Synopsis-This paper examines the cyber security aspect of the Maritime Transportation System (MTS) to understand the scope of the MTS, the different ways in which a hacker can infiltrate the computer systems of maritime, logistics, and port infrastructures, and the potential consequences and financial impact of a marine cyber disaster on businesses, states, and individuals.
Synopsis- This paper examines the cyber security aspect of the Maritime Transportation System (MTS) to understand the scope of the MTS, the different ways in which a hacker can infiltrate the computer systems of maritime, logistics, and port infrastructures, and the potential consequences and financial impact of a marine cyber disaster on businesses, states, and individuals.
## I. INTRODUCTION
Cybersecurity refers to the protection of information, computer systems, and networks from unauthorized access or attacks. The threat level of cyber-attacks on the Maritime Transportation System (MTS) has increased by $400\%$ in recent months. The CISA identifies 16 essential infrastructures critical to national economic security which can be physical or virtual assets, systems, networks, or assets. Maintaining cyber security in the MTS is crucial for the functioning of the Sea Lanes of Commerce (SLOC) and supply chain resilience. Cybersecurity is the responsibility of regulatory authorities and all other stakeholders, as the
MTS is dependent on every supply chain. This study aims to inform the maritime audience about the threat vectors in the upcoming Artificial Intelligence (AI) era, highlighting the various components of cyber security. This article uses experimental methodology on how data/instruction is passed from LBCC LAN to SBCC LAN to conceptualize the cyber essentials using conventional equipment, protocols, and configurations. The ship's LAN is created.
## II. MARITIME TRANSPORTATION SYSTEM (MTS) MODEL
The US maritime transportation system (MTS) encompasses approximately 95,000 miles of coastline, 25,000 kilometres of waterways and 361 ports. It is a complex system of interconnected physical and modern ICT networks that must be considered to address cyber security challenges. Governments, regulators, maritime stakeholders, and commercial organizations must work together to understand and address the underlying networks within the MTS. (CISA, 2020).
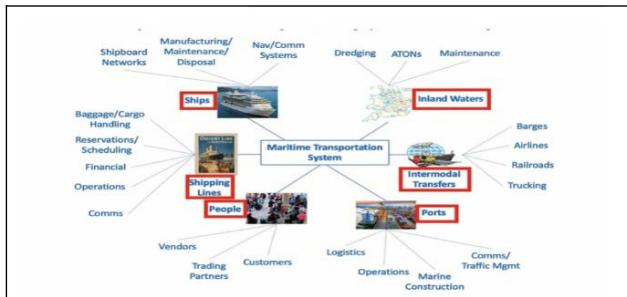 Figure 1: Maritime Transportation System (MTS)
The maritime transportation system (MTS) consists of six interconnected subsystems that are connected by Information Communication Systems (ICTs) and physical connections. It is essential to understand and conceptualize these networks to effectively address cyber security challenges within the MTS.
(CISA, 2020), (Atlantic Council, 2023)
## III. COMPARATIVE CONTEMPLATION OF BRIDGE MODELS
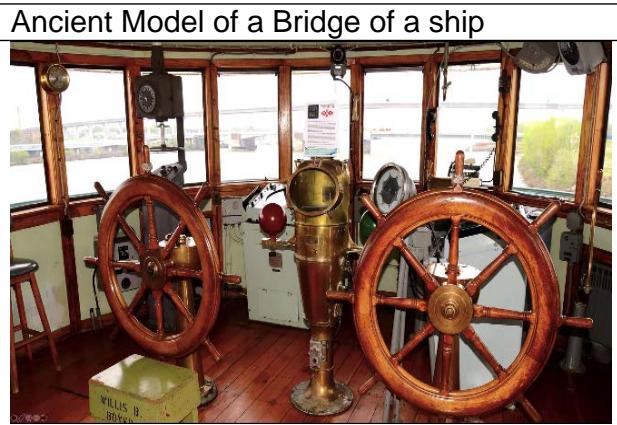
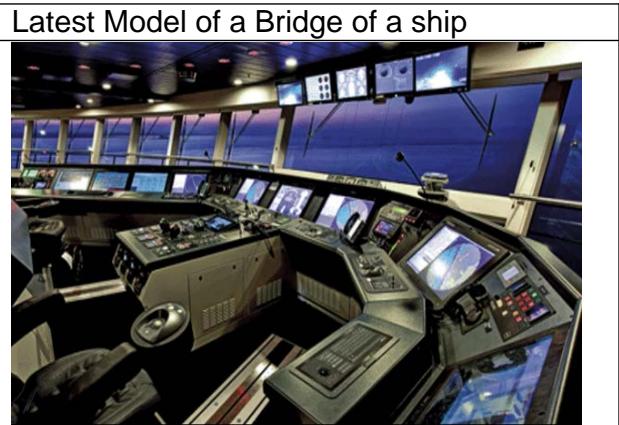 Figure 2: Ancient Vs Latest Bridge Model (Loomis et al., 2021, pp.1-50)
The key difference between ancient and the latest models is the presence of ICTs. The latter consists of networks of satellites, computers, routers, and servers in the latter. The figure illustrates the underlying network, with LBCC connected to SBCC in the latest Model.
