The strategy of digital twin (DT) implementation at the cyber-physical enterprises is proposed, which is due to the need for high-quality and effective reconstruction of Ukraine. The TISM and MICMAC methods are used to study the factors that influence the strategy of DT implementation to support the guaranteed functioning of a cyber-physical system. 13 main factors, that determine strategy success, were identified, and a model of strategy realization was built in the form of a six-level interaction diagram (digraph). The factors are classified by influence and dependence. The substantiated conclusion is that the state support of DT implementation strategy, the availability of design standards, data protection methods, legislative regulation and implementation experience by other enterprises are key factors to the success of strategy for DT implementation at the enterprise.
## I. INTRODUCTION
Ukraine's economy and infrastructure are being increasingly damaged since the full-scale russian invasion. The World Bank's estimate of full reconstruction price as of February 24, 2023 was $411 billion. The estimate covered social, production and infrastructure sectors as well as environmental damage [1]. A 10-year Recovery Plan for Ukraine has been developed, which includes 850 projects with a total cost of over$ 750 billion. One of 5 plan's core guiding principles is "Build back better" [2]. One of prerequisites for ensuring implementation sustainability is digital transformation. In order for infrastructure to meet modern standards, during the country reconstruction Industry 4.0 technologies should be involved, one of which is digital twin (DT).
The basic DT concept is a physical object, a virtual object with information exchange between them. DT could be designed as a computer model of physical object, with a set of forecasting algorithms, which include an information-analytical system, as well as corresponding hardware-software system. DT development may be based on simulation modeling methods that provide the most realistic representation of physical environment or virtual world object. Mathematical description of DT could be obtained by statistical and analytical modeling, machine learning [3-4].
Object's virtual nature allows to experiment with model, build scenarios instead of doing real tests, thus bypassing resource loss and risks. A detailed history of development, classification, areas of use and prospects of this technology are given in authors work [5]. DT is used both for new technical systems design and maintenance of existing ones. For instance, General Electric uses DT to optimize aircraft engines performance and predict its components failure time [6]. According to Research and Markets report, the global DT market is estimated at $10.1 billion in 2023, and is expected to grow to$ 110.1 billion by 2028. [7].
DT is applied, in particular, in manufacturing sector, automobile, aerospace and aviation industries, energy sector, and smart cities [6]. The versatility of the strategy allows it to be used at almost any enterprise. Among other things, digital twins of organizations are implemented, the main purpose of which is scenario analysis and support for business strategies [8].
The purpose of this paper is to develop a strategy of DT implementation to support the guaranteed functioning of a cyber-physical system in the form of enterprise during Ukraine reconstruction. The TISM (Total Interpretive Structural Modeling) and MICMAC (Cross-Impact Matrix Multiplication Applied To Classification) methods were applied to investigate the factors that influence DT implementation at the enterprise [9-10]. Based on TISM results, a 6-level digraph of factors interaction was built, which elucidates key factors that the company's top management should pay attention to when implementing DT. The work is relevant, because in post-war Ukraine, infrastructure reconstruction must be done according to modern standards.
## II. LITERATURE ANALYSIS
The idea of creating a digital copy during the design of system and its subsequent support was implemented as early as 1960 by NASA during the Apollo mission. However, DT concept emergence is associated with Michael Greaves' work which was a part of presentation at the University of Michigan for industry representatives in 2002 year. In 2014, he laid out a detailed description in a White Paper, later writing a book «The Origin of Digital Twins». 3 stages of concept development, areas of use, prospects of DT are given in author's work [5]. The emergence of cloud computing, IoT, Big Data, and rapid development of artificial intelligence have given a powerful rise to DT technology, spreading it among developed countries along with other Industry 4.0 innovations [11].
In order to identify factors that influence DT implementation at the enterprise, a comprehensive literature analysis was conducted in Scopus, Researchgate, and IEEE Xplore databases. Scientific articles, conference materials, analytical reports and technological blogs of leading companies were examined. The analysis showed that market economy is not sufficient for innovative activity at enterprises [12].
The main barriers to DT implementation are high financial costs and lack of qualified employees, especially for small and medium-sized businesses [13-14]. A noticeable problem is the lack of DT design standards [15]. Existing ISO, IEEE, ITU, IEC standards are not yet able to satisfy the needs [16]. Cybersecurity is also important. DT accumulates data about a physical object from sensors network, installed on it, generating several gigabytes of information per day. Data must be collected, processed through cloud solutions and protected from unauthorized influence [17]. For example, in 2015, the BlackEnergy malware attack on cyberphysical systems of Ukrainian energy suppliers affected 225,000 consumers [18].
The strategy of DT implementation creates uncertainty in issues of intellectual property and copyright, liability for errors and data privacy [19]. A possible version of state regulatory measures is given in [20]. Also, lack of top management commitment is a serious barrier for Industry 4.0 [21]. For example, according to a survey among Norwegian enterprise managers, $85\%$ of oil and gas companies and $49\%$ of mixed industry, consider uncertainty about consequences and risks as a factor that inhibits Industry 4.0 development [22]. Cooperation with scientific centers and institutes is important when planning digitalization, an example is given in [23].
DT development is a sequential process. First, a Proof of Concept is being designed - DT prototype to confirm adequacy of object model. Next, Subsystem Digital Twins are created, which are combined into a Full Digital Twin [24]. At the development stage, 5G mobile and broadband coverage is critical to a successful project. Otherwise, it would be necessary to use inconvenient cable connections [17]. The launch of 5G pilot version in Ukraine was planned for 2024 [25].
