Though Improvised Explosive Devices (IEDs) are commonly attributed to attacks carried out by terrorists in the Middle East, IEDs were also used in the Ukrainian conflict and extremely limited research touches upon the issue. There is a hypothesis that IED events were not mainly focused on killing but rather on striking terror and sowing chaos among the local populace to persuade it to withdraw its support for the Ukrainian government. This article presents an analysis of IEDs as a unique weapon, the possible intensions behind their occurrence in Ukraine at a particular point in time, and the methods of identifying IED use in Ukraine based on the Global Terrorism Database (GTD) and the authors’ database (TAD). Both the imprecision and uncertainty relative to GTD’s classification were discussed, as it served only as the starting point for data evaluation, yielding informative results, although containing little information related to the IEDs directly.
## I. INTRODUCTION
Contemporary armed conflicts are characterized by the coexistence and permeation of both the military- and non-military threats, often irregular in nature (Denysiuk, 2020). The essence of the activities is to avoid the opponent's strengths and attack their weakest, most vulnerable points, using unconventional means and methods. Significant features of these activities include coaxing the opponent into "unknown" areas, using their strength against them and their vulnerabilities to our advantage, using non-traditional weapons and technologies, e.g. improvised explosive devices (IED), deploying innovative tactics, making use of dissimilarity and disproportionality (relative to weapons available). This results in fatalities, usually among the civilian population, injuries, and adverse impact on the infrastructure and the natural environment (Global Terrorism Database, 2021; Landucci at all, 2015; Burkacki at all, 2017; Kowalkowski at all, 2014; Slawinski at all, 2013). Examples of serious threats to military security include improvised explosive devices (IEDs), used during (and after) operations in Iraq and Afghanistan, which hitherto remain a considerable hazard. Attacks by rebels and heavy loss of life, as well as a great loss of equipment, have contributed to in-depth analyses examining the causes behind the assaults, their circumstances, and conditions accompanying such actions, their precise location, and time.
It needs to be unequivocally stated that present-day armed conflicts are characterized by the coexistence and blending of the military and non-military threats, often considered as having a terrorist nature. Attacks with the use of improvised explosive devices (IEDs) provide their users with means of warfare prohibited by law, creating casualties and damaging material assets. Regrettably, the illegal use of improvised explosive devices has been spreading for many years in an uncontrollable manner. IED attacks have taken place in many areas around the globe, causing loss of human life and material consequences. This is indicated by IED attacks in Western countries (e.g. the United States, Great Britain, Northern Ireland, Spain), which are of interest to terrorists (Grant, 2017). Problems of the civilian losses incurred as a result of the use of IEDs during, and in the aftermath of armed conflicts, have been the subject of a number of research projects and publications (Denysiuk, 2020; Betts, 2017; Crane-Seeber, 2011). The prominence of this issue relative to citizen safety, and the constant analysis of threats posed by IEDs, their constant occurrence – even after the analysed period – can be reflected by the fact that in November 2020 at least one death or injury from explosive violence was recorded in 17 countries and territories. One such country is Ukraine (Action on Armed Violence, 2021). The authors themselves strived to identify the approximate number of IED events used in that conflict and to analyse them.[^910]
## II. GEOPOLITICAL BACKGROUND OF THE MILITARY CONFLICT IN UKRAINE
After 1989, momentum was created towards independence and the emergence of sovereign states in the former countries of the Soviet Union. One such country is Ukraine. The independence process was accompanied by the expectations on the part of many nations and social groups in this region of Europe, related to the desire to regain influence in certain geographical areas. The 2014 annexation of Crimea by Russia can serve as an example here. In this case, despite the highly probable Russian interference, no declaration of war was issued on either side (Zapalowski, 2016).
In turn, the armed conflict in the Luhansk- and Donetsk Oblasts (Ukr. province), which had been ongoing since 2014, caused a permanent division of Ukraine. Established on February $12^{\text{th}}$, 2015, the so-called second (Minsk Agreement, 2015) (also known as the Minsk II peace agreement) became only a form of sanctioning temporary separation of the parties to the conflict. This conflict, along with Ukraine's strenuous efforts to regain Crimea, is the key factor contributing to the destabilization process in Ukraine, where the parties to the conflict are the Ukrainian state on one side, and some of its rebellious citizens of Russian nationality living in the Luhansk and Donetsk Oblasts (Zapalowski, 2016).
Despite being a European country, Ukraine faces many malicious acts, such as the quite common use of IEDs against military personnel and persons uninvolved in an undeclared war. There has been an increasing number of attacks with improvised explosive devices in public spaces in recent years. Apart from the overt (as in Crimea) or covert military presence of another state in Ukraine (in Luhansk and Donetsk Oblasts), the parties to the armed conflict, as well as other forces destabilizing Ukraine, have been using combat measures known to terrorists and criminal groups, including improvised explosive devices for several years now. If the factors disintegrating Ukrainian statehood intensify, these weapons (IEDs) will still be quite easy to obtain, construct and use in Ukraine, both against ordinary citizens, public administration officers, as well as military personnel, militia, secret services, etc.
IED attacks on Ukrainian citizens and other feuding nationalities can be carried out both in Ukraine beyond. The use of IED in Ukraine affects the stability of Ukraine itself, but also of its neighbours and even those further away from the country's borders. The threat of IED being used also has a huge impact on the safety of persons living in Ukraine and those visiting the country as tourists, businessmen, or politicians. This country may also serve as a warning to other countries, which currently enjoy a period of peace, both in terms of their social, and military situations. Thus, for other societies, Ukraine can be seen as an example of the need to be prepared for similar occurrences.
