Data, working knowledge (OT), and an extensive range of other practices, tools, and concepts are all comprised under the canopy term of cybersecurity. The aggressive use of info skill to bout opponents is a characteristic eye of cyberse-curity. Clienteles and security doctors are misinformed and the significant changes between these sentences are hidden by the use of the term “cybersecurity” as a key challenge and a substitute for info security or IT security. The period “cybersecurity” should only be used to mention to security practices related to selfjustifying actions involving or relying on info skill and/or working knowledge surroundings and schemes, according to the orientation of security leaders. In this paper, we define “cybersecurity” and thoughtful how info security, working skill security (OTS), IT security, and other related punishments and practices, such as cyber protection, are connected to each additional and how they are practically in agreement with the nationwide cybersecurity plan, whether it be present or deliberate.
## I. INTRODUCTION
Armed organizations have been using cybersecurity techniques for more than ten years. The phrase has been used in many different contexts in new years, numerous of which bear slight or no relation to the phrase's unique sense. The misappropriation of the term confuses the rank of the procedures that syndicate info security, working skill (OT) safety, and IT safety procedures related to numerical possessions to form the cybersecurity discipline. Cyber defense examines the numerous threats that could exist for the given setting with a sympathizer of the particular setting. The strategies obligatory to protect against malicious attacks or amidifications are then industrialized and applied with its help. Cyber resistance includes a wide range of varied doings for both the defense of the board object and for the rapid reply to a danger scenery.
These might include creation the setting fewest inviting to possible assailants, meaningful where subtle data and critical sites are, putt preemptive events in place to make bouts costly, having the aptitude to notice bouts, and having response and reply competences. In order to determine the routes and regions that attackers might use, cyber defense also performs technical analysis [1].
## II. REVIEW OF PREVIOUS WORK
Similar to how military skill has travelled into noncom-batant businesses, military jargon has entered a non-military contexts. Similar changes have been experienced by additional terms, such as progressive tenacious danger [2]. A change in terminology has been frequently advantageous because it improves the level of specificity in discussions of technological operations. But when a term's distinctive meaning is lost or diminished during the transition to a new context, its usefulness is diminished.
### a) Cybersecurity
Meaning: Cybersecurity is the ascendancy, growth, organi-zation and usage of data safety, OT safety, and IT security tools and methods for attaining controlling obedience, defensive possessions and conciliatory the possessions of opponents [2]. The authors mentioned above claim that cybersecurity.
1. Is a subset of the performs found in information safety, operational safety, offensive safety, and IT safety;
2. Employs the gears and methods of info security, working security, and IT safety to reduce weaknesses, preserve system honesty, restrict access to authorized users, and protect possessions;
3. Comprises the growth and usage of aggressive IT- or OT-based bouts in contradiction of opponents, and (4) ropes info pledge objects (for example, paper documents).
4. Supports information pledge goals in a digital setting, but excludes analogue media security. But, in the similar period, cyber security is not
1. Just used as a substitute for info safety, OT security, or IT safety; and
2. Used to protect an enterprise from criminal activity.

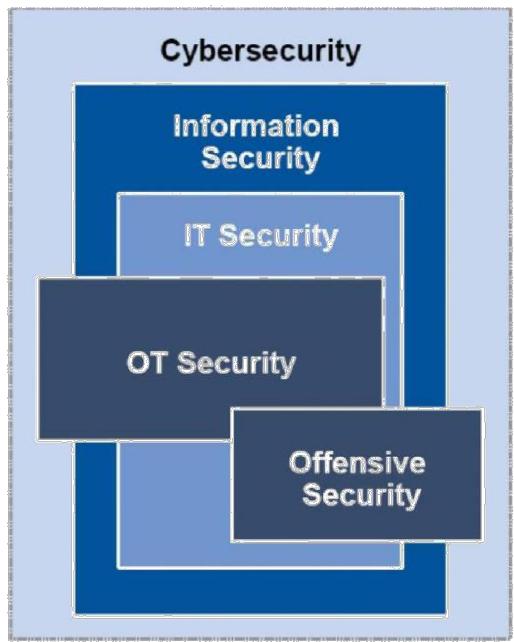 Figure 1: Components of Cybersecurity
3. Cyber warfare - although the term's definition is still debatable, it is generally agreed that "cyber warfare" mentions to the application of cybersecurity tools to combat situations. This is a complex area, and information warfare and physical attacks on infrastructure (such as the destruction of property and machinery) should not be confused with one another.
4. Cyberterrorism refers to the usage cybersecurity practices as a component of a guerilla movement or action, much like cyber warfare does.
5. Cybercrime. The term "cybercrime" simply mentions to criminal attacks that use IT infrastructure. Cybersecurity is unrelated to it.
Suitable usages of "cybersecurity" [2] would be the resulting:
1. The section increased its investment in cybersecurity in reply threat, danger valuations to enable the discount of weaknesses and enhanced competences for attacks
2. Integration of OT and IT security programmed inside the cybersecurity team allows for more comprehensive replies to intimidating.
3. A variety of cybersecurity strategies are used by the "group Anonymous to further its goals (use of offensive capabilities).