For effective DT application at the enterprise, an important factor is a corporate digital culture that defines common values and ways of doing business, encourages lifelong learning among employees, teamwork and innovation. Studies show there was no "cultural" preparation at companies where digitalization failed [26].
## III. METHODS OF RESEARCH
Within the proposed strategy framework, the TISM and MICMAC methods are used to investigate factors that influence DT implementation at the cyber physical enterprise to support guaranteed functioning of physical model. The TISM is a modification of ISM (Interpretive Structural Modeling) method, the latter was proposed by researcher John Warfield for complex socioeconomic systems analysis [27]. TISM algorithm repeats ISM, but additionally requires interpretation of connections in the system [9]. Now it is used to analyze any system, in particular, various aspects of Industry 4.0 [10], [28-30]. Usually, after TISM, the MICMAC method is used, which classifies system components into 4 types according to two properties: influence on system development and dependence on other system components. MICMAC discovers which factors are root causes and which are consequences of other factors.
a) The TISM method. Algorithm construction of the hierarchical structure of the studied system
The TISM method displays structure of the system under study. As output, it produces a hierarchical diagram of interconnections between system elements, which is then analyzed for decision-making. Algorithm of method is as follows [9]:
Step-1: Define set $X$ - key elements of the system.
Step-2: Define relationship between elements of $X$, which could be interpreted as:
- causal relationship (A leads to B);
- elements priority (A is more important than B);
- mathematical relationship between elements, etc.
Step-3: Compare pairwise all $X$ elements whether there is a relationship between each pair, which is done by experts or research group. Results are put inside Initial reachability matrix (IRM) according to the rule:
- if there is a relationship between $(i, j)$ - into cell $(i, j)$ of IRM 1 is written;
- if there is no relationship between $(i, j)$ - into cell $(i, j)$ of IRM 0 is written;
- cell $(i,i)$ of IRM (diagonal elements of matrix) is always 1.
Total amount of comparisons for set of size $n$ could be calculated by formula (1)
$$
N = n (n-1)
$$
Here is an example of creating an IRM. Assume we have set $\{a_1, a_2, a_3\}$ with the relationship between $(a_3, a_1)$, $(a_1, a_2)$. The corresponding IRM is shown in table 1.
Table 1: Example of Creating an IRM
<table><tr><td></td><td>a1</td><td>a2</td><td>a3</td></tr><tr><td>a1</td><td>1</td><td>1</td><td>0</td></tr><tr><td>a2</td><td>0</td><td>1</td><td>0</td></tr><tr><td>a3</td><td>1</td><td>0</td><td>1</td></tr></table>
Step-4: From now on, it is convenient to apply the mathematical theory of relations, in terms of which the relationship between elements is a binary reflexive relation $R$, which is defined by the Boolean matrix IRM. TISM methodology requires to check $R$ for transitivity, that is, condition (2)
$$
\forall a, b, c \in X: a R b \wedge b R c \Rightarrow a R c \tag {2}
$$
$$
F R M = \sup _ {1 \leq i \leq n} I R M ^ {k}, \tag {3}
$$
where matrix multiplication and supremum are defined by (4) and (5), respectively.
$$
(A \cdot B)_{ij} = \max_{k} \left(\min \left(A_{ik}, B_{kj}\right)\right),
$$
$$
\sup\left(A,B\right)_{ij} = \max\left(A_{ij},B_{ij}\right).
$$
FRM defines new transitive relation $R^{*}$.
Step-5: Perform level partitioning the following way:
- 5.1. Define set of elements $D$ and level $r = 1$.
- 5.2. If $D = \emptyset$ stop. Otherwise, for each $D_i \in D$ find Reachability set $R_i$, Antecedent set $A_i$ and Intersection set $I_i$ according to (5), (6), (7), respectively
$$
R _ {i} = \left\{D _ {j} \in D \mid \left(D _ {i}, D _ {j}\right) \in R \right\}, \tag {6}
$$
$$
A _ {i} = \left\{D _ {j} \in D \mid \left(D _ {j}, D _ {i}\right) \in R \right\}, \tag {7}
$$
$$
I_{i} = R_{i} \cap A_{i}.
$$
$$
I_{i} = R \cap A_{i}.
$$
$R_{i} -$ set of elements $D_{j}\in D$, which could be reached from $D_{i}$ in one step.
$A_{i} -$ set of elements $D_{j}\in D$, which could reach $D_{i}$ in one step.
If we work with causal relationship, then $R_{i}$ – set of events directly caused by $D_{i}$ and $A_{i}$ – set of events, which directly cause $D_{i}$.
5.3. If $R_{i} = I_{i}$ then assign element $D_{i}$ to level $r$. Then assume $D = D \backslash \{D_{i}\}$ and $r = r + 1$. Return to step 5.2.
Step-6: Display divided elements on digraph. The first levels are on top, the following levels are below them. Only direct connections and significant transitive links are displayed. Digraph is interpreted by experts, explanations are written into Interpretive matrix. Lower levels are independent elements that affect all others. Upper levels – elements that depend on the elements of the lower levels.