cyber security literature. If supply chain disruptions were to occur, the monetary value could reach trillions of dollars within a matter of hours.
## IV. SHIP'S INFORMATION & COMMUNICATION TECHNOLOGY (ICT)
### a) Systems
These systems are central in the Worldwide Area Network (WWAN) and play a significant role in
 Figure 3: Ships' Core ICT Systems (Loomis et al., 2021, pp.1-50)
Therefore, ensuring the security and reliability of these ICT systems in the maritime transportation system is essential.
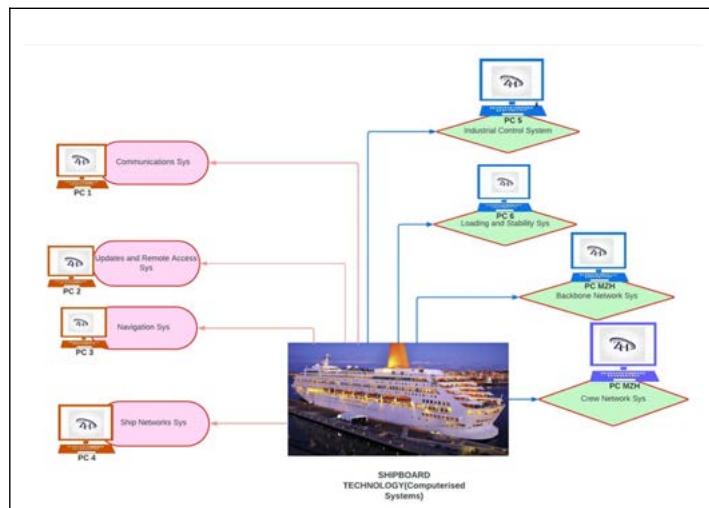 Figure 4: ICT Equipment
(Loomis et al., 2021, pp.1-50) For example: Navigation uses charts, ECDIS, GNSS Radar, and Weather.
Communications: AIS, GSM, Satellite Link, ship-to-shore, VoIP and so on. All these devices are programmed and connected to the satellite and the computer networks with a worldwide range by the internet.
## V. SHIP'S NETWORK LAN (LOCAL AREA NETWORK)
The diagram illustrates a typical ship network connected to a shore satellite that is invisible to human eyesight. The network has some components connected in series and others in parallel and is interdependent and interconnected. The network topology is a star topology, which is scalable and can easily be extended, or new ICT systems can be included.