## III. THEORETICAL BACKGROUND OF IEDs
Military operations, especially the undeclared ones, as well as the terrorist threats endangering human life and civilian and military infrastructure are a matter of concern for the authorities. The events of September 11, 2001, and military operations in Iraq, Afghanistan, Ukraine, and many other parts of our globe revealed an increase in the impact of armed conflicts on those who are not involved in combat directly – the innocents. Most often, IED events point to terrorist intent behind their use against human beings. The specifics of IED attacks have been the subject of a considerable number of studies. They rely heavily on expert opinions or an approach to an IED case in the form of an assessment using traditional reliability engineering systems and techniques e.g. (Salmon at all, 2019; Cuesta at all, 2019; Gill at all, 2011; Grant&Stewart, 2017; US Department of Homeland Security, 2021). Efforts expended on the investigation of IED attacks are increasingly supported by a core set of state-of-the-art case analysis methods based on systems thinking (Hulme at all, 2018).
What is an IED? There exists no single, authoritative definition of IED, one which would be accepted worldwide. For example, in NATO IED is defined as a 'device placed or fabricated in an improvised manner incorporating destructive, lethal, noxious, pyrotechnic, or incendiary chemicals and designed to destroy, incapacitate, harass or distract. Note: It may incorporate military stores, but is normally devised from non-military components' (NATO Standardization Office, 2020; US Defence Intelligence Agency. 2008). Different NATO definition is included in another publication, (NATO AJP 3.15C, 2018) whilst a more detailed, academic definition of IED can be found in (US Department of Homeland Security, n.d.; Gill at all, 2011).
The analysis of attacks with the use of IEDs shows that, except for military targets, they are used to conduct attacks on the local populace, national authorities at any administrative level and security forces, international organisations, non-governmental organisations and agencies, structures and infrastructure, commercial institutions, and economic nodes. IEDs are tactical weapons, the impact of which, however, is far wider.
The IED serves a specific purpose as means of warfare for the terrorists. IED attacks are a common terrorist weapon of choice against soft targets. Each year, IED attacks kill and injure more people than attacks with any other weapon, except for firearms (Action on Armed Violence Nigeria, n.d., 2020, 2016; Martin, 2016; Connolly&Clutter, 2010; Valsamos at all, 2019; Burkacki at all, 2017; United Nation, 2012, 2015, 2016; Canadian Department of National Defence, 2020; Annual Report, 2011). This may be due to the fact that IEDs are cheap and relatively simple to design and manufacture, in particular, due to the Internet helping in their design (Grant&Stewart, 2017). Data regarding terrorist attacks are published on the Internet by various organizations e.g. (Action on Armed Violence, n.d.; (Global Terrorism Database, n.d.). Apart from its compilations in databases, data regarding losses incurred as a result of IEDs use is also published in or related to other publications (LaFree&Legault, 2009;
LaFree&Dugan, 2007; LaFree at all, 2017; Miller, 2012). It should be emphasized, however, that the authors of these publications usually base their research on the information contained in the listed, openly available databases.
The Global Terrorism Database which covers over 200 000 terrorist attacks dating back to the 1970s, was used to illustrate the types of terrorist attacks (Global Terrorism Database, n.d.). A meaningful increase in terrorist attacks was recorded both directly prior to and in the immediate aftermath of the annexation of Crimea in the Luhansk and Donetsk regions. IED events were not explicitly mentioned in the types of terrorist attacks group. They probably belong in the Bombing/Explosion group, but a noteworthy number of such incidents may be included in the Unknown one.
Figure 1 shows the types of weapons used in terrorist attacks – according to the Global Terrorism Database (Global Terrorism Database, n.d.). In the same database, IED events indicated in this group are included as Explosives/Bombs/Dynamite and comprise almost $50\%$ of terrorist attacks. A considerable number of such events may have been categorised as belonging to the Unknown group.
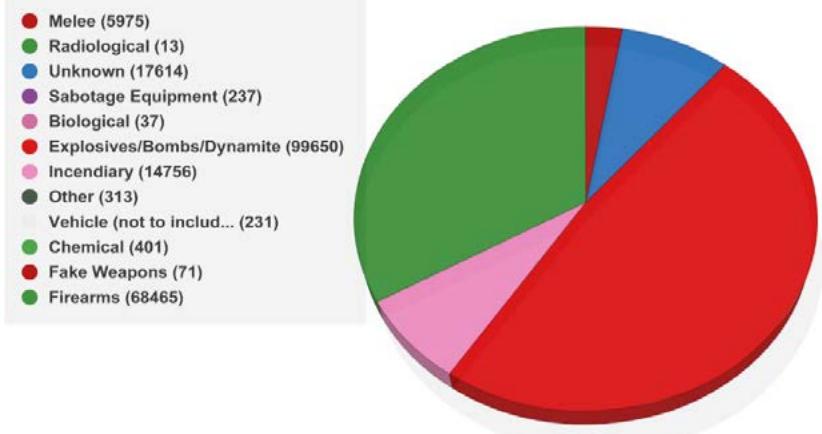 Figure 1: Weapon types of terrorist attacks – according to the Global Terrorism Database (Global Terrorism Database, n.d.).