### b) MICMAC method. Algorithm for evaluation of elements influence on the system
MICMAC is often applied after TISM, since it uses FRM as input to evaluate influence of each element on system. The algorithm includes the following steps:
Step-1: Calculate sum for each row in FRM - Driving power. It is a measure of $D_{i}$ influence on other system components.
Step-2: Calculate sum for each column in FRM - Dependence, which measures how much components affect the element $D_{i}$.
Step-3: For each element display (Dependence, Driving power) in the Cartesian coordinate system.
Step-4: Set thresholds for Dependence and Driving power, above which they are considered "high", below - "low". For set of $n$ elements the value of 2 is taken as the threshold. The plane is divided into 4 quarters (an example is shown in Figure 1).
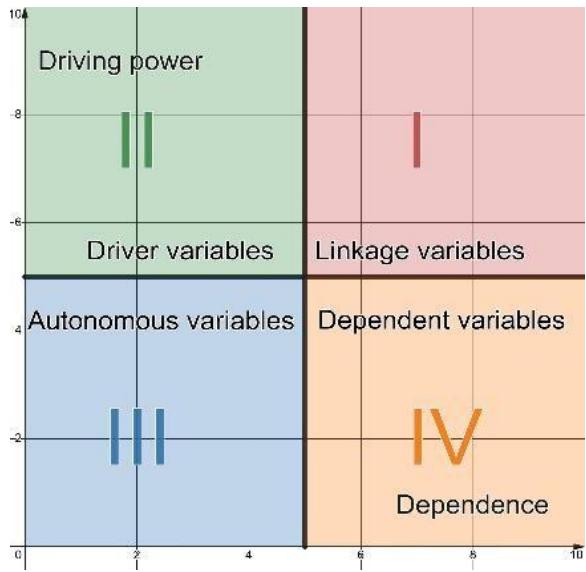 Fig. 1: Example how plane is divided in MICMAC-analysis
Step-5: Classify each element according to which quarter the corresponding point is in. MICMAC divides elements into four types:
- Linkage Variables - high influence and dependence (quarter 1);
- Driver Variables - high influence, low dependence (quarter 2); - Autonomous Variables - low influence and dependence (quarter 3);
- Dependent Variables - low influence, high dependence (quarter 4).
As a result, elements are classified into the most influential, which determine system development (Driver and Linkage) and ones without a significant impact (Autonomous and Dependent). Other variations of MICMAC exist, such as fuzzy version [21]. However, the essence remains unchanged - classification of system elements according to their level of influence and dependence on other components.
## IV. RESULTS
### a) Application of TISM method to build a hierarchical scheme of factors interaction
DT implementation depends on both external and internal conditions. During literature analysis 13 key factors were identified. Their description is given below:
1. State support for the implementation of the DT strategy. The state's role in support of this innovative activity process includes various forms of stimulation: direct financing, technical support programs, loans (including preferential), earmarked grants, DT implementation support funds, legislative protection of intellectual property [14].
2. DT design standards, data protection methods. The Lack of standards for DT creation is a serious barrier to its implementation [15]. In particular, these
standards should take into account cybersecurity issues [18].
3. Regulation of DT implementation at legislative level. For DT to take root in the market, the state needs to create an administrative and legal framework in accordance with European standards [19].
4. Experience of DT implementation by other enterprises. It will be easier for top management to implement DT, focusing on successful experience of other companies, cooperating with them and using approaches proven by practice. This, together with a competition factor, can convince top management of DT expediency.
5. Top management commitment and project planning. DT implementation is a serious step in enterprise development, which requires significant financial costs and changes in production processes. The complexity of the project and uncertainty, risks, need for a clear plan and lack of transparency are serious obstacles to digitization [22]. DT adoption success also significantly depends on top management commitment [21].
6. Cooperation with scientific centers. To obtain a systematic view of the problems related to the implementation project, reduce financial costs and find qualified specialists, it is advisable to cooperate with research centers and universities [23].
7. Proof of Concept quality. Success of the project depends on the DT prototype - Proof of Concept (PoC). Not only does it confirm that the model is correct, but also helps developers to choose software and tools necessary for real-time simulations [24].
7. Adjustment of data collection and processing. To implement effective DT, it is necessary to solve the problems of data collection, processing and storage [17].
8. Building a communication network at the facility. If broadband Internet and 5G communication technologies are available, establishing data exchange between physical and digital object becomes simpler. Otherwise, it will be necessary to build a network of optical fiber cable networks at the facility [17, 25].
9. Corporate culture. Human capital is the most important resource for business transformation in Industry 4.0 and directly affects the success of this transformation. Specialists aspire to work in a business dominated by digital culture [26].
10. Personnel retraining. The implementation strategy significantly changes duties and functions of employees, so they must be highly qualified [13]. Successful DT operation will require lifelong learning, teamwork skills, as well as acceptance of innovations, changes and ideas [26].
11. Changes in the organization, management. There will be a need to adjust the organizational process at the enterprise, which requires time and effort [32]. It is also necessary to eliminate Data silos - a
phenomenon when different information systems are separated and cannot effectively work together. The reason is that different departments independently created databases long before DT implementation project, also some employees may be against sharing information with other departments [33].
12. Predictive maintenance level at the enterprise. One of the main purposes of DT is predictive maintenance. After DT implementation and adoption, time will be needed for its adjustment and its effective use during mundane work[34].