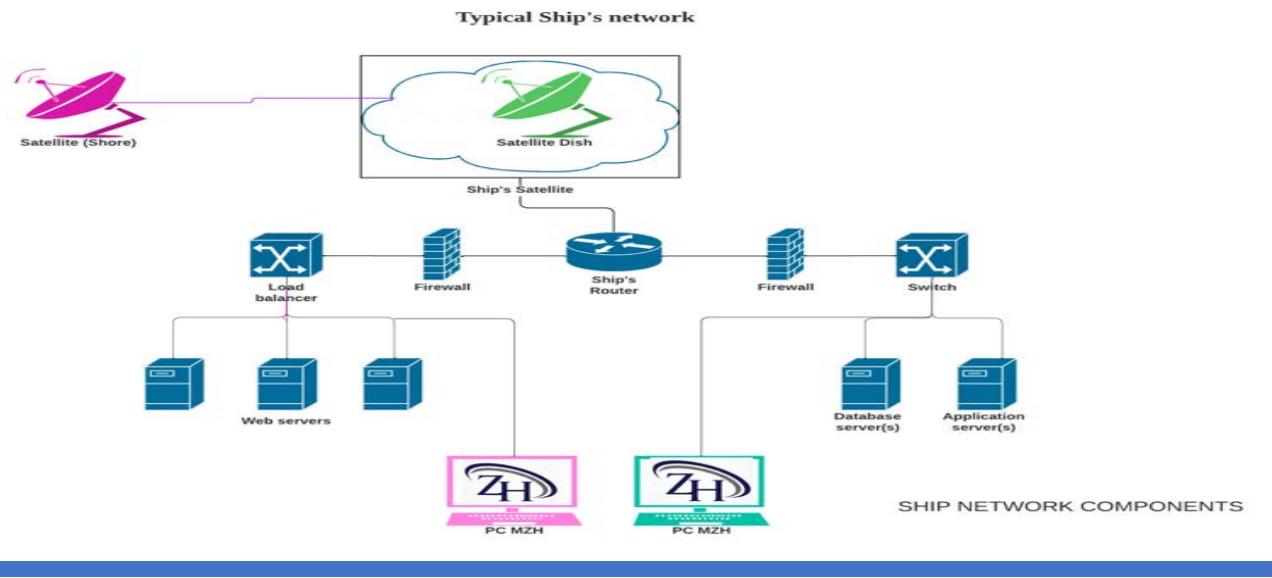 Figure 5: Ship Network Topology
However, this topology also has a drawback, where if a computer clicks a malicious link, it can install malware despite firewall security arrangements, which can have cascading impacts on servers' computers and IoT devices, leading to data being stolen, malware replication, and connecting to botnets with malicious intentions. All devices in this network require regular updates and security patches to keep the Local Area Network (LAN) safe and secure.
## VI. SHIP NETWORK TOPOLOGY (LBCC LAN TO SBCC LAN)
The simulation illustrates an autonomous model where a central PC sends instructions to the SBCC's central PC and the LBCC, using IPSec VPN tunnelling to secure data from malicious actors. However, there is a risk that some data may not be able to be encrypted due to commercial pressures, increasing the risk of data breaches. Connecting ship systems to port and logistics systems increases the risk vectors and matrix as cross-industrial network volume increases.
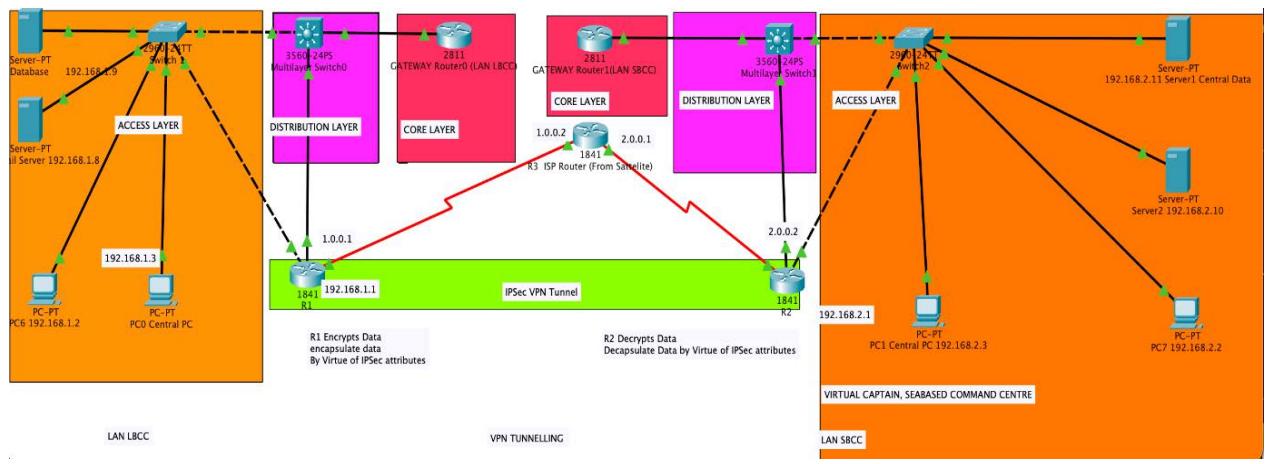 Figure 6: LAN to LAN Network Simulation
In the cyber world, all parties compete to control assets, infrastructures, and services in the supply chain (ship, port, and logistics), leading to a tug of cyber war.
## VII. COMPUTER RISK MANAGEMENT: (UOB, 2021)
The subsequent paragraphs focus on every network administrator's critical cyber security challenges. These challenges include threat vectors such as hacking, malware, and phishing, among others. Suppose shipboard management can effectively deal with these challenges. In that case, they will successfully handle maritime cyber challenges, avoiding supply chain disruptions and thwarting terrorist attacks or criminal and malicious intent on critical sea lanes of commerce (SLOC).