However, there are some instances where the term "cyberse-curity" is used improperly:
1. The stock's cybersecurity plan recommends the use of whole drive encryption to reduce laptop theft. (This paragraph outlines a fundamental IT security action.)
2. The cybersecurity policy requires all CAM schemes on the shop floor to use strong passwords. This explains a Cyber defense.
Despite their widespread use in the television and in nation-wide and global organizational statements, there are no universal definitions for terms used in the cyberspace. Instead, they are unspoken to nasty dissimilar belongings by dissimilar states and governments [3]. Though, [1] delivers the following meaning and additional clarification of the term "cyber defense": A processed net protection mechanism known as "cyber defense" comprises reply to threats, dangerous sub-structure defense, and info pledge for businesses, governments, and other possible nets. To safeguard that no substructure or data is cooperating, cyber protection emphases on stopping, detection, and quickly replying to attacks or intimidating. Cyber defense is crucial for the majority of entities in instruction to protect subtle info and possessions due to the upsurge in the capacity and difficulty of cyber attacks. The much-needed pledge to carry out procedures and actions without worrying about intimidating is provided by cyber defense. It assists in improving the most efficient use of resources and security strategy. Cyber protection, also assistance in enhancing the efficiency of security expenditures and resources, chiefly in sensitive areas. The United States (US) Section of Protection (DoD) has clear a new idea, Active Cyber Defense (ACD), as DoD's coordinated, real-time competence to uncover, notice, analyses, and alleviate intimidating and susceptibilities [4]. This was done in response to the need to hurry discovery of and response to hateful net actors.
## III. CYBER OPERATIONS
Cyber processes include a wide range of tasks including cyber organization, cyber attack, misuse, and cyber defense. These actions are by their very nature preventative, protective, and recuperative. Here, we'll talk about ACD as a branch of cyber defense that emphases on integrating and automating a variety of services and devices to carry out reply movements in a timely manner.
A CD is made up of a number of rational purposes that capture information from enterprise-level building to working realization with the main goal of becoming a functioning constituent of the Ministry of Defense's cyber processes to aid in defending the republic from adversaries with a focus on the internet. The essential to be safe, which comprises the ideas of, defensive, aggressive, and defensive amongst the warfighter areas of land, sea, air, space, and cyber, is one of the many requirements of war-fighter processes. Cyber is both a standalone domain with specific requirements for cyber defense and a mixing competence in the other areas [8]. Proactive, active, and regenerative are three complementary types of cyber defense. "Proactive" activities, maintain peak performance for mission functions and harden the cyber environment. "Active" activities "stop" or "limit" adversarial cyber action's harm in a time that is relevant to cyberspace. After a successful cyberattack, "reactive" activities bring efficiency or competence back. A shared outline of mechanization that comprises ACD as a subsection of combined cyber defense unites these categories to form a continuum of cybersecurity activities that take place continuously and concurrently on the nets. This article focuses on ACD [8].
Cyber defense also includes making actuarial-style predictions of the future and using non-real-time big-data analytics to discover tendencies in past information sources. Physical proximity and time are required for attacks in non-cyber domains to be carried out. Anyone with a Net joining is a possible member in this global fight space, making cyber sole in that there is no requirement for physical proximity to carry out a bat and that an attack can be carried out in a significantly shorter amount of time. By mixing numerous responses to deliver reply actions in cyber-relevant period, ACD addresses the significantly decreased time needed for a successful attack. The term "cyber-relevant time," which accommodates the demands of the battle space, is intentionally ambiguous.
The cyber-relevant period ranges from moments to microseconds if the battleground is a Dominant Dispensation Unit (CPU) and Random Access Memory (RAM), and the fighters are competing package requests. Cyber relevant time ranges from mass to seconds if the fight interplanetary is amid two computers that are bodily near to one another. Cyber-relevant time is instants in a battle interplanetary amid two computers on conflicting flanks of the planet interacts via cable links. Cyber pertinent time ranges from instants to minutes with live operators and the delays brought on by reasoning dispensation, keystrokes, and mouse clicks. As the adversary gets smarter and faster, the requirements for ACD rise [8]. Decision support algorithms used in the ACD sense-making process may be influenced by these analytics, which may be fed data from the ACD monitoring activity. These past and upcoming analytics, however, fall outdoor the purview of real-time dispensation and, consequently, fall outdoor the purview of ACD.
## IV. BASIC NOTIONS
In instruction to efficiently address the security amidinations in modern cyberspace, the Plan aims to attain a stable and synchronized reply from various organizations on behalf of all social subdivisions. The Plan acknowledges the standards that must be endangered, the appropriate organizations, and the steps necessary to implement such protection in a system-atic way. The Strategy is a declaration of the stakeholders' commitment to acting in their individual spheres of influence, collaborating with one another, and exchanging the essential data. It is a declaration of their willingness to last their own improvement and growth so that Croatian Internet will be structured, accessible, open, and secure. The approach to cyberspace is envisioned in the plan and act plan for its application as the society's virtual measurement. The aim of the Strategy and its implementation through the use of the events outlined in the Act plan is thus reliable with the European Union's Cybersecurity Plan [13] and is focused on achieving the highest level of capability and organization amongst all facets of our civilization in order to effectively implement the law and protect self-governing values in the virtual, or cyber, measurement of today's civilization. Only a common, effectively coordinated strategy involving a wide range of various institutions accountable for various sectors can accomplish such a goal. This is due to the very complicated field of cyber security, which now encompasses all facets of society and far surpasses the technical field from which it originally emerged with the fast growth of the Net and related info and message skills.