According to the Action on Armed Violence (AOAV), between October 2010 and the end of September 2020, there have been 28,729 incidents of explosive violence, resulting in 357,619 casualties (263,487 civilians) recorded in English language media worldwide. Of these, 171,732 people were recorded as being from IEDs – a number that includes both civilians and armed actors. $48\%$ of all people killed or injured by explosive weapons globally, then, were harmed by IEDs (Action on Armed Violence, n.d.).
Information on IED events published on the Internet (open network) does not always present all the data of interest to researchers in this narrow field. Some data is difficult to establish or is not known. Some databases are classified. There are also difficulties in identifying specific attacks as those which utilised IEDs.
The IED is a cheap weapon, easy to construct and use, even by a soldier with little training or a rebel fighter. Its construction includes components of various origins, and the amount of explosives is designed to injure or kill persons, damage vehicles, or destroy infrastructure. The tactic of using an IED is also planned. As far as the construction itself is concerned, IEDs generally consist of an initiator, switch, main charge, power source, and a container (Grant&Stewart, 2017).
Any object with explosive properties may be used as IED components, furthermore, the variety of IED design solutions is vast, almost endless. This requires great flexibility, continuous improvement of elements and actions implemented as part of counteracting the use of IEDs (C-IED), and a high level of personnel training, including in the field of IED detection and neutralization (NATO AJP 3.15C, 2018; NATO AJP 3.18, 2018). Descriptions of events with the use of Improvised Explosive Device (IED) in databases are imprecise, making it challenging to create a true picture of threats endangering people's lives and inflicting damage to critical infrastructure. They require seeking out particular events and additional studies of events not listed in the published databases (e.g. in the media).
## IV. MATERIALS AND METHODS
The study investigates the use of IEDs in the Ukrainian conflict. To identify, comprehend and analyse IED usage, defining the concept of IED was necessary (NATO APP-06, 2020; US Intelligence Agency, 2008, 2011). In this paper two databases were used: the GTD dataset, produced by the University of Maryland's START Program, and the proprietary database, called the authors' database (TAD), created by the authors of the article.
Organizing the TAD consisted of collecting information on terrorist attacks in Ukraine from various sources, typically articles in the media and newswires – the Internet, television, news agencies, military sources, and others. However, the events selected to be included in the dataset had to have been depicted as such, in which IED was used. In contrast, other incidents involving conventional weapon usage were rejected. The data gathered was sourced in four languages: Ukrainian, Polish, Russian, and English. This information was translated into English when needed. A two-stage data analysis was performed. The first stage included entering the received (acquired) information into the database. Events were assessed using a standardized scheme across all the years (date), a province where an incident (event) took place, an exact spot of an IED event, a description of an incident, and circumstances
Definitions of the main variables used in the analysis are described in Table 1.
of a given incident. Each time and for each event the data was saved. During the second stage, based primarily on the description of an event (mainly: who, in what way, and how – issues in question), the data was scrutinised, and the obtained results were presented as six separated variables, including types of events, IED incident (event) types, IED employment method – a delivery system, a method of IED emplacement.
After the coding scheme was finalized, the data collected, and its validity assessed, a variety of data analyses processes were conducted. These analyses were intended to provide an empirical baseline for IED terrorist attacks, as collected from the Ukrainian conflict. To create clear, replicable measurements of IED events, each variable in our analysis was based on information available in an incident-level database (LaFree&Legault, 2009).
Table 1: Definitions of variables and their indicators
<table><tr><td>Variable Name (groups)</td><td>Definition</td><td>Indicators (examples)</td></tr><tr><td>IED</td><td>A device placed or fabricated in an improvised manner incorporating destructive, lethal, noxious, pyrotechnic, or incendiary chemicals and designed to destroy, incapacitate, harass, or distract. Note: It may incorporate military stores, but is normally devised from non-military components.</td><td>Home-made bomb, home-made explosives device, explosive-laden vehicle, explosive device dropped by a drone, explosive device</td></tr><tr><td>Ammunition</td><td>Munitions, ordnance, or demolition charges containing explosives, propellants, pyrotechnics, initiating composition, or nuclear-, biological-, or chemical materials for use in military operations</td><td>Bombs, grenades, mines, projectiles, etc.</td></tr><tr><td>Unknown</td><td>Those devices for which there is no information or the information is not clear</td><td>The explosion took place in an apartment</td></tr></table>
Taking the GTD into account, two-stage data analysis was also performed, however, the first stage was different from that in the case of the TAD approach. The GTD database contains 1745 events which appeared to constitute terrorist attacks, and in which 13 different means of combat were used. These were marked as: biological, chemical, explosives/bombs/dynamite, fake weapons, firearms, incendiary, melee, nuclear, other, radiological, sabotage equipment, unknown, vehicle (excluding vehicle-borne explosives, i.e., car or truck bombs). To pinpoint terrorist events with the use of IED in the GTD, an advanced search was performed, in which the following variables were selected: Country – Ukraine, Weapon type – Explosives/Bombs/Dynamite and time: from January $1^{st}$, 2012 to December $31^{st}$, 2018. Moreover, the expanded results tab was used, where the users could find information related to the type of weapon used. Out of 1703 terrorist attacks in Ukraine, 1155 events involving explosives were identified as various types of bombs of the following types:
- Explosives/Bombs/Dynamite
- Explosives/Bombs/Dynamite, subtype: Explosives/Bombs/Dynamite
- Explosives/Bombs/Dynamite, subtype: Explosives/Bombs/Dynamite, Firearms
- Explosives/Bombs/Dynamite, subtype: Firearms
- Explosives/Bombs/Dynamite, subtype: Firearms, Firearms
- Explosives/Bombs/Dynamite, subtype: Incendiary
- Explosives/Bombs/Dynamite, subtype: Other
- Explosives/Bombs/Dynamite, subtype: Unknown
Weapon type identified as "Explosives/Bombs/Dynamite" was selected, since GTD codebook defines it as "a weapon composed of energetically unstable material undergoing rapid decomposition and releasing a pressure wave that causes physical damage to the surrounding environment" Global Terrorism Database Codebook, 2019). Accordingly, this definition does not indicate an IED unambiguously. Nonetheless, it does not eliminate it either.
