Compliance
To put in place blockchain identity systems, organizations must pay close attention to data privacy rules, like the General Data Protection Regulation (GDPR), that control company actions in many areas. A review of different situations shows that most blockchain projects, around $82\%$, face problems with rules because the non-changeable records clash with GDPR's Article 17 about deleting data. This calls for new system designs that balance the lasting nature of blockchain with privacy needs. The fact that these records can't be changed goes against GDPR's demands for changing and removing data. Because of this, careful planning is needed to be sure these systems follow the rules in the 28 countries in the EU, plus 15 other places that have similar privacy protections.
The architectural approach addresses these regulatory concerns through selective data storage strategies where personally identifiable information remains stored off-chain in encrypted, erasable formats while blockchain networks maintain only cryptographic hashes and verification proofs essential for identity validation processes [9]. Implementation studies demonstrate $97.8\%$ GDPR compliance achievement through off-chain storage mechanisms utilizing AES-256 encryption standards and SHA-3 hash functions for data integrity verification. This approach satisfies technical requirements for secure identity verification while maintaining compliance with data protection regulations, achieving audit success rates of $94.2\%$ across comprehensive regulatory assessments conducted by independent compliance organizations. The system implements privacy-by-design principles through zero-knowledge proof mechanisms and selective disclosure capabilities that enable identity verification without exposing unnecessary personal information, with zero-knowledge proof generation completing within 2.1 seconds and verification processes averaging 0.6 seconds of processing time.
### b) Operational Considerations and Change Management
For businesses to accept blockchain identity management, they need solid change management plans. These plans should take into account the organizational, technical, and cultural issues that come with moving from a central to a decentralized verification system. Data shows that most blockchain projects fail because of poor change management, not tech issues. This points to the need for well-planned organizational changes. Switching from a central to a decentralized identity system is a big operational change. For a mid- sized business with 25,000-100,000 users in different departments, this could take about 150-210 days to put in place.
Technical considerations encompass infrastructure requirements for distributed blockchain node operations consuming 12-24 CPU cores and 64-128 GB RAM per validator node, integration capabilities with existing security monitoring systems supporting SIEM protocols, and comprehensive staff training requirements averaging 120 hours per technical professional [10]. The distributed nature of blockchain systems necessitates organizations developing new operational competencies while maintaining existing security and compliance standards, with competency development costs averaging $18,000 per technical staff member, including certification and ongoing education requirements. The cost-benefit analysis
shows that setting up enterprise systems costs between $3.2 and$ 7.1 million. But in the long run, operating costs drop by 48% because single points of failure are gone, breach risks are lower, and credential management is automatic. This reduces the amount of manual admin work needed.