Therefore, the important problem in cyber security is one group, which is solved in the Plan by better and more real communication between all societal sections, making the most of the already-existing forms and their lawful obligations. Smearing the events outlined in the Action plan for each separate, impartial of the Plan should help achieve the documented goals in various areas of cyber security. The plan will be implemented in large part within the outline of the existing coffers of the forms capable for the activities in a given amount and the forms that will also be complicated, according to the description of the events obtainable in the Act plan for the application of the plan. The additional worth of these existing funds and other capitals is attained through structural events for better coordination and coordination in the work of numerous forms on related activities, a more effective information exchange, and, generally, through the interaction of various organizations and civilization subdivisions that have up until now not been adequately linked and synchronized when it originates to the doings connected to cyberspace. Adopting the Plan and Action Plan and implementing a methodical and all-encompassing method for cyber security are intended to accomplish an amount of goals that are crucial for the advancement of the whole civilization, in specific:
1. A methodical approach to the request and growth of the nationwide lawful outline version for the new, cyber measurement of the civilization.
2. Putting into action initiatives and strategies to increase the safety, dependability, and resilience of cyberspace;
3. establishing a more effective information-sharing system to guarantee an advanced standard of overall care in cyberspace.
4. Increasing the security consciousness of all internet users.
5. Promoting the creation of synchronized educational aut-tomatic. Encourage research and growth, chiefly in the field of e-services.
6. A methodical strategy for international cyber security cooperation. The practice of method selected to define the Strategy's fillings was founded on identifying the over-all objectives of the Plan, the societal subdivisions it enclosed, and the fundamental values of method to the Strategy's application. At this stage of the information society's development, Croatia is divided into societal segments considered to be most important for cyber security. The following are the cyber security domains that were chosen:
7. Public communications infrastructure, e-government substructure, and electric financial facilities are further broken down into electric message and information substructure and services.
8. Critical infrastructure for communication and information, cybercrime management.
The Strategy not only acknowledges the cyber security areas, but also their relationships with one another, safeguarding synchronized preparation of all cooperative doings and capitals in the aforementioned cyber security parts. The following connections between the various aspects of fake security have been chosen:
1. Data security.
2. Coordinating practical efforts to address computer security incidents.
3. Collaboration on a global scale.
4. Cybersecurity education, research, development, and awareness-building. The Plan is based on the current laws and obligations, but it acknowledges the need for some laws to be changed through the application of the Action Plan's events and synchronized with the knowledge supplies of the civilization's virtual measurement, which has previously become an essential component of all citizens' personal and expert lives as well as their daily activities.
Adopting the Strategy won't immediately address all the issues that have arisen and accumulated as a result of the rapid globalization of society and technological advancement over the past 20 years, issues that are now present in every aspect of our society.
Presenting long-term and methodical care for all upcoming tests in the society's virtual measurement through the Strategy is unquestionably the first step to a methodical and permanent development of the present national in the field of cyber security. This is crucial to the society's continued development.
## V. GENERAL GOALS OF THE STRATEGY
Submission and improvement of the nationwide legal outline using a systematic approach, custody in mind the coordination with global duties and trends in worldwide cyber security, to account for the new, cyber measurement of civilization; pursuing actions and events to strengthen cyberspace's security, pliability, and dependability that must be taken to safeguard the accessibility, integrity, and privacy of the various groups of info used in cyberspace, both by the breadwinners of numerous electric and substructure services and by the users, i.e., all legal objects and people whose info schemes are linked to Internet; founding a device for info sharing that is more effective and required for a advanced equal of overall safety in cyberspace, wherein each investor is required to ensure the application of passable and consistent values of information defense, particularly with regard to certain groups of information; raising security awareness among all internet users using a plan that takes into account the unique characteristics of the community and secluded sectors, as well as those of individuals and legal entities, and that incorporates the outline of the essential instructive components into regular and additional school activities as well as the planning and execution of various creativities aimed at humanizing the over-all public about specific present issues in this part; encouraging the creation of unified educational programmed in colleges and universities through beleaguered and specialized sequences, by fusing the moot, public, and business sectors; fostering the growth of e-services by establishing the necessary minimal security standards and increasing user trust in e-services; encouraging coordinated efforts between the academic, commercial, and public sectors by stimulating research and development; a methodical approach to international cooperation that enables effective knowledge transfer and synchronized info distribution among the various national establishments, organizations, and societal sectors that are competent, with the goal of identifying and developing competences for successful engagement in commercial doings in a global setting.