The second stage of the analysis was like that of the TAD because it was not possible to identify those terrorist attacks in which IEDs were used solely basing on the data presented in GTD. Therefore, each event listed in GTD was analysed (1155) in terms of its description (GTD-HOW tab) and the information on the weapons, the type, and the subtype used. As a result of this examination, the events were classified into the following groups:
- attack with IED;
- it is not clear, whether IED was used in an attack; and
- attack (events) involving ammunition usage.
The English dictionary and professional Explosive Ordnance Disposal and Weapons Intelligence Team experience of one of the authors and were drawn on to define attacks with the use of an IED (an event). While the Oxford Learners' Dictionary defines the notion of a "device "as a bomb or weapon that will explode" (Oxford Learner's Dictionary, n.d.), Longman Dictionary identifies a "device" as a bomb or other explosive weapon (with examples, such as explosive/nuclear/ incendiary, etc. device) (Longman Dictionary, n.d.).
Taking into consideration TAD and GTD and in the context of the presented differences of the variables in Table 1, the photographs from the incident site and their description were the basis for the EDO technicians (researchers) to qualify the type of the incident which took place. The main criteria used to distinguish between IED-related incidents and conventional weapon incidents were the following:
Description on the course of the incident which focused on its nature e.g. direct- or indirect fire (using artillery shells, rockets etc.), a grenade being thrown, shooting with any weapon. In such cases IED incidents were classified as a non-IED events;
The entity fabricating the given hazardous object and its fabrication method: either an arms factory (non-IED) – professional manufacturing, or home-made manufacturing (IED) -,
Two forms of IED presence at the site: either it was found prior to the explosion on following the incident. In former case, the researcher was looking for any mine elements which would be atypical to this weapon. In the later, the most crucial was to locate, either on the photographs or in the description, specific facts or elements which do not belonged to a mine (e.g. radio with wires, electric blasting caps), but are capable of changing the way mine detonated. In those instances, where the IED incident description lacked details which would allow the researcher to qualify the incident either as IED or non-IED type, such events were qualified as non-IED ones or, or if the information was incomplete – as unknown.
To identify IED events, the above understanding of the definition and additional information describing the circumstances of attacks in GTD were taken into consideration. For example, (GTD): "Explosive devices made from 82-mm mortar rounds were used in the attack". In fact, the mortar round was not used, as it was designed. This round was modified in some unknown manner, to make it explode; other devices (e.g. an electric blasting cap, a cell phone, a battery) must be installed to create a new chain of detonation, different from the one designed in an arms factory it. Consequently, the IED was manufactured based on conventional ammunition, but it was no longer a mortar round. Considering these facts, this event was qualified as an IED incident per se.
## V. RESULTS
The convergence of place and time.
In the paper, the authors' attention was focused on the incidents (events) in which Improvised Explosive Devices (IEDs) were used in Ukraine between 2009 and 2019. The authors' deliberations include in-depth case studies of events contained in two databases – the authors' database (TAD) and the Global Terrorism Database (GTD).
The findings discuss the nature of the data collected in these two databases about the number of IED events and where they took place. Across the databases, there was significant variation in the number of terrorist incidents, both as far as attacks utilizing IED are concerned, and relative to other types of weapons being used. During the creation of the TAD, since the research was focused mainly on terrorist incidents in which IED was used, there were not any incidents described in which a type of weapon, i.e., ammunition was utilised. The TAD, however, includes several dozens of incidents related to IED; there are some of them, in case of which the available data was inaccurate and the only available information was that the incident was associated with a terrorist being imprisoned, arrested, or convicted in IED investigations. These incidents are known as "unknown events (incidents)". As far as GTD is concerned, there are no incidents in which IED is identified as a type of weapon. Nevertheless, in the "weapon details" tab there are sometimes pieces of information pointing to IED use in either direct- or indirect way.
Applying the aforementioned definition of IED, Table 2 was drawn, in which the number of the IED terrorist attacks (incidents) is presented for the two databases. These netted 294 IED attacks out of a total of 328 events in the TAD and GTD, with zero IED attacks out of a total of 1155 events included in the later database. For purposes of this study, 294 and 59 IED incidents were researched in the two databases, respectively.