The calculation process is given in Tables 29. Table 2 is the IRM of identified factors. Table 3 shows the corresponding FRM, which is obtained by formula (3). Tables 4-9 display calculations of level partitioning, according to step 5 of the TISM algorithm (paragraph 3.1). To perform these calculations, a Python program was created, computations then were checked manually.
Table 2: IRM of identified factors
<table><tr><td></td><td>1</td><td>2</td><td>3</td><td>4</td><td>5</td><td>6</td><td>7</td><td>8</td><td>9</td><td>10</td><td>11</td><td>12</td><td>13</td></tr><tr><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td></tr><tr><td>2</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>1</td><td>0</td></tr><tr><td>3</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td></tr><tr><td>4</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>1</td><td>1</td></tr><tr><td>5</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>0</td></tr><tr><td>6</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td><td>1</td><td>0</td><td>0</td><td>0</td><td>1</td></tr><tr><td>7</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td></tr><tr><td>8</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>0</td><td>0</td><td>1</td><td>0</td><td>1</td></tr><tr><td>9</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td><td>0</td><td>0</td><td>1</td></tr><tr><td>10</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>0</td></tr><tr><td>11</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td></tr><tr><td>12</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td></tr><tr><td>13</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td></tr></table>
Table 3: FRM of identified factors
<table><tr><td></td><td>1</td><td>2</td><td>3</td><td>4</td><td>5</td><td>6</td><td>7</td><td>8</td><td>9</td><td>10</td><td>11</td><td>12</td><td>13</td><td>Driving power</td></tr><tr><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>13</td></tr><tr><td>2</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>12</td></tr><tr><td>3</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>12</td></tr><tr><td>4</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>12</td></tr><tr><td>5</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>9</td></tr><tr><td>6</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>9</td></tr><tr><td>7</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>7</td></tr><tr><td>8</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>7</td></tr><tr><td>9</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>1</td><td>7</td></tr><tr><td>10</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>4</td></tr><tr><td>11</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>1</td><td>1</td><td>4</td></tr><tr><td>12</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>2</td></tr><tr><td>13</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>0</td><td>1</td><td>1</td><td>2</td></tr><tr><td>Dependence</td><td>1</td><td>4</td><td>4</td><td>4</td><td>6</td><td>6</td><td>9</td><td>9</td><td>9</td><td>11</td><td>11</td><td>13</td><td>13</td><td></td></tr></table>
Then level partitioning is carried out to assign level to each element. Calculations are shown in tables 4-9.
Table 4: Iteration 1 of level partitioning
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>1</td><td>1,2,3,4,5,6,7,8,9,10,11,12,13</td><td>1</td><td>1</td><td></td></tr><tr><td>2</td><td>2,3,4,5,6,7,8,9,10,11,12,13</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>3</td><td>2,3,4,5,6,7,8,9,10,11,12,13</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>4</td><td>2,3,4,5,6,7,8,9,10,11,12,13</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>5</td><td>5,6,7,8,9,10,11,12,13</td><td>1,2,3,4,5,6</td><td>5,6</td><td></td></tr><tr><td>6</td><td>5,6,7,8,9,10,11,12,13</td><td>1,2,3,4,5,6</td><td>5,6</td><td></td></tr><tr><td>7</td><td>7,8,9,10,11,12,13</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>8</td><td>7,8,9,10,11,12,13</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>9</td><td>7,8,9,10,11,12,13</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>10</td><td>10,11,12,13</td><td>1,2,3,4,5,6,7,8,9,10,11</td><td>10,11</td><td></td></tr><tr><td>11</td><td>10,11,12,13</td><td>1,2,3,4,5,6,7,8,9,10,11</td><td>10,11</td><td></td></tr><tr><td>12</td><td>12,13</td><td>1,2,3,4,5,6,7,8,9,10,11,12,13</td><td>12,13</td><td>1</td></tr><tr><td>13</td><td>12,13</td><td>1,2,3,4,5,6,7,8,9,10,11,12,13</td><td>12,13</td><td>1</td></tr></table>
At the first iteration, level 1 was assigned to factors 12 and 13. According to step 5.2 of the TISM algorithm, since set $D$ is not null (it has factors from 1 to
11), level partitioning process is repeated, but without factors 12 and 13. Level partitioning continued until levels were assigned to each factor.