## VI. SECTORS OF THE CIVILIZATION AND FORMS OF COOPERATION OF CYBERSECURITY STAKEHOLDERS
The scope of this Strategy was defined by defining the subdivisions of civilization and what they mean for the drives of this Plan, as well as the ways in which the stakeholders in cyber security cooperate. Following are the subdivisions of civilization and their meanings for the Plan:
1. The public sector, which includes a variety of competent authorities that are Strategy stakeholders, other state establishments, bodies of local and local self-government units, lawful objects with community establishments and organizations that represent Internet users in a variety of ways, and entities required to implement Strategy-related measures.
2. The academic sector, working closely with the state establishments, who are the Strategy's investors, and other educational organizations from the public and financial subdivisions, who in numerous ways represent operators of cyberspace and objects required to implement the Strategy's regulations.
3. The financial subdivision in close coordination with the pertinent state and controlling bodies that are the Strat-egy's investors, particularly the legal entities subject to special rules pertaining to dangerous substructures and defense, as well as all other legal objects and commercial objects on behalf of the users of cyberspace in various ways and objects required to implement the Strategy's events, with all of those lawful and commercial entities' unique characteristics.
4. The general public, which includes all operators of message and information skills. The level of security in cyberspace has a variety of effects on the populace. It also refers to people whose data are in cyberspace, but who do not actively use it.
The following are the types of stakeholder collaboration in cyber security that the Strategy envisions:
1. Intergovernmental coordination.
2. Cross-country collaboration between the community, moot, and business subdivisions.
3. Discussion with absorbed parties, and communication with the populace.
4. Global collaboration among those involved in cybersecurity.
According to competencies, capabilities, and objectives as well as the functionaries expounded cyber security parts outlined in the Plan, all of these forms of collaboration are carried out in a systematic and synchronized way.
## VII. ANALYSIS AND RESULTS OF MEASURES APPLICATION
The treated data are related to 77 measures (33 area-level events and 44 link-level area-level measures) registered with the Act Plan, which support a total of 35 specific goals and 8 over-all formats in the Plan developed in 5 areas-level and 4 link-level cyber security initiatives. Teamwork is the connection between actions taken to achieve both specific and general formats. For the strategy Plan and Act Plan's approach and drafting, as well as for some of the region's nations, a reference model has been created. The strategy was methodical, clear, and all-inclusive. Analysis of a worldwide movement involving the hateful code behind Wanna Cry was also done in terms of approximations, i.e., lessened injury and learned educations.
The journalism arrangement allows for four degree interpretations on the rank of application: Fully applied/applied, ap-plied/carried out, applied/applied to a lesser grade/not started, and all events of the Act Plan have clear application indicators. Out of the 30 pertinent cyber security organizations in the Republic of Croatia, data from the accompanying reports of individual measures, along with analyses conducted in specific areas and the connections between those areas and those clear in the Policy's objectives and Action Plan application, have been processed. The consequences are as shadows:
### a) For the Following Areas
1. Community Electric Transportations (3 Events): The Action Plan identified three Measures based on the Strategy's three goals. Application pointers include two short-term events with a 12-month limit for application (since the Strategy's adoption) and one long-term amount.
2. Electric organization (8 measures): The plan has three objects, and the act strategy has eight events that are both consecutive and reliant on, have real implementation pointers that are descriptive, and have deadlines for application. The 2016 report does not include any information on how the measures were put into action. The main issue is the lack of adequate coordination between information technology development strategies and projects and security supplies.
3. Electric monetary facilities (4 measures): In this priority area, the Plan has established two planned goals, and Act Plan 4 assesses the precise
application deadlines and indicators that have already been met. The reports succumbed have demonstrated that while the events are being applied, they are not yet completely realized. 33 measures are present in all areas.
### b) For regional links
1. Information Defense (6 measures): The Plan has rec-ognized five objects, and the Act Strategy calls for six actions, with one action being implemented continuously for four actions for 12 or 24 months after the Strategy's adoption or the start of implementation, and one action's implementation being contingent upon the acceptance of EU orders.
2. Practical Organization in Computer Security Events (5 Measures): The Plan outlines three goals, and the Act Strategy for achieving these objectives includes five measures, one of which must be put into action 12 months after the Strategy's adoption while the other four must be continued unceasingly.
3. Global Co-operation (6 Measures): The Plan has set six objects, and the Act Plan calls for six actions to achieve these objectives. These actions must be implemented consistently and in a way that promotes success.
4. Teaching, Research, Growth, and Improvement of Cyber Security (27 Measures): The Plan outlines three objects, and the Act Strategy contain 27 measures to help achieve these objectives. Of these measures, three have implementation deadlines in 2017-2018, two have deadlines of 6 or 12 months from the acceptance of the Plan, and the residual 22 should be approved out unceasingly.
The need for much healthier, exercise of lecturers at various heights and types of teaching, as well as much greater consistency in cyber security, is a major problem. There are 44 measures in all of the links. Total, there are 77 measures. By implementing the Act Plan events that provision the exact and overall objects of the Plan, it can be inferred from the results above that the Strategy 2016 was realized in agreement with the capabilities or appointment of all the investors designated by the Manager and the Assembly.