## VIII. KEY MARITIME CYBER CHALLENGES
The MTS computer network is a combination of LAN, WAN, and WWAN. Its main cyber security challenges include ensuring the security of networks and hardware, implementing threat monitoring, developing alternative networks, raising user awareness, and managing and configuring interfaces between networks to secure the whole network.
## IX. WHAT DOES IT MEAN CYBER SECURITY
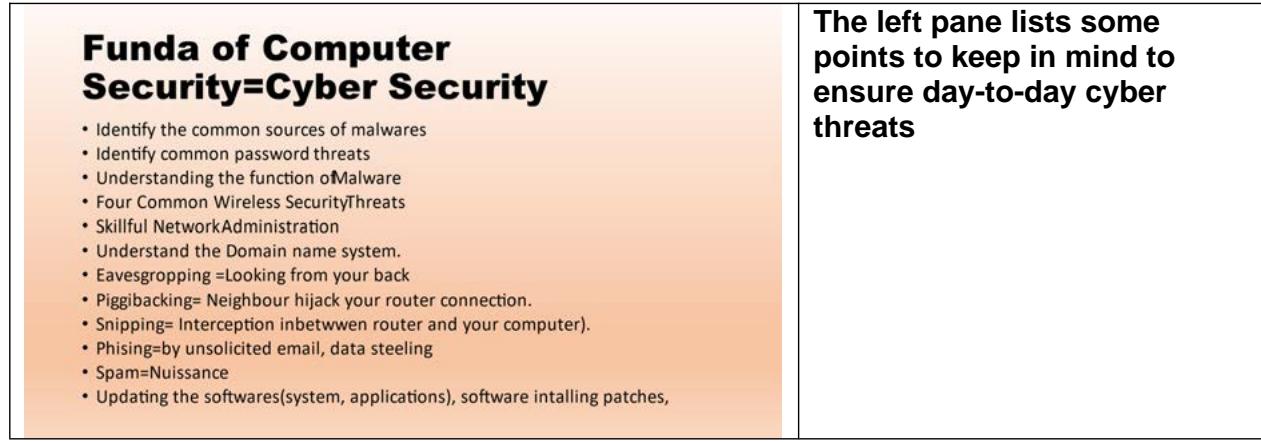 Figure 7: Fundamentals of Computer Security
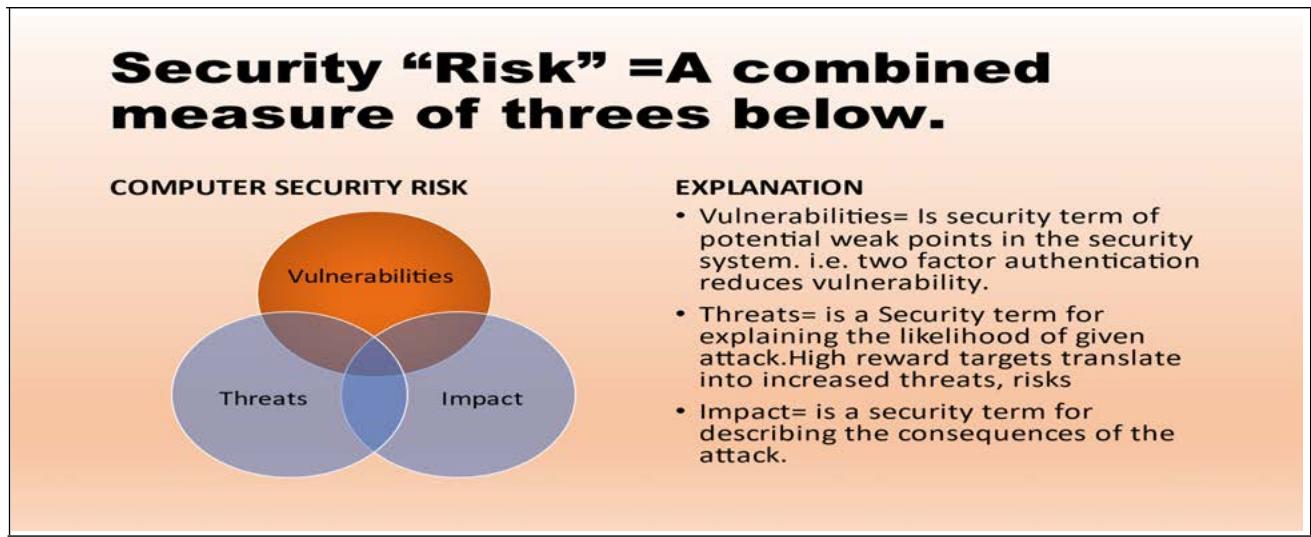 a) Overlapping Figure 8: PC RISK MODEL IN Venn Diagram (UoB,2021)
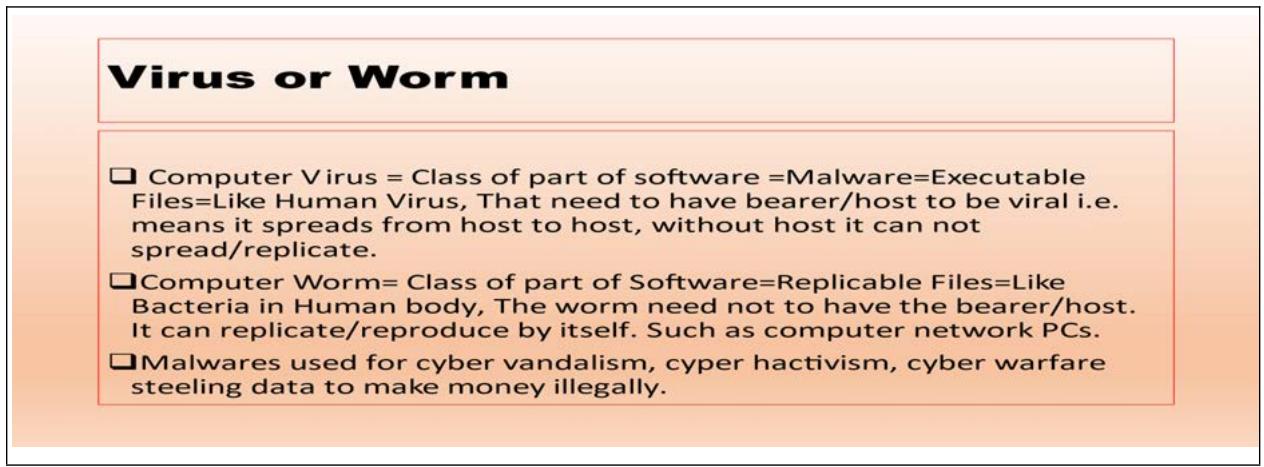 b) Viruses Figure 9: Virus or Worm Explanation
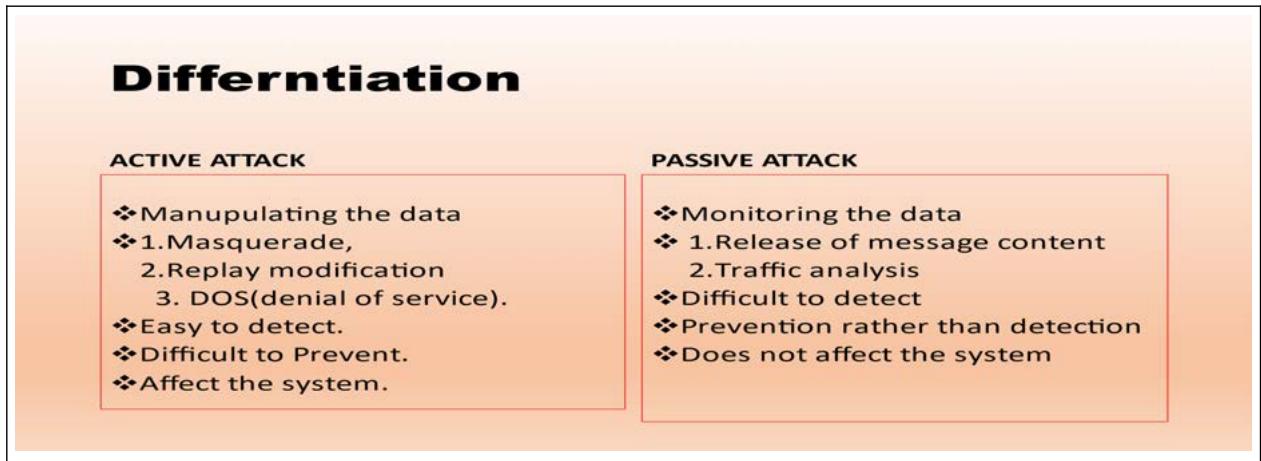 c) Attack Definition Figure 10: Attack Definition
### d) Intrusion
 Figure 11: Intruder Definition
## i. Types of Intruders
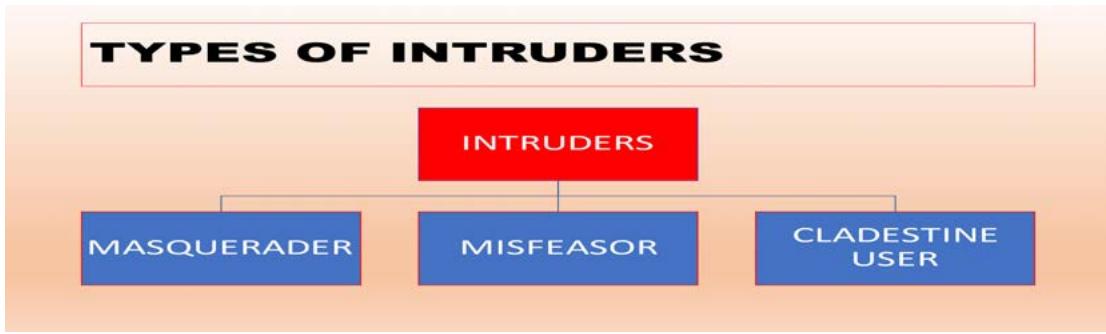 Figure 12: Types of Intruders
## X. ATTACK MODEL: (IAPH, 2020)
<table><tr><td>Types of Techniques</td><td>How Delivered and Deployed</td></tr><tr><td>Social Engineering</td><td>Phycological Manipulation to click, tempting to click on the social media posts.