Table 5: Iteration 2 of level partitioning
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>1</td><td>1,2,3,4,5,6,7,8,9,10,11</td><td>1</td><td>1</td><td></td></tr><tr><td>2</td><td>2,3,4,5,6,7,8,9,10,11</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>3</td><td>2,3,4,5,6,7,8,9,10,11</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>4</td><td>2,3,4,5,6,7,8,9,10,11</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>5</td><td>5,6,7,8,9,10,11</td><td>1,2,3,4,5,6</td><td>5,6</td><td></td></tr><tr><td>6</td><td>5,6,7,8,9,10,11</td><td>1,2,3,4,5,6</td><td>5,6</td><td></td></tr><tr><td>7</td><td>7,8,9,10,11</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>8</td><td>7,8,9,10,11</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>9</td><td>7,8,9,10,11</td><td>1,2,3,4,5,6,7,8,9</td><td>7,8,9</td><td></td></tr><tr><td>10</td><td>10,11</td><td>1,2,3,4,5,6,7,8,9,10,11</td><td>10,11</td><td>2</td></tr><tr><td>11</td><td>10,11</td><td>1,2,3,4,5,6,7,8,9,10,11</td><td>10,11</td><td>2</td></tr></table>
Table 6: Iteration 3 of level partitioning
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>1</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>1</td><td>1</td><td></td></tr><tr><td>2</td><td>2, 3, 4, 5, 6, 7, 8, 9</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td></td></tr><tr><td>3</td><td>2, 3, 4, 5, 6, 7, 8, 9</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td></td></tr><tr><td>4</td><td>2, 3, 4, 5, 6, 7, 8, 9</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td></td></tr><tr><td>5</td><td>5, 6, 7, 8, 9</td><td>1, 2, 3, 4, 5, 6</td><td>5, 6</td><td></td></tr><tr><td>6</td><td>5, 6, 7, 8, 9</td><td>1, 2, 3, 4, 5, 6</td><td>5, 6</td><td></td></tr><tr><td>7</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr><tr><td>8</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr><tr><td>9</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr></table>

Table 7: Iteration 4 of level partitioning
<table><tr><td>Dt</td><td>Reachability Set Rt</td><td>Antecedent Set At</td><td>Rt∩At</td><td>Level</td></tr><tr><td>1</td><td>1,2,3,4,5,6</td><td>1</td><td>1</td><td></td></tr><tr><td>2</td><td>2,3,4,5,6</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>3</td><td>2,3,4,5,6</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>4</td><td>2,3,4,5,6</td><td>1,2,3,4</td><td>2,3,4</td><td></td></tr><tr><td>5</td><td>5,6</td><td>1,2,3,4,5,6</td><td>5,6</td><td>4</td></tr><tr><td>6</td><td>5,6</td><td>1,2,3,4,5,6</td><td>5,6</td><td>4</td></tr></table>
Table 8: Iteration 5 of level partitioning
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>1</td><td>1,2,3,4</td><td>1</td><td>1</td><td></td></tr><tr><td>2</td><td>2,3,4</td><td>1,2,3,4</td><td>2,3,4</td><td>5</td></tr><tr><td>3</td><td>2,3,4</td><td>1,2,3,4</td><td>2,3,4</td><td>5</td></tr><tr><td>4</td><td>2,3,4</td><td>1,2,3,4</td><td>2,3,4</td><td>5</td></tr></table>
Table 9: Iteration 6 of level partitioning
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>1</td><td>1</td><td>1</td><td>1</td><td>6</td></tr></table>
Level partitioning results are displayed in table 10.
Table 10: Level partitioning results (levels are highlighted with green)
<table><tr><td>Di</td><td>Reachability Set Ri</td><td>Antecedent Set Ai</td><td>Ri∩Ai</td><td>Level</td></tr><tr><td>13</td><td>12, 13</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13</td><td>12, 13</td><td>1</td></tr><tr><td>12</td><td>12, 13</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13</td><td>12, 13</td><td>1</td></tr><tr><td>10</td><td>10, 11</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11</td><td>10, 11</td><td>2</td></tr><tr><td>11</td><td>10, 11</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11</td><td>10, 11</td><td>2</td></tr><tr><td>7</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr><tr><td>8</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr><tr><td>9</td><td>7, 8, 9</td><td>1, 2, 3, 4, 5, 6, 7, 8, 9</td><td>7, 8, 9</td><td>3</td></tr><tr><td>5</td><td>5, 6</td><td>1, 2, 3, 4, 5, 6</td><td>5, 6</td><td>4</td></tr><tr><td>6</td><td>5, 6</td><td>1, 2, 3, 4, 5, 6</td><td>5, 6</td><td>4</td></tr><tr><td>2</td><td>2, 3, 4</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td>5</td></tr><tr><td>3</td><td>2, 3, 4</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td>5</td></tr><tr><td>4</td><td>2, 3, 4</td><td>1, 2, 3, 4</td><td>2, 3, 4</td><td>5</td></tr><tr><td>1</td><td>1</td><td>1</td><td>1</td><td>6</td></tr></table>
Table 10 displays a digraph (Figure 2), in which we highlight 3 components.
- External factors (green color; 6-th and 5-th level);
- Factors, that describe the stage of DT implementation (orange; 4-th and 3-rd level); - factors, that describe the stage of DT integration into enterprise work (blue; 2-nd, 1-st level).
The enterprise cannot influence external factors, that why they are located at lower levels of the scheme. The following levels reflect the "chronology" of digitalization from DT development to fully-fledged implementation at the enterprise.