### c) Cyber Defense
Despite their widespread use in the television and in nationalwide and global organizational statements, there are no universal definitions for terms used in the cyberspace. Instead, they are unspoken to nasty dissimilar belongings by dissimilar states and governments [3]. Though, [1] delivers the following meaning and additional clarification of the term "cyber defense": A processor net protection mechanism known as "cyber defense" comprises reply to threats, dangerous substructure defense, and info pledge for businesses, governments, and other possible nets.
To safeguard that no substructure or data is cooperated, cyber protection emphases on stopping, detection, and quickly replying to attacks or intimidating. Cyber defense is crucial for the majority of entities in instruction to protect subtle info and possessions due to the upsurge in the capacity and difficulty of cyberattacks. The much-needed pledge to carry out procedures and actions without worrying about intimidating is provided by cyber defense. It assists in improving the most efficient use of resources and security strategy. Cyber protection also assists in enhancing the efficiency of security expenditures and resources, chiefly in sensitive areas. The United States (US) Section of Protection (DoD) has clear a new idea, Active Cyber Defense (ACD), as DoD's coordinated, real-time competence to uncover, notice, analyses, and alleviate intimidating and susceptibilities [4]. This was done in response to the need to hurry discovery of and response to hateful net actors.
### d) People-Centric Security
A plan that offers another to traditional information security practices is called "people-centric security" (PCS). PCS seeks to raid a balance amid employee agility and risk discount. It is a calculated method of information security that places less emphasis on limiting, preventative security measures and more on personal responsibility and trust. The old-style control-centric method to info security is flattering more and more impracticable in environments where technology, business, and risk are evolving quickly and becoming ever more complex.
Security directors in companies with the right ethos should look into whether some or all of PCS's ideas and precepts can be applied to their security plans. Such a study ought to point out instances in which a trust-based, cost-effective security strategy will be made possible by a more people-centric approach [5].
PCS is founded on a number of fundamental principles as well as on an individual's rights and associated obligations. The underlying idea behind PCS is that workers have sure human rights. These, however, are connected to particular duties. These human rights and duties are founded on the sympathetic that, if a being bombs to achieve his or her obligations or bombs to act in a way that compliments the human rights of his or her classmates and other investors in the initiative, that person will face consequences.
1. This agreement of rights and obligations fosters a sense of codependency among employees, taking advantage of the social capital already present within the company.
2. According to PCS principles, transparent preventive controls, as opposed to intrusive preventative controls, should be prioritized over detectable and reactive controls.
3. PCS favors maximizing a trust environment in which personal initiative and autonomy are promoted.
4. PCS requires executive awareness and support, as well as an open, trust-based business ethos.
5. According to PCS principles, people must have the necessary information to comprehend their rights, obli-gations, and related choices.
On the other pointer, PCS is not
1. A spare for shared intelligence, defense in complexity security,
2. A loosening of safety supplies or social values,
3. Individuality organization, not exactly concentrating on an individual's digital identity,
4. Targeted at employees of the enterprise rather than all individuals, and
5. (Almost) security consciousness and exercise [3].
e) Methodology
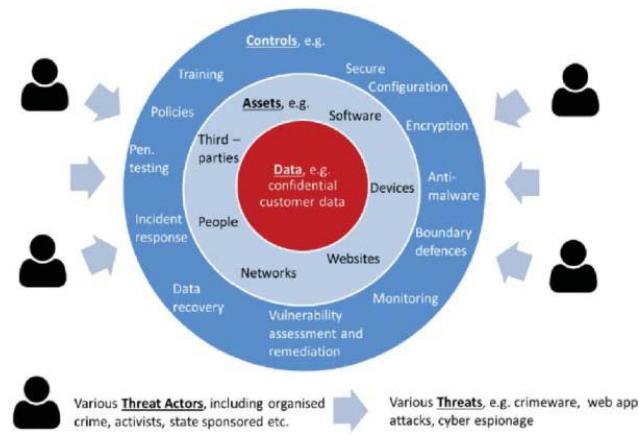
Illustrates important cyber security elements and connections:
1. Data are stowed, treated, and connected with, by, or to Possessions such as package, nets, plans, sites, persons, and 3rd gatherings
2. Information is stowed, treated, and connected with, by, or to Assets, in the majority of bags intimate data, such as client records or other valued info.
3. Danger Performers, including organized corruption bands, campaigners, and nation conditions, will use Intimidations to access Data, usually through or by targeting Possessions.
4. Threat-resistance controls are frequently practically to Possessions and sporadically straight to Data.
5. Approximately panels, like mobile device encoding, guard against particular threats, like the loss or robbery of moveable plans, whereas other panels, like package patching, guard in contradiction of a variety of intimi-dations, like somewhere, web app bouts, cyber spying, etc.
6. Intimidations will try to take advantage of Controls' flaws (or vulnerabilities) to access Data.
7. The group will be able to protect itself against the Threat if the appropriate Panels are practical to the appropriate Possessions and they are applied efficiently compared to the equal of Danger. If this is not the circumstance, there will be a data opening.