</td></tr><tr><td>Ransomware</td><td>Email phishing, Remote Desktop Protocol (RDP), Downloads, Pirated Software, Removable Media. (Cawthra et al., 2020)</td></tr><tr><td>Spoofing</td><td>Domain Spoofing, Email Spoofing, geolocation GPS spoofing, TCP/IP Spoofing</td></tr><tr><td>Unauthorized Access</td><td>Gaining access to a company's network, endpoint, application, or device without permission is often due to flawed or misconfigured authentication measures.</td></tr></table>
## XI. ATTACK ON MODEL
Attack on IT System
Information Technology (IT) is used to create, process, store, securely transmit, and electronically exchange data, computers, networking, storage, and other devices.
Attack on OT System
Operational technology primarily engages with the physical world by controlling industrial equipment via hardware and software.
Attack on PNT Systems
Positioning, Navigation and Timing (PNT) is a system that includes three core capabilities: positioning, which is the ability to determine the ship's location precisely and reliably, and orientation in two dimensions (or three-dimensionally when necessary).
(Loomis et al., 2021, pp.1-50)
### a) Navigation System
Modern ships use three types of navigation systems and 30 different navigational tools and resources, and communication and vessel status equipment. The ship has evolved into a floating computer network, but advanced IT interactions also increase vulnerability to specific threats as no computer equipment is $100\%$ safe by default.
### b) ICT (Information Communication Technologies)
The Internet is a complex network made up of millions of other networks. The Maritime Transportation
System (MTS) is similar in that it is a system of systems. Information and Communication Technologies (ICT) play a vital role in these systems as they allow for data storage and communication between different parts of the system. However, vulnerabilities may surface when various components interact, such as from a ship to a satellite to a base station to a command and control and tracking center. The figure illustrates real-time global ship traffic, which is too vast to account for without using ICT and its applications, with red representing cargo ships.
 Figure 16: Satellite Overview of Global Fleets (Marine Traffic, 2023)
Clicking on a vessel allows easy access to shipping details via satellite. Still, malign actors/hackers can alter the data and send false information to the satellite, base station, and vessel tracking centre, leading to inaccurate vessel location data.