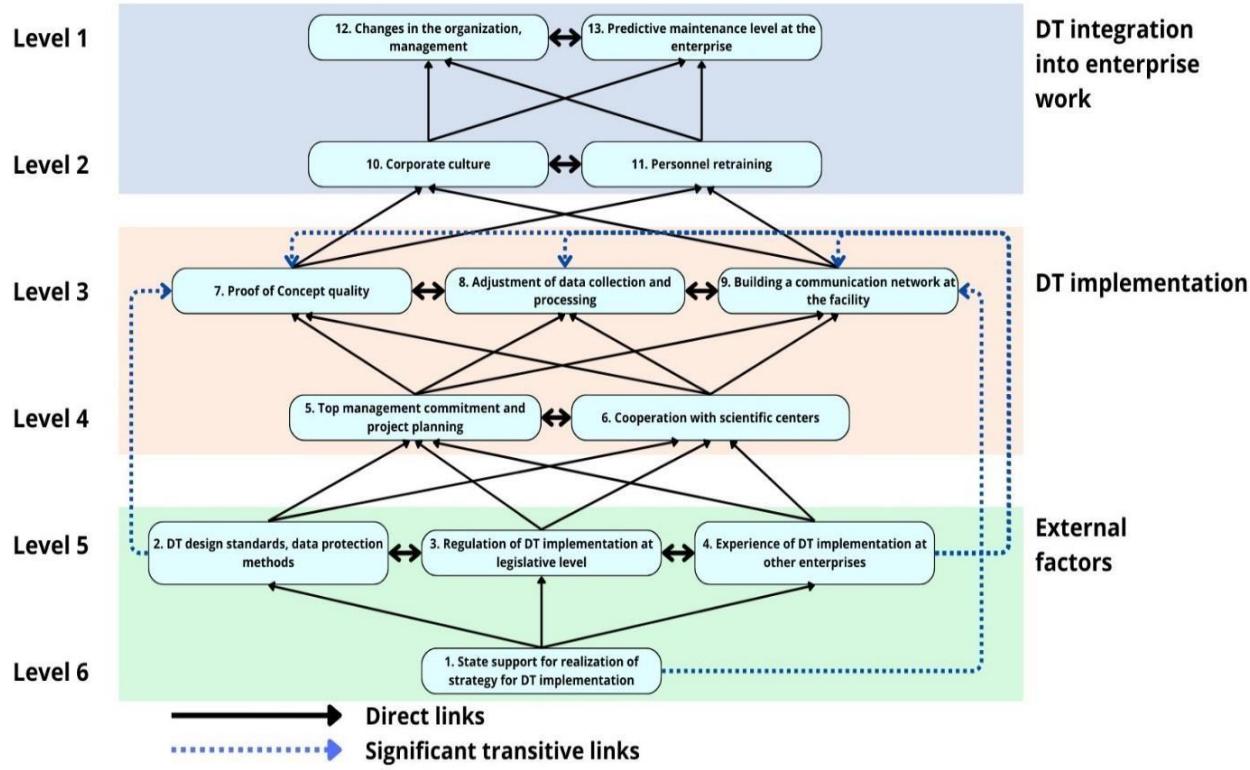 Fig. 2: Digraph, illustrating TISM model of factors that influence DT implementation Based on the digraph, an Interpretive matrix, which explains interconnections between factors, is built (Table 11).
Table 11: Interpretive matrix
<table><tr><td>No</td><td>Factors</td><td>Influence</td><td>Interpretation</td></tr><tr><td>1</td><td>State support for realization of strategy for DT implementation</td><td>2, 3, 4, 9</td><td>The state determines the following aspects: amount of financial support for enterprises that switch to DT, quality of legislative regulation of this technology and standards, as well as overcoming corruption. These factors accelerate DT adoption on the market so that it will be easier for our enterprise to implement it. In particular, the state could provide 5G coverage, which will significantly simplify the building of communication network at the facility.</td></tr><tr><td>2</td><td>DT design standards, data protection methods</td><td>3, 4, 5, 6, 7</td><td>The standards for DT design will contribute to data protection methods development and formation of relevant legislation, as well as give companies and scientific centers a "common language", opening opportunities for cooperation. This will help top management to form a better plan and develop a high-quality Proof of Concept.</td></tr><tr><td>3</td><td>Regulation of DT implementation at legislative level</td><td>2, 4, 5, 6</td><td>Legislation supports DT standards development and reduces uncertainty. Under these conditions, it will be easier for the enterprise to create a plan of DT implementation, as well as establish cooperation with colleagues and scientists.</td></tr><tr><td>4</td><td>Experience of DT implementation at other enterprises</td><td>2, 3, 5, 6, 7, 8, 9</td><td>Examples of successful digitalization and other enterprises experience, as well as competition factor, could convince the top management of DT implementation expediency. Experience exchange will allow the enterprise to develop high-quality Proof of Concept, data acquisition and processing system, communication network.</td></tr><tr><td>5</td><td>Top management commitment and project planning</td><td>6, 7, 8, 9</td><td>The entire further DT development process depends on the top management commitment and project plan. A sound plan would also include collaboration with academics.</td></tr><tr><td>6</td><td>Cooperation with scientific centers</td><td>5, 7, 8, 9</td><td>Cooperation with research centers allows us to plan the DT effective development, identify barriers to digital transformation at a specific enterprise and key factors. This would also motivate the management.</td></tr><tr><td>7</td><td>Proof of Concept quality</td><td>8, 9, 10, 11</td><td>Proof of Concept is a DT prototype, created to confirm the adequacy of physical system models, so that it determines further development success, and therefore staff training quality. In the process, it may be necessary to improve the communication network and data acquisition system.</td></tr><tr><td>8</td><td>Adjustment of data collection and processing</td><td>7, 9</td><td>Data acquisition, processing and storage systems provide the DT with all the information. Hence, it determines DT prototype quality and its further development.</td></tr><tr><td>9</td><td>Building a communi-cation network at the facility</td><td>7, 8, 10, 11</td><td>5G/Wired network coverage is critical for DT development, as it determines whether it will be convenient for employees to switch to a new system.</td></tr><tr><td>10</td><td>Corporate culture</td><td>11, 12, 13</td><td>Effective use of DT, business process change begins with a corporate culture that accepts new information technologies and adapts to them.</td></tr><tr><td>11</td><td>Personnel retraining</td><td>10, 12, 13</td><td>Only qualified employees will be able to work with the DT at the enterprise. This will create the necessary corporate "digital culture" and allow to adopt the innovation.</td></tr><tr><td>12</td><td>Changes in the organization, management</td><td>13</td><td>After DT development at the enterprise, reorganization of activities is inevitable: new duties, positions, requirements and change of corporate rules. Such measures will define the effectiveness of DT use.</td></tr><tr><td>13</td><td>Predictive maintenance level at the enterprise</td><td>12</td><td>The ability of DT models to conduct scenario analysis will accelerate the transition to a new organizational level at the enterprise.</td></tr></table>
### b) Application of the MICMAC method for factor classification
Based on the TISM method results, MICMAC is used to classify the identified factors. Driving power and Dependence values from table 3 for each factor are displayed in the Cartesian coordinate system. Since we consider 13 elements, the threshold for classification was 6.5 (dashed lines). The results are shown in Figure 3.