## VIII. CYBERSECURITY STRATEGY, CYBER OPERATIONS AND SECURITY RISK MANAGEMENT
The price of launching an attack simultaneously decreases while the cost of defensive cyber constructions and the rewards from fruitful bouts both continue to increase [6]. According to the traditional armed definition, "strategy" is the use of a country's entire force structure through extensive, long-term preparation and growth in order to guarantee safety or conquest. That strategy was successful in old-style wars against old-style colossal foes. The Merriam-Webster meaning of the plan as "an adaptation or complex of adaptations (as of behavior, metabolism, or structure) that serves or appears to serve an important function in achieving evolutionary success" is more pertinent for today's biosphere of unequal fighting and fast evolving intimidating. Receiving to inferior levels of susceptibility is the key to increasing cybersecurity. Even though threat awareness is crucial, all attacks are made more challenging by reducing vulnerabilities [7].
Cybersecurity risk management: Ashley Madison, the US Workplace of Workers Organization, and JP Morgan Chase are just a few examples of companies that have experienced cyber security breaches that have shown the threat is real and present. Admiral Mike Rodgers, director of the Nationwide Security Activity and commander of the United States Fake Knowledge, was enthused to say that "It's not a matter of if you will be penetrated, but when." [9].
As a result, it is crucial for businesses to accurately assess their current state of cyber security and, where essential, take quick corrective action to address flaws. Governments won't be able to achieve cyber security dangers and will nearly surely experience at opening if there is insufficient visibility into the status of their cyber security.
The term "visibility of cyber security status" refers to having the full picture and capacities to respond to the following queries:
1. What are the present slow heights of enterprise-wide cyber security danger due to the numerous threats we face?
2. Can we tolerate these cyber security dangers?
3. If not, what is our ordered, justifiable strategy for reducing these dangers to manageable levels?
4. Who is in charge and by when?
It is essential to be able to amount the state of cyber security because management is impossible without measurement. Data analytics and security event and event management (SIEM) tools can give helpful hints network compromises that have already occurred or could happen in the future, but these are only partial perspectives, not the capacities of our overall risk status. Threat intellect services work similarly in that they can spot data losses and give useful hints about current or upcoming attacks, but once more, these are not evaluations of our level of risk. Individual results from acquiescence organization, vulnerability organization, penetration challenging, and reviews can all be characterized in the same way.
It is likely to reply to proceed and make decisions rapidly when there is surely in our cybersecurity risk capacities, for example:
1. Being able to classify dangers that we are not ready to stand and having a strong and ordered risk-based action strategy for the switch developments required to decrease these dangers to a satisfactory equal.
2. To gain a deeper comprehension of how threat intellect, SIEM productions, and data analytics can be used to enable quicker, more precise responses.
3. To create defenses for investments in cyber security products and facilities based on risk. But because of the extremely high threat level and the rapid rate of alteration in both the danger and switch scenarios, we must be able to regularly update our assessment of our level of cyber security. As part of planning and budgeting, cybersecurity risk management used to be an annual process, but it is now a vital real-time organizer in the fight against cyberattacks [9].
When people, events, skill, or additional elements of the cyber security danger organization scheme are lacking, insufficient, or malfunction in some method, a cyber security breach con-sequence. Therefore, we must comprehend all of the crucial elements and how they interact.
This does not imply that your risk organization system must store information about each end opinion and the current state of each susceptibility on the net, as there are other gears that can do that; however, the danger organization system must be aware that every endpoint on the network has been recognized and that all dangerous vulnerabilities are being spoken as soon as they are discovered.
### a) Cyberattack model (intrusion Kill Chain
A suitable attack model must be used in order to counter a cyberattack. An attack's current state and potential future states can be identified using a boat perfect. A bout perfect is a hypothesis-based perfect that will be used to forecast potential attacker actions. Our attack model is primarily based on the Lockheed-
Martin Interruption Kill Chain (IKC) [10] model. IKC is a seven-stage model that an attacker must inevitably use to plan and execute an interruption. The IKC phases are shown as follows in Figure 3: [11]
1. Information gathering - gathering details about the tar-get, such as the technologies it uses and any potential security holes.
2. Weaponization is the process of creating hateful code to exploit found weaknesses and combined it with un-known deliverable cargos like pdfs, docs, and pets.
3. Distribution: Moving the weaponized cargo to the intended location.
4. Misuse is the usage of security flaws to run hateful code.
5. Connection – In order for the adversary to uphold its perseverance in the beleaguered setting, Remote Access Trojans (RAT) are typically installed. Attackers may need to execute one or more IKCs to get around various self-justifying panels in order to defeat most advanced defense systems.
Cyber resiliency situational consciousness: The success of cyber resiliency is a consequence of prompt and synchronized movements resulting from an efficient execution procedure. Defenders in a hardy scheme must be able to recognize the movements of assailants, decipher their sense, and respond in a way that will minimize the effects of these movements and enable a speedy recovery of any assets that were harmed.
The side with information dominance has the best chance of winning, just like in any conflict. SA is the key to achieving information dominance (and denying it to the enemy). The following are the main points of SA's response to the question of which data:
Control and direction (C2). An adversary needs a channel of communication to manage its malware and carry out their operations. As a result, a C2 server connection is required. Actions. In the final stage of the kill chain, the opponent ac-complishes its goals by carrying out acts like data. Protectors can be sure that the opposition has advanced to this stage after completing earlier ones [11].