### c) Spoofing Attack
The spoofing attack on the global navigation satellite system (GNSS) aims to trick a GNSS receiver by transmitting fake signals that mimic real GNSS signals or by rebroadcasting real signals at a different location or time. The spoofing can cause the receiver to estimate its position incorrectly or at a different time, as decided by the attacker. One common type of GNSS spoofing is a carry-off attack, which starts by broadcasting signals in sync with the real signals that the receiver sees and then gradually increasing the strength of the fake signals. (Ball, 2020)
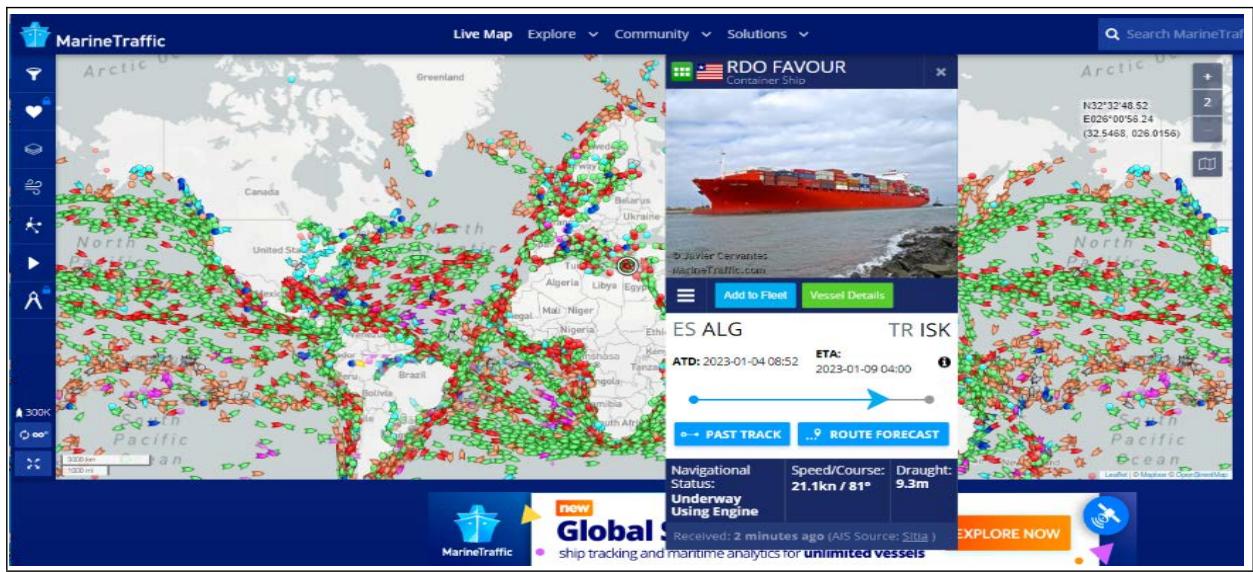 Figure 17: Ships' Data from Satellite Captures (Marine Traffic, 2023)
Ships have computerized devices connected to satellites and networks that allow for the exchange of information. However, the interconnected nature of the maritime transportation system means that when one component breaks down, it can significantly impact the entire system. (Brewin, 2013) how breakdowns can affect the entire system. The Defra Impact Calculator and methodology can be used to predict and calculate the monetary costs and impact of such breakdowns and help identify critical areas and interdependencies to mitigate risks.
## XII. IMPLICATIONS OF THE CYBER DISASTER
The implication model illustrates the relationship between computer systems and the supply chain and
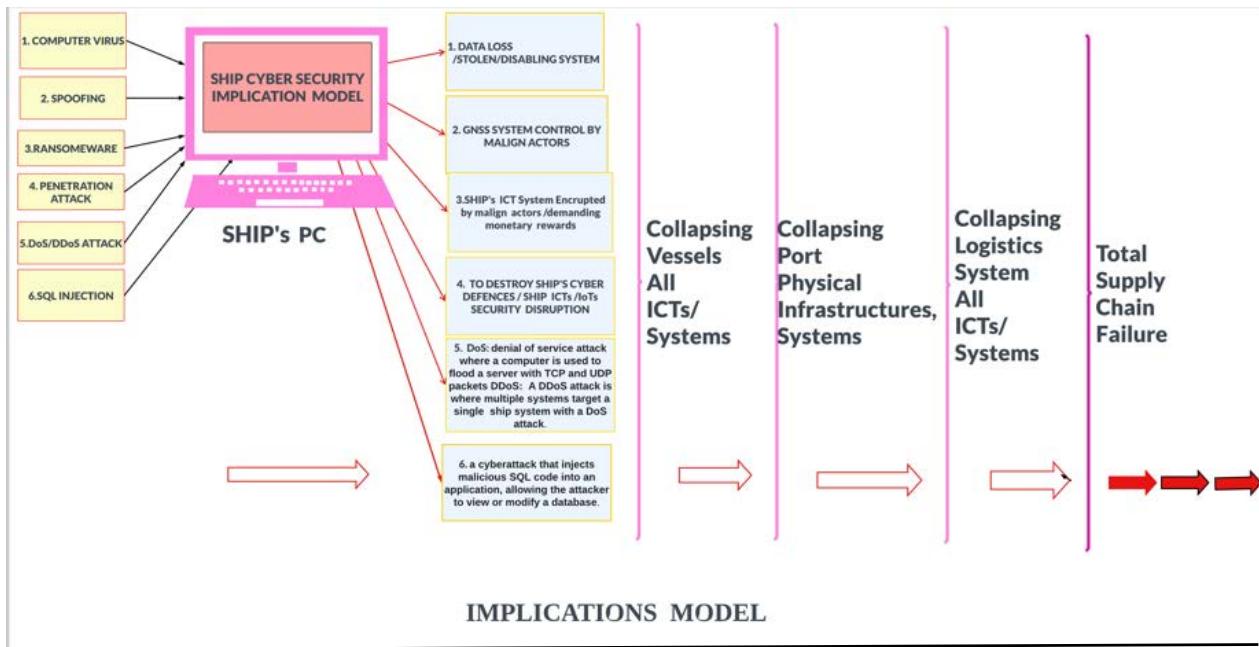 Figure 18: Cyber Disaster Implication Model
Shortages of essential items, price increases, industrial closures, unloaded shipping containers, and other factors can negatively impact a country's economic health.
## XIII. CONCLUSIONS
It is important to remember that computer viruses need hosts to harm a system, service, or infrastructure. Cyber security can be effectively managed by understanding how malicious actors can take control of an organization's assets and services. The objectives of this article are looked at /conceptualized from various angles. They will help maritime professionals promote their awareness of cyber responsibilities in their workplace to uphold supply chain resilience and the resilience of its stakeholders.
Generating HTML Viewer...
References
13 Cites in Article
B Ball (2020). Figure 5: Taxonomy of GPS spoofing attacks..