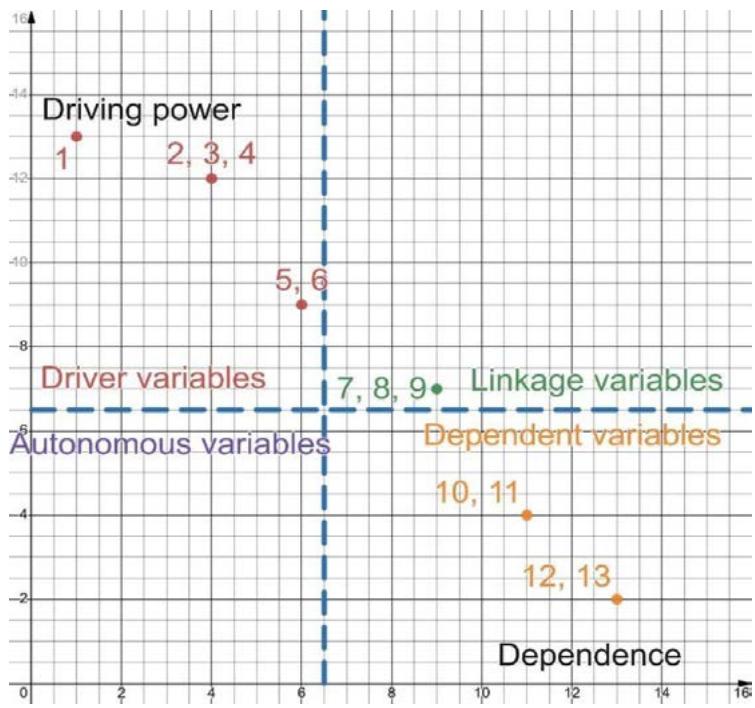 Fig. 3: Elements classification via MICMAC-method
From Figure 3 we have the following classification.
- Driver variables: factors 1, 2, 3, 4, 5, 6;
- Linkage variables: factors 7, 8, 9;
- Dependent variables: factors 10, 11, 12, 13;
- Autonomous variables are absent.
MICMAC results confirmed that all identified factors play an active role in system development and/or are significantly influenced by it.
All external factors were found to be driver variables (state support for realization of strategy for DT implementation, other companies' experience, DT design standards, legislative regulation), as well as top management commitment, project planning and cooperation with scientific centers. The algorithm attributed to linkage variables the factors of data collection and processing system adjustment, Proof of Concept and building a communication network. They have a great influence on system development; however, they are also greatly influenced by other factors. Corporate culture, personnel retraining, changes in the organization, management, and the level of predictive maintenance at the enterprise are considered to be dependent factors.
## V. CONCLUSIONS
Industry 4.0 technologies, especially cyberphysical systems with a DT, open up unique opportunities for companies to increase efficiency, bring business processes management to a new level, and improve the quality of products and services. This paper aims to develop a DT implementation strategy to support the guaranteed functioning of a cyber-physical system in the form of enterprise in the reconstruction of post-war Ukraine. To solve this problem, it is essential to identify and prioritize the factors that affect the quality of the DT implementation at the enterprise.
The study identified 13 factors of that kind. Using the TISM method, they were organized into a scheme with 6-level digraph. External factors are located at two lower levels: state support for the realization of strategy for DT implementation, availability of design standards and data protection methods, legislative regulation of DT and other companies' experience of DT adoption. The factors at higher levels are the consequences of external factors. Two middle levels contain factors that determine the quality of DT implementation strategy process. Two upper levels contain factors that determine the success of transition to a new information system after DT development. Next, the factors were classified by the MICMAC method. All external factors, as well as top management commitment and project planning, cooperation with scientific centers are classified as driver variables.
Finally, the prospects for further domestic DT industry development depend on financial and legislative support of the state, the promotion of DT design standards formation and data protection methods, as well as improvement of legislation which will regulate their implementation. These factors should be the key goals of strategies to support the development of Industry 4.0 in Ukraine.
Generating HTML Viewer...
References
33 Cites in Article
(2022). Ukraine Rapid Damage and Needs Assessment.
Nataliya Pankratova,Igor Golinko (2023). Approach to Development of Digital Twin Model for Cyber-Physical System in Conditions of Conceptual Uncertainty.
Nataliya Pankratova,Igor Golinko (2023). Development of Digital Twins to Support the Functioning of Cyber-physical Systems.
N Pankratova,K Grishyn,V Barilko (2023). Digital twins: stages of concept development, areas of use, prospects.