Table 2: Databases description
<table><tr><td></td><td>TAD</td><td>GTD</td></tr><tr><td># of Events (attacks with IED)</td><td>294</td><td>0</td></tr><tr><td># of Events (unknown)</td><td>34</td><td>0</td></tr><tr><td># of Events (explosives/Bombs/Dynamite)</td><td>0</td><td>942</td></tr><tr><td># of Events (explosives/Bombs/Dynamite, subtype: Explosives/Bombs/Dynamite)</td><td>0</td><td>4</td></tr><tr><td># of Events (explosives/Bombs/Dynamite, subtype: Explosives/Bombs/Dynamite, Firearms)</td><td>0</td><td>4</td></tr><tr><td># of Events Explosives/Bombs/Dynamite, subtype: Firearms</td><td>0</td><td>178</td></tr><tr><td># of Events Explosives/Bombs/Dynamite, subtype: Firearms, Firearms</td><td>0</td><td>22</td></tr><tr><td># of Events Explosives/Bombs/Dynamite, subtype: Incendiary</td><td>0</td><td>2</td></tr><tr><td># of Events Explosives/Bombs/Dynamite, subtype: Other</td><td>0</td><td>1</td></tr><tr><td># of Events Explosives/Bombs/Dynamite, subtype: Unknown</td><td>0</td><td>2</td></tr><tr><td>Total</td><td>328</td><td>1155</td></tr></table>
Once a common definition of IED was applied across the GTD at an event level, case-by-case analysis and identification of those incidents, during which IEDs were used in the attacks, was conducted. Using descriptions and case attributes in the GTD tabs to identify IED or its components across the 1155 GTD incidents, IED incidents were identified. The research shows 59 IED events; 172 events which were classified as being of an "unknown" character, and 924 events that included the use of conventional weapons - ammunition, resulting in an all-encompassing number of 1155 events.
In the process of triangulation, new information was introduced on numerous events – its convergence. When these two databases were compared regarding the dates and descriptions of events they contain, it was found that 33 IED incidents across the GTD database matched events in the TAD. However, there were several cases in which the date of an event is one day back or ahead.
The investigation relating to the number of IEDs used in attacks per annum during the period of 2009-2019 in the TAD, as well as between 2009 and 2018 in the GTD. In the years 2009-2012, no more than 6 events per year were identified. According to the TAD, there were no events involving the use of IEDs in 2013. As far as the IED events in the TAD are concerned, the largest number of IED incidents was recorded between 2014 and 2017. The culmination of incidents occurred in 2015 - when 93 events were noted. In 2016, the number of IED incidents dropped to 44. In turn, this level increased to 57 in 2017, and, subsequently, dropped to below 30 events per year and remained at that level in the following two years.
Taking GTD into consideration, IED events through one decade, the majority of IED events was recorded between 2014 and 2017, when they comprised $90\%$ of all the incidents, with a similar peak to the one noted in the TAD in 2015, namely 24 events.
In both the databases there are IED events, however, in several dozens of incidents, the identification of IED presence was impossible due to the lack of sufficient evidence (information). Hence the definition of such events as unknown. Firstly, the greatest number of GTD unknown events took place between 2013 and 2016 - 155 events in total, with the high point in 2015, when 81 were noted. Secondly, in the TAD the unknown depicts 34 events in total, with their apex also in 2015 - 7 events.
Considering the administrative division of Ukraine, the analyses revealed the number of IED events by province (location) in both databases. The research results indicate that the prevalent number of IED events took place in the following 6 provinces: Donetsk, Luhansk, Kiev, Odessa (Odesa), Kharkov (Kharkiv), and Dnipropetrovsk. The percentage value of these events is $85.9\%$ of all the events in the GTD database, and $84.4\%$ of all the events in the TAD. The results show similarity, however, it should be noted that each database has a different total number of events: GTD contains 59 events, whereas the TAD includes 294 events. What is more, there are 9 events in the TAD, where the exact location and province had not been identified. They were marked as an unknown location.
Even though the Donetsk and Luhansk provinces experienced the highest rate of IED events, the data indicates that their municipalities were not as heavily targeted as Kiev and Odessa cities were. To sum up the study in the context of location, Figure 2 depicts the number of IED events indicated on the administrative map of Ukraine, as based on the TAD - 285 IED events, keeping in mind the previously mentioned 9 events, the location of which was unknown.
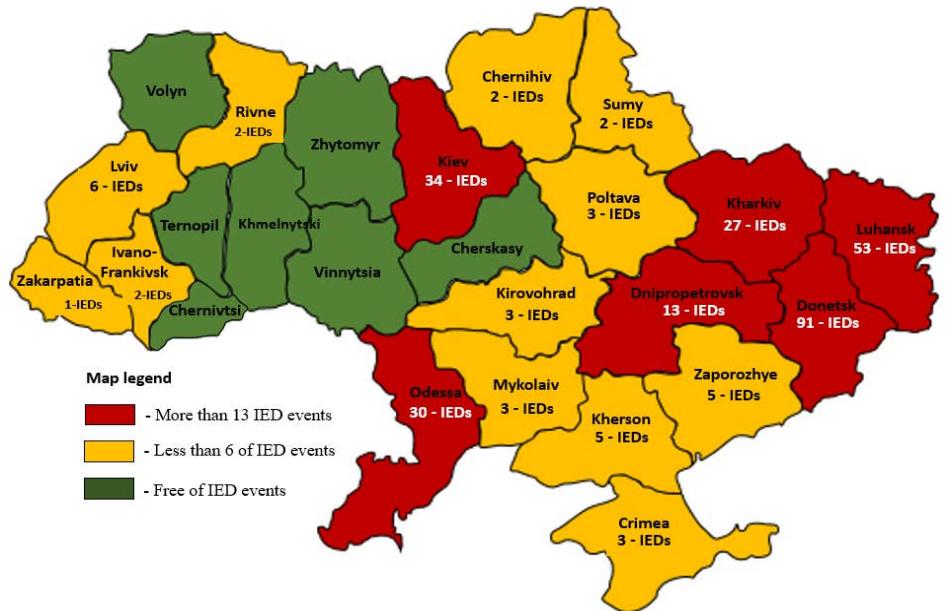 Figure 2: Number of IED events in Ukraine by provinces - TAD.