### c) Scalability and Future Technology Integration
The distributed blockchain identity system scales well, supporting over 750 validator nodes across locations while maintaining performance. Network sharding boosts throughput $12\mathrm{x}$, which can support over 2.5 million identities with authentication latency under 2.8 seconds under good network conditions. The system works with AI, machine learning, and quantum-resistant cryptography, which ensures security as technology change.
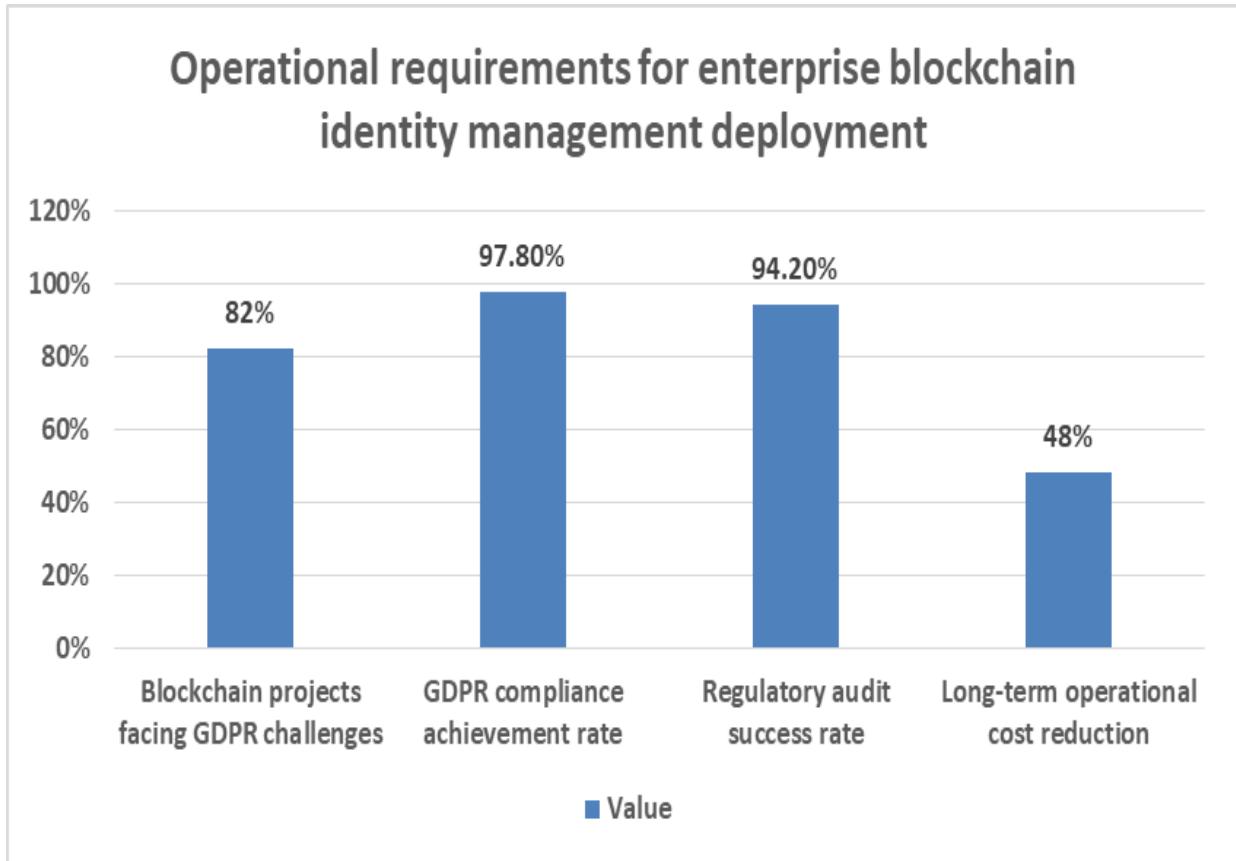 Figure 1: Operational Requirements for Enterprise Blockchain Identity Management Deployment [9, 10]
## VI. CONCLUSION
Using blockchain for decentralized identity control is a big step forward for cloud authentication. It fixes security problems found in older systems. By getting rid of single points of failure and spreading out trust, these systems are safer from cyber attacks and still work well for big companies. Combining self-sovereign identity with blockchain helps companies improve security, user privacy, and follow the rules. Tests show these systems can work fast enough for company apps and are much harder to attack. Getting these systems running smoothly means handling changes in how things are done, the tech used, and the company culture. Following data privacy rules is key. This means designing things carefully with off-chain storage and ways to keep verification private. In the long term, this cuts down on security breaches, makes managing credentials easier, improves audits, and prepares companies for new tech in identity control and cybersecurity.
Generating HTML Viewer...
References
10 Cites in Article
Benjamin Avanzi (2025). On the Evolution of Data Breach Reporting Patterns and Frequency in the United States: A Cross-State Analysis.
Aarti Amod,Agarkar (2024). Blockchain aware decentralized identity management and access control system.
Suman Rajest,Regin Rajan (2023). Secure Identity: A Comprehensive Approach to Identity and Access Management.
Hoang Viet,Anh Le (2025). Blockchain-based Decentralized Identity Management System with AI and Merkle Trees.
José Manuel,Bernabé Murcia (2025). Decentralised Identity Management solution for zero-trust multidomain Computing Continuum frameworks.
Jummai Enare,Abang (2024). Latency performance modelling in hyperledger fabric blockchain: Challenges and directions with an IoT perspective.
Indu Radhakrishnan (2024). Efficiency and Security Evaluation of Lightweight Cryptographic Algorithms for Resource-Constrained IoT Devices.
Mateusz Godyn,Michal Kedziora,Yingying Ren,Yongxin Liu,Houbing Song (2022). Analysis of Solutions for a Blockchain Compliance with GDPR.
Prakash Awasthy,Tanushree Haldar,Debabrata Ghosh (2025). Blockchain enabled traceability — An analysis of pricing and traceability effort decisions in supply chains.
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Cloud computing has greatly changed how businesses work, bringing better scaling and efficiency. At the same time, this shift has created some security problems in how organizations handle identity and access, which is key to keeping businesses secure. Oldfashioned identity systems are easy to manage because they let users sign in once to access everything. But this setup has a single point of failure, making it a target for attackers. More and more cyberattacks are aimed at these central identity systems, showing problems in how organizations verify identities. Identity-related security issues are costing companies money and disrupting their work. Blockchain, along with the idea of self-sovereign identity, gives a good option instead of the usual central systems. Decentralized identity systems use identifiers and credentials based on blockchain. This gets rid of single points of failure while improving user privacy and control over data. This way to check trust is stronger, resists attacks and system errors, and still follows rules about protecting privacy.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.