## IX. NATIONAL CYBERSECURITY STRATEGY AND ACTION PLAN
Like the phone system was a period ago, the Internet is now unquestionably a necessary communications infrastructure. However, the Internet's development and technological foundations are very distinct from those of telecommunications or any other infrastructure.
As a result, distinct strategies are needed to guarantee dependable and secure facilities in cyberspace as opposed to on the outdated telecom nets, and distinct processes also need to be followed when developing public policy. Instead of adopting strategies that only encourage higher spending or visibility, Gartner advises that nationwide cybersecurity rule takes a more pragmatic method of encouraging advanced heights of security in the Internet. The administration has a role to play, but attempting to increase cyberspace security through rule will be more like attempting to address global heating than it will be like to address policies pertaining to the banking, banking industry, or the automobile industry [7].
A nationwide cybersecurity plan should, in accordance with[7], make use of the government's resources to advance the normal security procedures used by businesses, administration entities, and individuals in their everyday use of the internet. Define the present areas of weakness, use influence close those gaps, evaluate development, and recurrence are the objectives of such a strategy. The government shouldn't try to switch the level of safety on the Net or pass laws requiring fixes as part of a nationwide cybersecurity strategy. The spread of cybersecurity is a problem that will only worsen as technology advances.
Similar to a storm readiness plan, which orders reshaping constructions or erecting advanced levees instead of the placement of more aquatic devices, the cybersecurity strategy should therefore place a greater emphasis on removing or protecting susceptibilities that enable bouts than on journalism attacks.
### a) Case Study
The Nationwide Cyber Security Plan [12] is an article that the Republic of Croatia means to use to begin preparing the most crucial actions for safeguarding all users of contemporary electric services, including those in the community and commercial sectors as well as the over-all public.
### b) Principles
Internet, substructure, and users under Croatian authority are all covered by the complete nature of the method to cyber security (citizenship, registration, domain, address); combining efforts from various cyber security fields, as well as their connection and supplementation, to make the internet a safer place; proactive approach involving ongoing activity and measure adjustment and appropriate periodic strategic framework adaptation;
Strengthening resiliency, dependability, and adaptability through the application of universal standards for the defense of privacy and the privacy, honesty, and obtainability of sure groups of info, as well as through compliance with the relevant obligations related to these issues, including the application of suitable guarantee and authorization of various kin Application of fundamental principles as the cornerstone of contemporary society's organization in cyberspace, the virtual facet of so-ciety: application of the law to safeguard people's rights and freedoms, particularly privacy, property rights, and all other fundamental aspects of a modern, organized society;
creating a unified legal framework through coordinated efforts from all societal sectors, that is, the forms and lawful objects involved in this Plan; request of the subsidiarity code finished a methodically developed transmission of decision-making and reporting authority on cyber security matters to the suitable expert whose expertise is neighboring to the issue being determined in parts significant for cyber security, from group finished organization and collaboration to the practical subjects of replying to processor intimidatings to specific message and info substructure;
By applying the proportionality principle, each area's costs and level of protection will rise in direct proportion to the risks it faces and its capacity to mitigate those risks.
### c) Cybersecurity Areas
At the time the Strategy was being written, Croatia's top needs were evaluated, and these needs led to the definition of the cyber security areas. These areas cover security measures for the message and info substructure and facilities, including community electric communications, e-Government, and elec-tric monetary facilities, which are the substructure of major strategic importance for the whole society. Another crucial part of cyber security is the defense of vital information and communication infrastructure. It might exist in all three of the aforementioned infrastructure areas, but those characteristics are very different, so it's important to establish the standards for identifying them.
Although cybercrime has existed in civilization for a very long time and takes many dissimilar forms, at the current stage of the growth of the virtual measurement of society, it represents a continuous and a rising threat to the growth and financial wealth of every contemporary state. Because of this, combating cybercrime is also regarded as a priority in the arena of cyber security, and setting strategic objectives is essential to stepping up efforts to do so in the near future.
The component of the defense plan that falls under the purview of the office responsible for defense-related matters is the part of cyber defense. It will be the focus of separate discussion and action, carried out with the aid of all pertinent factors resulting from this Plan, and additional cyber-related nationwide security subjects are handled by a minor amount of the security and intellect system's competent bodies and need a distinct strategy, which will also make use of all the necessary components resulting from this Plan.
In instruction to classify the unique objectives intended to achieve developments in each separate area and the events required for attaining the of the Plan, cyber security parts are analyzed in relative to the over-all gamuts of the Plan. The specific goals and actions that will be additional developed by the Act Plan for the Plan's application are chosen in consideration of the identified societal sectors and how the cyber security field affects each one, as well as the ways in which the various cyber security stakeholders cooperate with one another. The development of the cyber security areas adheres to the principles outlined in the Strategy.
It makes sense to assume that the susceptibility of geospatial information will eventually make it a target for actual bodily attacks on the data's objects.
## X. IMPLEMENTATION OF THE TACTIC
The defined, planned goals are elaborated on the active plan for the application of the plan, lengthways with the relevant establishments and a schedule of limits for their application. It also identifies the application measures required to attain those formats. The action plan for the strategy's application enables systematic oversight of the plan's implementation and acts as a mechanism for controlling whether a particular measure has been fully applied and has achieved the wanted consequence or whether it needs to be redefined in light of the new supplies.