Taking the TAD into consideration, a detailed analysis was carried out as far as the exact location of IED incidents was concerned. The authors found that most of the events took place in the following cities:
- Kiev province: out of 34 incidents overall, 27 events took place in Kiev city itself,
- Odessa province: out of 30 incidents in this province, 23 events took place in Odessa city itself,
- Donetsk province: 17 out of the 91 events in this province occurred in Donetsk city itself,
- Kharkiv province: 16 out of the 27 events in this province took place in Kharkiv city itself,
- Luhansk province: 9 out of the 53 events in this province transpired in Luhansk city itself,
- Dnipropetrovsk province: out of 13 incidents in this province, 8 events took place in Dnipropetrovsk city itself,
- Lviv province: 4 out of 6 events in this province took place in Lviv city or its suburbs.
Analysis of the dates of individual events (TAD) broken down by months shows that until the mid-2014 (June) IED events occurred sporadically – monthly arithmetic mean of 1 IED event, whereas from July 2014 to January 2015 they were at the level of 1 to 6 IED events – monthly arithmetic means of 3.1 IED events. On the other hand, from February 2015 to February 2016, the average number of monthly IED events was 7.8 events per month, while from March to the end of the year the average value equalled 3.2 events per month. In turn, in the following years, this value was at the level of 4.5 IED events per month in 2017; 2.3 IED events per month in 2018, and in 2019 – 2.1 of those events per month.
## VI. DISCUSSION
What is intention behind the IED attacks? Attempt at understanding the phenomenon.
Wars being waged nowadays seem to be more complex than those made in the past, both in terms of the armed conflicts themselves, and those activities which are not directly their parts, such as the defence of the given country's population and protection of state structures.
This contemporary reorganization focuses on engaging in many types of warfare at the same time. The division into large and conventional versus small and irregular wars (armed conflicts), where the former is led by states, and the latter by non-state entities, does not fit in with present-day reality (Hoffman, 2007). The current conflicts – the reality around them – are defined by terms, such as "hybrid threat", "hybrid conflict" and "hybrid war" (Pawlak, 2015; Stoddard, 2020; Harris, 2020; Oxnevad, 2020; Hoffman, 2007; Murray&Mansoor, 2012) where during operations the following conventional and unconventional actions are taken apropos of tactics, weapons and other factors influencing warfare. The term "hybrid war" was popularized by Western media and military experts after the annexation of Crimea. It was then that the state as a subject of international law could conduct a "hybrid war" which blends conventional warfare with new elements of cyber-electronic warfare, drones, radio jamming, usage of sophisticated armament and equipment (Veljovski at all, 2017), as well as IEDs.
Despite significant datasets ((LaFree at all, 2017; Global Terrorism Database, n.d.; Action on Armed Violence, n.d.) and speculation among terrorism researches regarding the state and non-state organizations and attacks launched by the two using various means of warfare, quantitative and qualitative analysis of events frequently do not identify weapon type used in terrorist attacks precisely. The conducted analyses, however, resulted in a near-complete absence of the study of improvised explosives devices in the Ukrainian conflict, often the analyses included referring to them as booby trap bombs, remote-detonated devices, and so on, excluding some exception in some designated period (NATO Project Github, n.d.). An IED and other synonymous terms seem to be most frequently attributed to terrorist organizations (e.g. ISIS and others) and attacks carried out by such groups or one of the most well-known conflicts in Iraq, Afghanistan, and Syria. However, IEDs were also used in the Ukrainian conflict and extremely limited research touches the issue.
Moreover, the comparison of the number of events with their use relative to the two databases (TAD and GTD) reveals that the number of events utilizing IEDs was the highest in 2015. The question arises, what was the reason for this surge, and the subsequent reduction in the number of such events in following (months) years. If we were to plot the number of monthly IED events on the timeline in terms of events related to the conflict in question, the following observations could be made. The culmination of IED events in 2015 is also related to the launch of an anti-terrorist operation by the Ukrainian side in order to regain control in the state (BBC, 2014), which ended in 2018 (Coffey, 2021). Considering the decrease in the number of IED events in 2018 and 2019, these low values converge with the announced completion of the anti-terrorist operation by the Ukrainian side.
When the military actions in Ukraine are researched from the perspective of the Ukrainian provinces, what can be seen is that the highest number of IED incidents was noted in 6 provinces (plus Crimea) out of the 24. The fact that these provinces include Donetsk and Luhansk - provinces taken over by separatists; Kharkiv and Dnipropetrovsk - neighbouring provinces, as well as Kiev - the province with the capital city, is of no surprise. However, the sixth province with the highest number of IED events was Odessa. Considering the period of 2009 to 2019, Odessa, after Kiev, is the second province in Ukraine to record the highest number of IED events. Moreover, in 2015, Odessa had the highest number of IED events among all the Ukrainian cities.