B Brewin (2013). University of Texas Team Hijacks $80 Million Yacht with Cheap GPS Spoofing Gear.
Jennifer Cawthra,Michael Ekstrom,Lauren Lusty,Julian Sexton,John Sweetnam (2020). Data Integrity: Detecting and Responding to Ransomware and Other Destructive Events.
(2020). Critical Infrastructure Sectors | CISA.
(2020). Figure 6.1. Refugee numbers have increased sharply in the last three years.
J Edwards (2019). The Russians are screwing with the GPS system to send bogus navigation data to thousands of ships.
(2023). LAS VEGAS SANDS CORP., a Nevada corporation, Plaintiff, v. UKNOWN REGISTRANTS OF www.wn0000.com, www.wn1111.com, www.wn2222.com, www.wn3333.com, www.wn4444.com, www.wn5555.com, www.wn6666.com, www.wn7777.com, www.wn8888.com, www.wn9999.com, www.112211.com, www.4456888.com, www.4489888.com, www.001148.com, and www.2289888.com, Defendants..
Mehr Nisa,Kashif Kifayat (2020). Detection of Slow Port Scanning Attacks.
D Kessler,C Gary (2021). Cyber Threats and Choke Points: How Adversaries are Leveraging Maritime Cyber Vulnerabilities for Advantage in Irregular Warfare.
C Leahy (2013). UT Austin Researchers Successfully Spoof an $80 million Yacht at Sea.
W Loomis,V Singh,G Kessler,X Bellekens (2021). RAISING THE COLORS: CYBER STATECRAFT Signaling for Cooperation on Maritime Cybersecurity.
A Reid,J Lorenz (2008). Working at a Smallto-Medium Business or ISP: CCNA Discovery Learning Guide.
No ethics committee approval was required for this article type.
Data Availability
Not applicable for this article.
How to Cite This Article
Md Ziaul Haque. 2026. \u201cCyber Security of the Maritime ICTs, threat vectors and implications on Global Sea Lanes of Commerce (SLOC).\u201d. Global Journal of Science Frontier Research - E: Marine Science GJSFR-E Volume 23 (GJSFR Volume 23 Issue E1): .
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Synopsis-This paper examines the cyber security aspect of the Maritime Transportation System (MTS) to understand the scope of the MTS, the different ways in which a hacker can infiltrate the computer systems of maritime, logistics, and port infrastructures, and the potential consequences and financial impact of a marine cyber disaster on businesses, states, and individuals.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.