P Raj,C Surianarayanan (2020). Digital twin: The industry use cases.
Chao Liang,Ji Wang,Lijun Sun,Chunyang Ji (2023). Research and Application of Digital Twin Model for Gear Box Operation and Maintenance.
Rashik Parmar,Aija Leiponen,Llewellyn Thomas (2020). Building an organizational digital twin.
S Sushil (2012). Interpreting the Interpretive Structural Model.
V Conclusions (2020). Conclusions.
Ahmad Bakhtari,Vineet Kumar,Mohammad Waris,Cesar Sanin,Edward Szczerbicki (2020). Industry 4.0 Implementation Challenges in Manufacturing Industries: an Interpretive Structural Modelling Approach.
Angira Sharma,Edward Kosasih,Jie Zhang,Alexandra Brintrup,Anisoara Calinescu (2022). Digital Twins: State of the art theory and practice, challenges, and open research questions.
Haien Ding (2022). What kinds of countries have better innovation performance?–A country-level fsQCA and NCA study.
Andrea Benešová,Jiří Tupa (2017). Requirements for Education and Qualification of People in Industry 4.0.
Tariq Masood,Paul Sonntag (2020). Industry 4.0: Adoption challenges and benefits for SMEs.
R D'amico,S Addepalli,J Erkoyuncu (2023). Industrial Insights on Digital Twins in Manufacturing: Application Landscape, Current Practices, and Future Needs.
K Wang,Y Wang,Y Li,X Fan,S Xiao,L Hu (2022). A review of the technology standards for enabling digital twin.
Maggie Mashaly (2021). Connecting the Twins: A Review on Digital Twin Technology & its Networking Requirements.
D Holmes,M Papathanasaki,L Maglaras,M Ferrag,S Nepal,H Janicke (2021). Digital Twins and Cyber Security -solution or challenge?.
Binyu Lei,Patrick Janssen,Jantien Stoter,Filip Biljecki (2023). Challenges of urban digital twins: A systematic review and a Delphi expert survey.
Rory Baxter (1985). Digital reveals its five-year plan for cim.
R Ruben,C Rajendran,R Ram,F Kouki,H Alshahrani,M Assiri (2023). Analysis of barriers affecting Industry 4.0 implementation: An interpretive analysis using Total Interpretive Structural Modelling (TISM) and Fuzzy MICMAC.
Maria Mogos,Ragnhild Eleftheriadis,Odd Myklebust (2019). Enablers and inhibitors of Industry 4.0: results from a survey of industrial companies in Norway.
B Neuhierl,T Eppinger,J-W Handgraaf (2023). Combining computational chemistry and 3D CFD to simulate CO2 Membrane separation for Carbon Capture.
Martin Tomczyk,Hendrik Van Der Valk (2022). Digital Twin Paradigm Shift: The Journey of the Digital Twin Definition.
Đorđe Gojković (2023). Međunarodno pravo i distributivna pravda - slučaj Antarktika.
T Karaboğa (2023). The Impact of Industry 4.0 on Talent Management Practices: A Systematic Review.
J Warfield,A Cardenas (1994). Iowa State University Digital Press.
Aswathy Sreenivasan,Suresh Ma,Ateekh Rehman,Shanthi Muthuswamy (2023). Assessment of Factors Influencing Agility in Start-Ups Industry 4.0.
Pedro Senna,Luís Ferreira,Ana Barros,Jaime Bonnín Roca,Vanessa Magalhães (2022). Prioritizing barriers for the adoption of Industry 4.0 technologies.
Bishal Sarkar,Ravi Shankar (2021). Understanding the barriers of port logistics for effective operation in the Industry 4.0 era: Data-driven decision making.
Gunther Schmidt,Thomas Ströhlein (1993). Relations and Graphs.
Andrea Benešová,Martin Hirman,František Steiner,Jiří Tupa (2019). Determination of Changes in Process Management within Industry 4.0.
No ethics committee approval was required for this article type.
Data Availability
Not applicable for this article.
How to Cite This Article
Nataliya Pankratova. 2026. \u201cThe Strategy of Digital twin Implementation at the Cyber-Phisical Enterprises\u201d. Global Journal of Computer Science and Technology - H: Information & Technology GJCST-H Volume 24 (GJCST Volume 24 Issue H1): .
Explore published articles in an immersive Augmented Reality environment. Our platform converts research papers into interactive 3D books, allowing readers to view and interact with content using AR and VR compatible devices.
Your published article is automatically converted into a realistic 3D book. Flip through pages and read research papers in a more engaging and interactive format.
The strategy of digital twin (DT) implementation at the cyber-physical enterprises is proposed, which is due to the need for high-quality and effective reconstruction of Ukraine. The TISM and MICMAC methods are used to study the factors that influence the strategy of DT implementation to support the guaranteed functioning of a cyber-physical system. 13 main factors, that determine strategy success, were identified, and a model of strategy realization was built in the form of a six-level interaction diagram (digraph). The factors are classified by influence and dependence. The substantiated conclusion is that the state support of DT implementation strategy, the availability of design standards, data protection methods, legislative regulation and implementation experience by other enterprises are key factors to the success of strategy for DT implementation at the enterprise.
Our website is actively being updated, and changes may occur frequently. Please clear your browser cache if needed. For feedback or error reporting, please email [email protected]
Thank you for connecting with us. We will respond to you shortly.