The non-linear warfare and reflexive control and thus to the non-conventional measures were related to the number of IED events. The facts are as follows: firstly, Odessa is one of nine seaports characterised by highest container handling capacity in the region (Görçün, 2020); secondly, the natives in the province speak mostly Russian and thirdly, Transnistria (with its capital of Tiraspol) is located several dozen kilometres (approx. $100\mathrm{km}$ ) from Odessa and is a separatist region of the state of Moldova. The fourth point is that Transnistria, like Donetsk and Lugansk, is actively supported by the Russian military stationed in Moldova (Peterka-Benton, 2012). Fifthly, former Georgia's president Mikheil Saakashvili was appointed by President Petro Poroshenko to the post of the governor of the southern Ukrainian region of Odessa (BBC, 2015).
Despite lacking full territorial control, the Russian Federation annexed the Donetsk, Luhansk, Kherson, and Zaporizhia oblasts. The Odessa Oblast has not been seized or detached from Ukraine in either 2015 – the year of the greatest number of incidents – or in 2022 and 2023. Security destabilization, caused by terrorist attacks employing aspects of reflective control and non-linear warfare within the Odessa Oblast, has not led to favourable conditions for the Russian Federation to gain control over parts or the entirety of the city (oblast) from 2015 to the present day.
## VII. CONCLUSION
In line with the objectives set out for the study, thanks to the data contained in the GTD and, above all, to the authors own analysis of terrorist incidents in the form of TAD, security aspects of improvised explosive devices in the Ukrainian armed conflict during the period of 2009-2019 could be examined was and a case study was made possible. What results from the findings, is that data presented in the publicly available databases such as GTD, are not particularly detailed. A thorough account of the difficulties encountered when dealing with such databases was presented when comparing these data with the ones from the author's very own research. The former is not correlated with the regions, where armed conflicts occur.
It turns out that such issues can be presented as precisely as possible, and based on such investigations, conclusions can be drawn regarding the impact of the circumstances and conditions behind IED events not only on the security of Ukrainian citizens but also those in countries, whose political and military situation is similar to that of Ukraine.
IED incident type is impacted by a number of factors, but one of the most important is the Counter-Improvised Explosive Devices (C-IED) approach characterized by three complementary pillars: prepare the force, defeat the device, and attack the networks (NATO AJP 3.15C, 2018). This is a defensive view. Responsibility for the identification and disposal of IEDs is borne by the properly prepared services, and depending on the adopted solution, these may include: the police, military forces, national guard, coast guard, etc. Each country adopts its distinctive solution. In the case of Ukraine, the police have the capacity to dispose of IEDs related to typical criminal activities and terrorist incidents. However, the ongoing conflict resulted in C-IED operations, including recognition and removal of IEDs being assigned to Armed Forces of Ukraine (AFU).
Since the 1990s, Ukraine has been working with NATO in a wide range of areas including, peace-support operations, defence and security sector reform, military-to-military cooperation. NATO Trust Fund Project on Explosive Ordnance Disposal and Countering Improvised Explosive Ordnance Devices (EOD & CIED), destruction of conventional ammunition, small arms and light weapons, and antipersonnel landmines, which may serve as examples of such cooperation here (Maksak, 2021). After the armed conflict broke out, several Slovakian-led NATO countries (Slovak MOD, 2018) supported Ukraine in efforts to increase the ability to counter various incidents with the use of IEDs and other weapons. One of the many implemented projects, in this case around training, is AFU's Demining Centre which organised a successful course on Improvised Explosive Device Disposal (IEDD) transition. In other words, in 2018, the Ukrainian training centre achieved the capability to train future EOD (IEDD) technicians, and thus recognize IEDs and render them safe.
Research shows that, paradoxically, most of the IED characteristics (number of IED used in attacks by year, number of IED used in attacks by province) can be established quite precisely on the grounds of one hundred cases of IED use broadcasted in the media.
To the neighbouring countries and even to the international community, Ukrainian IED events can serve as an example and a cautionary tale that similar events may manifest elsewhere in the world, even in those countries which currently enjoy peace. Thus, Ukraine IED incidents forewarn about the need to be prepared for similar events and make a contribution to further analysis, development of a much larger and even more comprehensive factual database on such incidents, reaching and supporting conclusions, and educating societies on how to ensure safety relative to this type of occurrences in the region, in Europe and other areas of the world.
To provide a comprehensive understanding of the repercussions of IEDs on security in Europe and other parts of the world, the authors are conducting further research not only on Ukrainian matters but also focus their efforts on IED events within the Russian Federation and other European countries, including Central and Eastern Europe. The investigation is carried out in terms of differences, similarities, dependencies, and the impact of the IEDs as one of the factors shaping regional- and global security.
### ACKNOWLEDGEMENTS
The authors would like to thank the Minister of Defense of Poland for decision No. 20/Szkol./DNiSW, dated October $27^{\text{th}}$, 2017, on the support program for basic research at military universities under the name of a "Research Grant". As part of the task, projects are implemented, the subject matter of which is related to the current "Priority research directions in the Ministry of National Defense".
Disclosure statement
No potential conflict of interest was reported by the authors.
Generating HTML Viewer...
References
38 Cites in Article
(2021). About the GTD.
Coffey Adam (2021). Ukraine Declares "Anti-Terrorist Operation in the Donbas" Officially Over: What Does That Mean?.