It is essential to found a scheme of incessant nursing of the application of the Plan and Act plan in instruction to ascertain in due period, whether the Plan is producing the wanted con-sequences, that is, whether the clear goals are being achieved and the recognized events are applied within the deliberate time frame, and to also establish a device for coordinating all the capable administration forms in developing the suitable rules and replies to threats.
The Nationwide Cyber Security Council1 (hereafter "the National Council") will be established by the Administration of the Republic of Croatia with the aim of studying and refining the application of the Strategy and Act Plan for its application.
## XI. CONCLUSION ON CONSEQUENCES
The majority of the organizations fulfilled their obligations and gave the Council the necessary information for analysis as part of the separate Action Plan events for which the Assembly demanded the completion of the procedure.
There have been some developments since the Act Plan's application got underway in 2016 among the 30 joint in-stituptions that make up the diverse stakeholder profiles in cybernetic security. Every institution and stakeholder have acknowledged and connected initiatives within their purview to the conceptual thematic measures of the Act Plan. A few managers in the measures' application have completed their tasks. For admission the application of events in the area of critical message and info organizations, it is essential for whole the application of activities and, if essential, to change the legal outline in the area of nationwide dangerous substructure before continuing with the application of national events in this area.
Cybersecurity needs to be much more consistent, and lec-turers at all educational levels and types need better training. Because of this, the effectiveness of the cybernetic security teaching programmed being run in the Republic of Croatia is in doubt.
All nationwide teaching programmed in this area must be developed with the Strategy and Action Plan's emphasis on developing cybersecurity as their framework, and the Council should participate in the Republic of Croatia's optional process for the pertinent office and other forms regarding curriculum improvement and the enhancement of all types and heights of teaching in the area of cybernetic safety and protection.
## XII. CONCLUSION AND FUTURE EFFORT
The administration must play a significant part in encouraging advancement of cybersecurity. The high-leverage part of enhancing cybersecurity is reducing vulnerabilities. A strategy that focuses on operations is required. Many government organizations serve as excellent examples of how to enforce current laws. The relationships and connections between numerous actors at various levels of hierarchy are a contributing factor to the limitations of the national cybersecurity strategy. Information and communication technologies have seen the most dynamic and all-encompassing technological development of any field. The fast growth and introduction of new facilities and crops have always been prioritized, while security-related anxieties have characteristically had little influence on the extensive adoption of new skills.
Modern information systems have very short life cycles from the time of their planning, introduction, and use for the time they are removed from use, which frequently makes systematic testing them impossible. Instead, testing is most frequently practical as an exclusion, in specifically specified bags. The majority of commercial products have security fea-tures that protect user data confidentiality and confidentiality, but because users typically have little information on the skill they use and it is practiced in such a method that it is very difficult to approximation these security features, many of these products are sold commercially. The users' boldness towards message and information skill as a result is largely based on unreasoning sureness.
Technology in the areas of communication and information is pervasive in contemporary societies. Nowadays, text, image, and sound are transmitted between people using a variety of technologies, with the growing Internet of Things (IoT) tendency. While a sure type of message and information organization's deviation from normal operation may go ignored, the indecorous operation of additional systems may have severe repercussions on the state's ability to function. These consequences can include loss of life, health problems, significant material damage, environmental pollution, and disruption of other functions that are crucial to the society's ability to function as a whole.
A variety of factors, including human mistake, malicious action, technological error, and organizational oversight, have contributed to deviations in the proper operation of message and info skills from the time of their inception up until the present.
The development of the Internet and the linking of numerous information and communication systems used by the community, moot, and commercial subdivisions as well as individuals shaped the modern Internet, which is made up of this inter-connected infrastructure as well as users communicating more and more with one another using an increasing number of dissimilar facilities, some brand-new and some more old-style but in a new, computer-generated way.
Nonconformities in how these unified systems or their components should function are no lengthier just practical issues; they pose a threat to worldwide security. The term "cyber security" refers to a variety of actions and policies that modern societies use to combat them. In light of the susceptibility of geospatial information, it may ultimately be rational to anticipate bouts that have a bodily impact on the data's.
Generating HTML Viewer...
References
10 Cites in Article
A Walls,E Perkins,J Weiss (2013). Definition: "Cybersecur¬ity.
(2011). Strategy for operating in cy-berspace.
T Scholtz (2013). Definition: "People-Centric Security.
J Pescatore (2009). Toward a national cybersecurity strategy.
M Herring,K Willett (2014). Cyber Deterrence and Russia’s Active Cyber Defense.
S Marvell (2015). Real-Time Cyber Security Risk Management.
E Hutchins,M Cloppert,R Amin (2011). Intelligencedriven computer network defense informed by analysis of adversary campaigns and in-trusion kill chains.
E Yano,P Gustavsson (2011). Cyber awareness.
(2015). Cyber-Security: National Strategy.
Myriam Dunn Cavelty (2013). A Resilient Europe for an Open, Safe and Secure Cyberspace.
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.