(2011). Protection of Civilians in Armed Conflict -Afghanistan | ReliefWeb' <https.
Aoav (2021). Action on Armed Violence | AOAV.
George Byford (2021). COUNTER Improvised Explosive Device (C-IED) Operations as an Element of Counter Insurgency (COIN): Balancing C-IED Efforts to Support Commander International Security Assistance Force (COMISAF) Operational Objectives.
Linda Grimm (2020). United States and International Officials Comment on Unrest and Violence in Africa : October 21, November 2, November 3, November 10, November 13, and November 17, 2020.
(2021). Improvised Explosive Devices Research.
Richard Betts (2017). Conflict After the Cold War.
Thomas Connolly,J Clutter (2010). Criteria to determine likelihood of brain injury during explosive events.
Irmina Denysiuk (2020). Irregular Warfare and Modern Defense – Counterinsurgency Operations.
Dictionary (2021). The Longman Dictionary of Contemporary English (5th ed.).
(2024). learner, n..
(2021). Full Text of the Minsk Agreement.
Paul Gill,John Horgan,Jeffrey Lovelace (2011). Improvised Explosive Device: The Problem of Definition.
Ömer Görçün,Faruk (2020). Efficiency Analysis of Black Sea Container Seaports: Application of an Integrated MCDM Approach.
Matthew Grant,Mark Stewart (2017). Modelling Improvised Explosive Device Attacks in the West -Assessing the Hazard.
Ho-Jeung Kang (2021). The Potential Misuse of AI Technologies in Terrorism and Counterstrategies: A Focus on the Global Terrorism Database (GTD).
Kira Harris (2020). Russia's Fifth Column: The Influence of the Night Wolves Motorcycle Club.
Bruce Hoffman (2007). The ‘cult of the insurgent’: its tactical and strategic implications.
Adam Hulme,Neville Stanton,Guy Walker,Patrick Waterson,Paul Salmon (2019). What do applications of systems thinking accident analysis methods tell us about accident causation? A systematic review of applications between 1990 and 2018.
Gary Lafree,Laura Dugan (2007). Introducing the Global Terrorism Database.
Gary Lafree,Laura Dugan,Erin Miller (2017). Putting Terrorism in Context.
Gary Lafree,Richard Legault (2009). Developing An Empirical Understanding of Improvised Explosive Devices : A Social and Behavioral Science Perspective.
Hennadiy Maksak (2021). The security perception and security policy of Ukraine, 1991–2018.
Richard Martin (2016). Soft Targets are Easy Terror Targets: Increased Frequency of Attacks, Practical Preparation, and Prevention.
Erin Miller (2012). Patterns of Onset and Decline Among Terrorist Organizations.
Radosław Ambroziak,Sławomir Ambroziak,Ryszard Katulski (2018). COUNTERING IMPROVISED EXPLOSIVE DEVICES IN THE LIGHT OF AJP-3.15 ALLIED JOINT DOCTRINE.
Carl Curling,Julia Burr (2018). NATO Allied Joint Medical Publication 7: Allied Joint Medical Doctrine for Support to Chemical, Biological, Radiological, and Nuclear (CBRN) Defensive Operations, Final Draft.
(2020). Glossary of terms.
(2015). New Odessa Governor Saakashvili "will Tackle Corruption" -BBC News.
Ian Oxnevad (2020). Beyond a Desert Revolt: TE Lawrence's Theory of Proxy War and State Creation.
Daniela Peterka-Benton (2012). Arms Trafficking in Transnistria: A European Security Threat?.
Paul Salmon,Adam Hulme,Guy Walker,Patrick Waterson,Elise Berber,Neville Stanton (2019). The big picture on accident causation: A review, synthesis and meta-analysis of AcciMap studies.
Elena Aldescu,Inês Neves (2021). Non-Economic Activities with Economic Features: the Speciality of ‘Hybrid’ Social Security systems. Case Comment to the Judgment of the EU Court of Justice of 11 June 2020 European Commission and Slovak Republic v Dôvera zdravotná poist’ovňa (Joined cases C-262/18P and C-271/18P).
Tadeusz Sławiński ; Grzegorz,Wiesław Niezgoda,Marcin Barnat,Wojtkowski Numerical Analysis.
No ethics committee approval was required for this article type.
Data Availability
Not applicable for this article.
How to Cite This Article
Grzegorz Piela. 2026. \u201cSecurity Aspects of Improvised Explosive Devices. The Ukrainian Case Study\u201d. Global Journal of Human-Social Science - F: Political Science GJHSS-F Volume 23 (GJHSS Volume 23 Issue F4): .
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
Though Improvised Explosive Devices (IEDs) are commonly attributed to attacks carried out by terrorists in the Middle East, IEDs were also used in the Ukrainian conflict and extremely limited research touches upon the issue. There is a hypothesis that IED events were not mainly focused on killing but rather on striking terror and sowing chaos among the local populace to persuade it to withdraw its support for the Ukrainian government. This article presents an analysis of IEDs as a unique weapon, the possible intensions behind their occurrence in Ukraine at a particular point in time, and the methods of identifying IED use in Ukraine based on the Global Terrorism Database (GTD) and the authors’ database (TAD). Both the imprecision and uncertainty relative to GTD’s classification were discussed, as it served only as the starting point for data evaluation, yielding informative results, although containing little information related to the IEDs directly.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.